Question: 5 1 point How does a pass - the - hash attack work? By using stolen hashes of user passwords to authenticate to a system
point
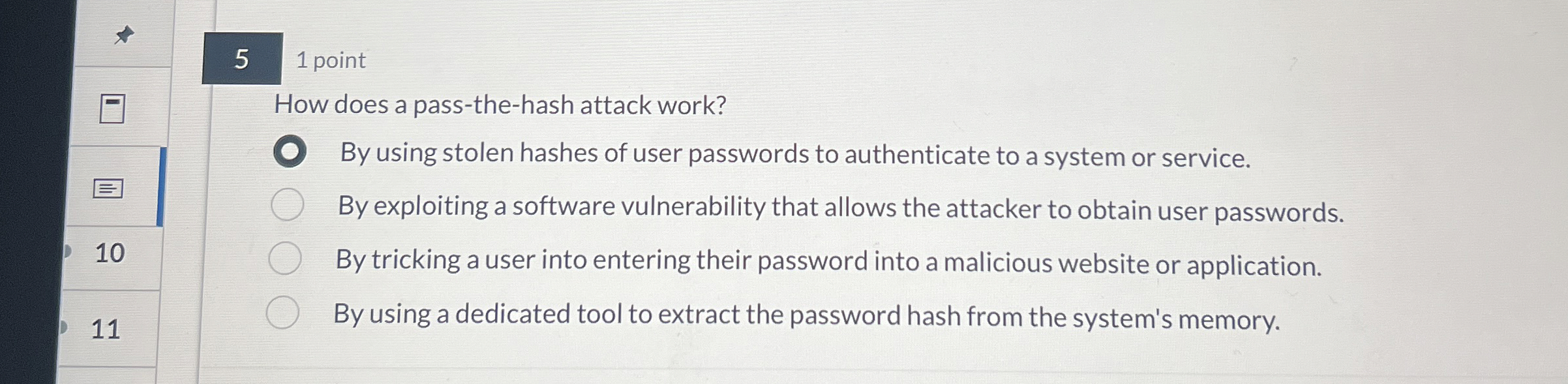
How does a passthehash attack work?
By using stolen hashes of user passwords to authenticate to a system or service.
By exploiting a software vulnerability that allows the attacker to obtain user passwords.
By tricking a user into entering their password into a malicious website or application.
By using a dedicated tool to extract the password hash from the system's memory.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


