Question: 4. When using ftp, each character, ch, that is typed on the remote machine is copied and sent to display on the local machine.
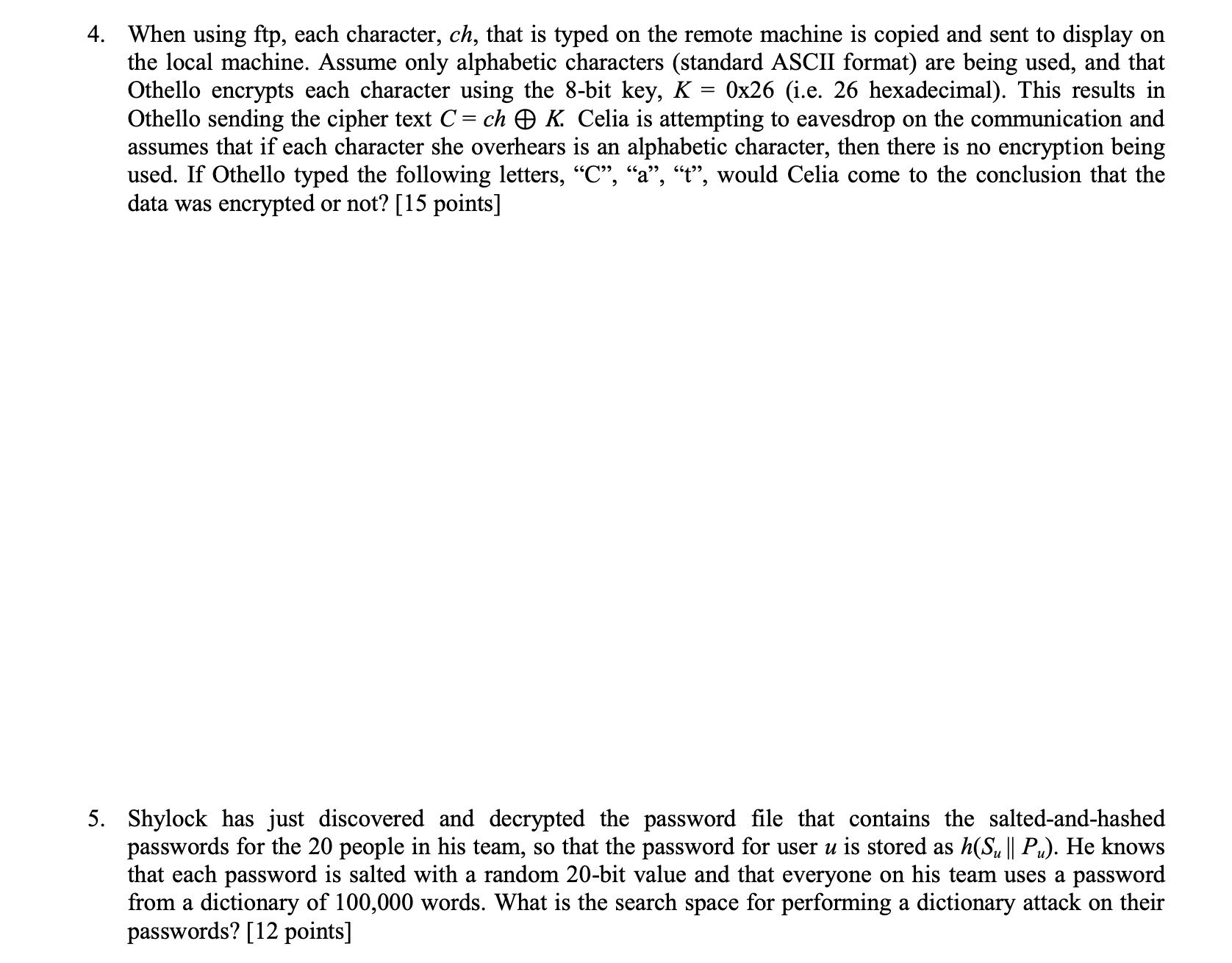
4. When using ftp, each character, ch, that is typed on the remote machine is copied and sent to display on the local machine. Assume only alphabetic characters (standard ASCII format) are being used, and that Othello encrypts each character using the 8-bit key, K = 0x26 (i.e. 26 hexadecimal). This results in Othello sending the cipher text C = ch K. Celia is attempting to eavesdrop on the communication and assumes that if each character she overhears is an alphabetic character, then there is no encryption being used. If Othello typed the following letters, "C", "a", "t", would Celia come to the conclusion that the data was encrypted or not? [15 points] 5. Shylock has just discovered and decrypted the password file that contains the salted-and-hashed passwords for the 20 people in his team, so that the password for user u is stored as h(Su || Pu). He knows that each password is salted with a random 20-bit value and that everyone on his team uses a password from a dictionary of 100,000 words. What is the search space for performing a dictionary attack on their passwords? [12 points]
Step by Step Solution
3.30 Rating (153 Votes )
There are 3 Steps involved in it
4 In the given scenario Othello encrypts each character using the 8bit key K 0x26 Celia is attemptin... View full answer

Get step-by-step solutions from verified subject matter experts


