Question: 4{?,il 41% & 12:26 Lab 1 - Read-only Read Only - You can't save changes to t... INCS 775 Da ta Center Security Summer 2018
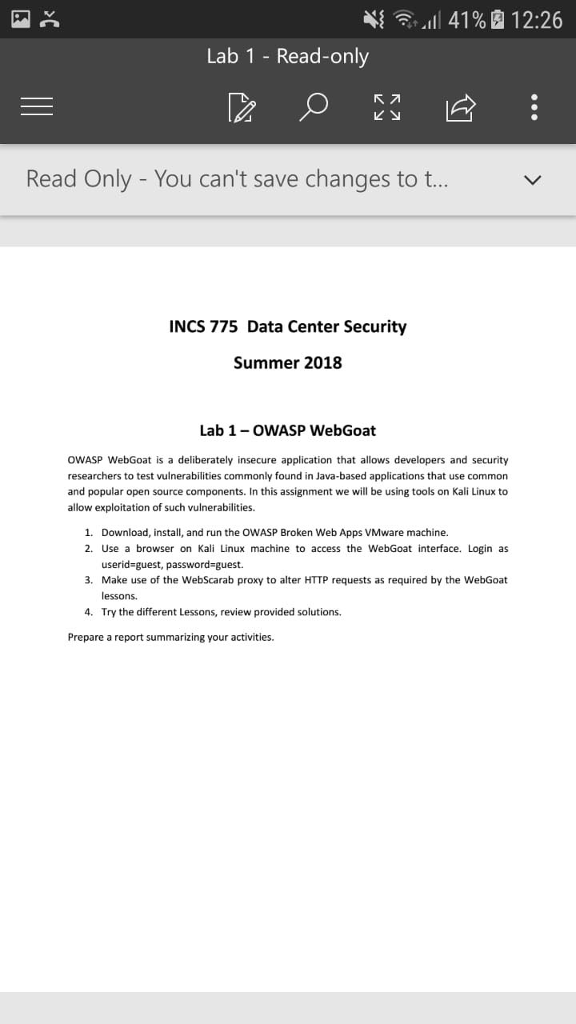
4{?,"il 41% & 12:26 Lab 1 - Read-only Read Only - You can't save changes to t... INCS 775 Da ta Center Security Summer 2018 Lab 1- OWASP WebGoat OWASP WebGoat is a deliberately insecure application that allows developers and security researchers to test vulnerabilities commonly found in Java-based applications that use commorn and popular open source components. In this assignment we will be using tools on Kali Linux to allow exploitation of such vulnerabilities. 1. Download, install, and run the OWASP Broken Web Apps VMware machine. 2. Use a browser on Kali Linux machine to access the WebGoat interface. Login as userid-guest, password-guest. 3. Make use of the WebScarab proxy to alter HTTP requests as required by the WebGoat essons Try the different Lessons, review provided solutions. 4. Prepare a report summarizing your activities. 4{?,"il 41% & 12:26 Lab 1 - Read-only Read Only - You can't save changes to t... INCS 775 Da ta Center Security Summer 2018 Lab 1- OWASP WebGoat OWASP WebGoat is a deliberately insecure application that allows developers and security researchers to test vulnerabilities commonly found in Java-based applications that use commorn and popular open source components. In this assignment we will be using tools on Kali Linux to allow exploitation of such vulnerabilities. 1. Download, install, and run the OWASP Broken Web Apps VMware machine. 2. Use a browser on Kali Linux machine to access the WebGoat interface. Login as userid-guest, password-guest. 3. Make use of the WebScarab proxy to alter HTTP requests as required by the WebGoat essons Try the different Lessons, review provided solutions. 4. Prepare a report summarizing your activities
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


