5. XYZ Foundation (XYZ) is a not for profit fund-raising entity for a large company. XYZ...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
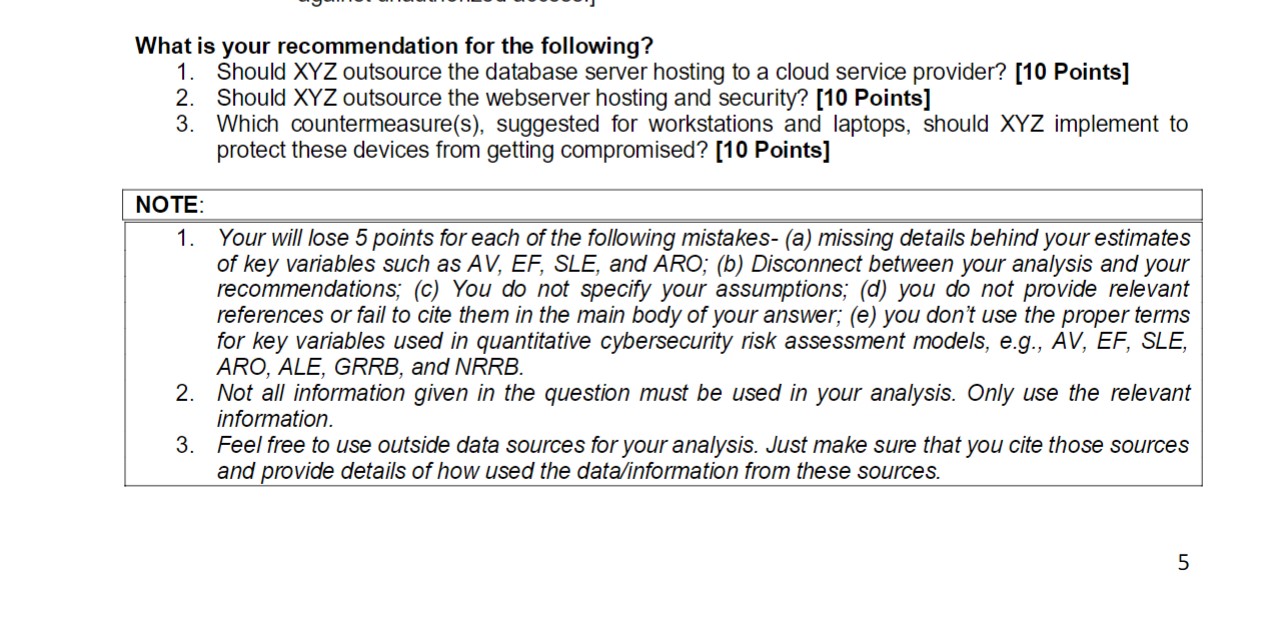
5. XYZ Foundation (XYZ) is a not for profit fund-raising entity for a large company. XYZ has assets of over $1 billion in cash, stock, and property. They currently have a donor base of 73250 doners and this is expected to grow at the rate of 600 new doners/year. Although they raise money for a public entity, they are a private entity and are not required to publish financial information or donor records. The release of any donor information could be very damaging to the reputation of XYZ and could have a critical effect on future donations. In addition, their books are private and information of what they own could be detrimental as well. Based on this, XYZ has requested that you perform a cybersecurity assessment, focusing on threats to their workstations, laptops, and webserver. These assets are described as follows. Webserver- This server is used to host information relevant to XYZ's fund raising campaigns and collect contributions from doners. The website allows doners see the details of prior fund raising campaigns, browse through current campaigns, and see plans for forthcoming campaigns. First time visitors have an option to open an account with XYZ and opt-in for a monthly newsletter. The website is active 24/7 and any disruption can result in a loss of $10K to $50K per hour. Loss of reputation resulting from each disruption can result in at least 10 current donners closing their accounts and the rate of new account openings slow down by 10% for the remaining year. The webserver must be protected against website defacement and cross site scripting (XSS) attacks. In XSS attacks, a vulnerable website or web applications is injected with malicious code, which then infect the devices (e.g., laptops, workstations, tablets, mobile phones etc.) of unsuspecting users who visits that infected website. Database Server- This server is used to collect, store, manage, and maintain doner information. Currently there are 73250 doners registered with XYZ and all their data is stored in this database. This includes information on their preferred method to donate online (e.g., credit/debit card details, PayPal, Venmo etc.), their name, date of birth, mailing address, and the list of causes that the doner is interested in donating to. The security of this data must be following Sarbanes-Oxley, SEC rule 30, part of Regulation S-P (17 CFR 248.30), and Gramm-Leach-Bliley Act. The database server also hosts employee database that has PII, financial data and tax data for its 230 employees. This server must be protected against data breach. Employee Workstations- XYZ has 200 laptops and 50 workstations that the employees use to do their jobs. The laptops and workstations run on Windows 10. These devices are classified as follows- O Administrative- All 50 workstations are used by the administrative staff (e.g., accounting, HR, MIS). Applications running on these workstations are limited to only that software which is needed for various admin functions. These workstations do not have access to the Database or Web Servers. If compromised, XYZ expects to spend $500 per incident to recover from the incident. O Laptops- Laptops are used by senior management, and staff responsible for promoting current and future campaigns, finding spokespersons for these campaigns, public relations management, soliciting large doners etc. These laptops have access to both the webserver and the database server. They also include data on potential spokespersons, contacts in public relations industry, potential doners, details of current and future fund raising campaigns. If compromised, then each incident could result in a financial impact of $5k- $20k for XYZ. These devices must be protected against- i. Phishing emails. ii. Malware infections. iii. Malicious/infected websites. iv. Unauthorized access. Security Audit: The following are the key issues found through network scans, observations, and interviews: Use of Public IP Addresses for all the networking devices, workstations, and server residing on the LAN. No Firewall to segregate the XYZ LAN into DMZ and internal network. This means that all XYZ servers and workstations can be scanned by anyone from remote locations. 4 LAN/WAN issues- XYZ has two locations that are both connected to the Internet. All communications between the sites happens over the Internet. In this case the WAN is based on public networks. This is common with smaller companies, as it keeps the cost of interconnection down. The head office has a single LAN environment that contains 2 application servers (Windows Server 2020), one Web Server (IIS 7.5), 50 workstations (Windows 10), a database server (Oracle Database 12c release 1), 4 HP LaserJet 1320 printers, and networking equipment. All equipment is on the same core switch. A single router is used to connect the LAN to the Internet, as well as the remote office. XYZ had little to no documented IT procedures or policies. As a result, everything is done 'ad hoc,' which leads to systems that are hard to administer effectively. For example, on XYZ servers, there was no consistency on how they were setup. A policy would have step-by-step procedures detailing how to disable guest accounts and enforce password standards. No such document existed and some servers had guest accounts and weak passwords. The databases utilized by XYZ, which hold their critical information, have poor password, and account management. Many passwords were either 'password' or the same as the account name. Furthermore, several default and guest accounts were active, some with extended privileges. XYZ systems are running free versions of anti-malware that is not updated regularly. While operating systems are patched automatically and on time, XYZ is always behind on patching its applications. Countermeasures [Costs, Effectiveness]- A. Database Server- Outsource database server hosting and security to cloud service provider. [$20K/year, 98% effective in protecting against data breach incidents.] B. Webserver-Outsource webserver hosting and security services. [$10K/year, 99% effective against cyberattacks on web server, applications, and pages.] C. Workstations & Laptops- a. Mandatory cybersecurity training (that includes simulated phishing attacks) every quarter. [$100K/year, 90% effective against social engineering attacks such as phishing emails] b. Subscribe to anti-malware for all workstations, laptops, and employee's personal devices with auto-updates. [$5K; 95% effective against malware infections] C. Enforce secure browsing on employees' personal devices used to connect to XYZ's servers. [$5K., 98% effective against malicious/infected websites] d. Enforce password policies that require employees to have strong passwords, frequently change passwords, and penalize them for sharing passwords. [$5K/year, 90% effective against unauthorized access.] What is your recommendation for the following? 1. Should XYZ outsource the database server hosting to a cloud service provider? [10 Points] 2. Should XYZ outsource the webserver hosting and security? [10 Points] 3. Which countermeasure(s), suggested for workstations and laptops, should XYZ implement to protect these devices from getting compromised? [10 Points] NOTE: 1. Your will lose 5 points for each of the following mistakes- (a) missing details behind your estimates of key variables such as AV, EF, SLE, and ARO; (b) Disconnect between your analysis and your recommendations; (c) You do not specify your assumptions; (d) you do not provide relevant references or fail to cite them in the main body of your answer; (e) you don't use the proper terms for key variables used in quantitative cybersecurity risk assessment models, e.g., AV, EF, SLE, ARO, ALE, GRRB, and NRRB. 2. Not all information given in the question must be used in your analysis. Only use the relevant information. 3. Feel free to use outside data sources for your analysis. Just make sure that you cite those sources and provide details of how used the data/information from these sources. 5 5. XYZ Foundation (XYZ) is a not for profit fund-raising entity for a large company. XYZ has assets of over $1 billion in cash, stock, and property. They currently have a donor base of 73250 doners and this is expected to grow at the rate of 600 new doners/year. Although they raise money for a public entity, they are a private entity and are not required to publish financial information or donor records. The release of any donor information could be very damaging to the reputation of XYZ and could have a critical effect on future donations. In addition, their books are private and information of what they own could be detrimental as well. Based on this, XYZ has requested that you perform a cybersecurity assessment, focusing on threats to their workstations, laptops, and webserver. These assets are described as follows. Webserver- This server is used to host information relevant to XYZ's fund raising campaigns and collect contributions from doners. The website allows doners see the details of prior fund raising campaigns, browse through current campaigns, and see plans for forthcoming campaigns. First time visitors have an option to open an account with XYZ and opt-in for a monthly newsletter. The website is active 24/7 and any disruption can result in a loss of $10K to $50K per hour. Loss of reputation resulting from each disruption can result in at least 10 current donners closing their accounts and the rate of new account openings slow down by 10% for the remaining year. The webserver must be protected against website defacement and cross site scripting (XSS) attacks. In XSS attacks, a vulnerable website or web applications is injected with malicious code, which then infect the devices (e.g., laptops, workstations, tablets, mobile phones etc.) of unsuspecting users who visits that infected website. Database Server- This server is used to collect, store, manage, and maintain doner information. Currently there are 73250 doners registered with XYZ and all their data is stored in this database. This includes information on their preferred method to donate online (e.g., credit/debit card details, PayPal, Venmo etc.), their name, date of birth, mailing address, and the list of causes that the doner is interested in donating to. The security of this data must be following Sarbanes-Oxley, SEC rule 30, part of Regulation S-P (17 CFR 248.30), and Gramm-Leach-Bliley Act. The database server also hosts employee database that has PII, financial data and tax data for its 230 employees. This server must be protected against data breach. Employee Workstations- XYZ has 200 laptops and 50 workstations that the employees use to do their jobs. The laptops and workstations run on Windows 10. These devices are classified as follows- O Administrative- All 50 workstations are used by the administrative staff (e.g., accounting, HR, MIS). Applications running on these workstations are limited to only that software which is needed for various admin functions. These workstations do not have access to the Database or Web Servers. If compromised, XYZ expects to spend $500 per incident to recover from the incident. O Laptops- Laptops are used by senior management, and staff responsible for promoting current and future campaigns, finding spokespersons for these campaigns, public relations management, soliciting large doners etc. These laptops have access to both the webserver and the database server. They also include data on potential spokespersons, contacts in public relations industry, potential doners, details of current and future fund raising campaigns. If compromised, then each incident could result in a financial impact of $5k- $20k for XYZ. These devices must be protected against- i. Phishing emails. ii. Malware infections. iii. Malicious/infected websites. iv. Unauthorized access. Security Audit: The following are the key issues found through network scans, observations, and interviews: Use of Public IP Addresses for all the networking devices, workstations, and server residing on the LAN. No Firewall to segregate the XYZ LAN into DMZ and internal network. This means that all XYZ servers and workstations can be scanned by anyone from remote locations. 4 LAN/WAN issues- XYZ has two locations that are both connected to the Internet. All communications between the sites happens over the Internet. In this case the WAN is based on public networks. This is common with smaller companies, as it keeps the cost of interconnection down. The head office has a single LAN environment that contains 2 application servers (Windows Server 2020), one Web Server (IIS 7.5), 50 workstations (Windows 10), a database server (Oracle Database 12c release 1), 4 HP LaserJet 1320 printers, and networking equipment. All equipment is on the same core switch. A single router is used to connect the LAN to the Internet, as well as the remote office. XYZ had little to no documented IT procedures or policies. As a result, everything is done 'ad hoc,' which leads to systems that are hard to administer effectively. For example, on XYZ servers, there was no consistency on how they were setup. A policy would have step-by-step procedures detailing how to disable guest accounts and enforce password standards. No such document existed and some servers had guest accounts and weak passwords. The databases utilized by XYZ, which hold their critical information, have poor password, and account management. Many passwords were either 'password' or the same as the account name. Furthermore, several default and guest accounts were active, some with extended privileges. XYZ systems are running free versions of anti-malware that is not updated regularly. While operating systems are patched automatically and on time, XYZ is always behind on patching its applications. Countermeasures [Costs, Effectiveness]- A. Database Server- Outsource database server hosting and security to cloud service provider. [$20K/year, 98% effective in protecting against data breach incidents.] B. Webserver-Outsource webserver hosting and security services. [$10K/year, 99% effective against cyberattacks on web server, applications, and pages.] C. Workstations & Laptops- a. Mandatory cybersecurity training (that includes simulated phishing attacks) every quarter. [$100K/year, 90% effective against social engineering attacks such as phishing emails] b. Subscribe to anti-malware for all workstations, laptops, and employee's personal devices with auto-updates. [$5K; 95% effective against malware infections] C. Enforce secure browsing on employees' personal devices used to connect to XYZ's servers. [$5K., 98% effective against malicious/infected websites] d. Enforce password policies that require employees to have strong passwords, frequently change passwords, and penalize them for sharing passwords. [$5K/year, 90% effective against unauthorized access.] What is your recommendation for the following? 1. Should XYZ outsource the database server hosting to a cloud service provider? [10 Points] 2. Should XYZ outsource the webserver hosting and security? [10 Points] 3. Which countermeasure(s), suggested for workstations and laptops, should XYZ implement to protect these devices from getting compromised? [10 Points] NOTE: 1. Your will lose 5 points for each of the following mistakes- (a) missing details behind your estimates of key variables such as AV, EF, SLE, and ARO; (b) Disconnect between your analysis and your recommendations; (c) You do not specify your assumptions; (d) you do not provide relevant references or fail to cite them in the main body of your answer; (e) you don't use the proper terms for key variables used in quantitative cybersecurity risk assessment models, e.g., AV, EF, SLE, ARO, ALE, GRRB, and NRRB. 2. Not all information given in the question must be used in your analysis. Only use the relevant information. 3. Feel free to use outside data sources for your analysis. Just make sure that you cite those sources and provide details of how used the data/information from these sources. 5
Expert Answer:

Related Book For 

Cost Management Measuring Monitoring and Motivating Performance
ISBN: 978-0470769423
2nd edition
Authors: Leslie G. Eldenburg, Susan K. Wolcott
Posted Date:
Students also viewed these algorithms questions
-
Read the case study "Southwest Airlines," found in Part 2 of your textbook. Review the "Guide to Case Analysis" found on pp. CA1 - CA11 of your textbook. (This guide follows the last case in the...
-
How does HCA's financial strategy affect its product-market strategy? How important is finance to HCA and in what ways? (Please no plagiarism) Hospital Corporation of America (A) In January of 1982...
-
In Exercises use the Ratio Test to determine the convergence or divergence of the series. 00 n=1 n! n3n
-
Calculate the focal length of a lens in water, given that the index of refraction of the lens is nlens = 1.52 and its focal length in air is 25.0 cm. A. 57.8 cm B. 66.0 cm C. 91.0 cm D. 104 cm
-
A job requiring 42 minutes was speeded up. It was completed in 38 minutes. What percent of the original time was saved?
-
The following data pertain to water pressure at various depths below sea level: (a) Fit an exponential curve. (b) Use the result obtained in part (a) to estimate the mean pressure at a depth of...
-
Go to the Structural Styles section and create a style rule that sets the background color of the browser window to rgb(173, 189, 227). Create a style rule for the body element that sets the...
-
I think value pricing should be used since we are increasing product and service benefits while maintaining a reasonable price. Some products, price influences consumers perception of overall quality...
-
Sofia Lofts case, but under a new set of assumptions on page 11 of the case. First re-read the Sofia Lofts case, then click here to download the new page 11. Specifically, you are to write up a brief...
-
Factor. 2 u + 16u+64 M X
-
1. Calculate the equilibrium constant, Keq, for the following reaction at 25 C, if [NO]eq = 0.106 M, [02]eq = 0.122 M and [NO2]eq = 0.129 M. 2 NO (g) + O2 (g) 2 NO2 (g) 2. Find the equilibrium...
-
LO 1 LO 1 11. Valuing Preferred Stock E-Eyes.com has a new issue of preferred stock it calls 20/20 preferred. The stock will pay a $20 dividend per year, but the first dividend will not be paid until...
-
4. Solve the following systems: (a) x + x2 + 2x3 = 8 - -x1 2x + 3x3 1 3x17x2 + 4x3 = 10 (b) x+y+z=3 4x + 4y + 4z = 7 3xy + 2z = 5
-
Shown below is the block diagram of the datapath that was used for Greatest Common Divisor (GCD) calculation in the lab task. 19 else selA SelB LoadA LoadB AeqB else AltB Loadgcd done Y = A-B; end if...
-
Consider the two regions in the state of Central Ulna, Dockside and Lakeside. In both of these communities, household workers produce anchors and flour. Dockside workers: Produce 16 anchors or 4...
-
o Find the torque must be applied the limk-2 to retain the static equilibrium (Both graphical and analytical) o Hint: Use superposition A OA = 250 mm 2 * 45 Nm AB = 400 mm 60 AC = 0,0, = 700 mm: %3D...
-
If someone's Z-score for a variable was 0.67. Their score is a significant extreme score. Their score is not significant. O Their score is slightly above average. O Their score is an outlier.
-
Saguaro Systems produces and sells stereo systems for MP3 players. The following information has been collected about the costs related to the systems: Selling price per unit ........ ... .. $70...
-
Conrad Miller owns a small sheet metal business. He produces three different types of sheet metal. Their sizes are similar, but they have different degrees of flexibility. Costs are allocated based...
-
Suppose that a car dealership decided it would no longer compensate employees with sales commissions, but instead pay a salary with a bonus for high customer satisfaction ratings. What problems would...
-
Define family law and identify the kinds of issues that are addressed in a family law practice.
-
Describe the role of a paralegal in a family law practice.
-
Identify the kinds of resources included in a basic family law library.

Study smarter with the SolutionInn App