Question: 6. Elements of security include confidentiality, integrity, and availability. Which technique provides for integrity and confidentiality? A. Encryption B. B. UPS C. C. Hashing D.
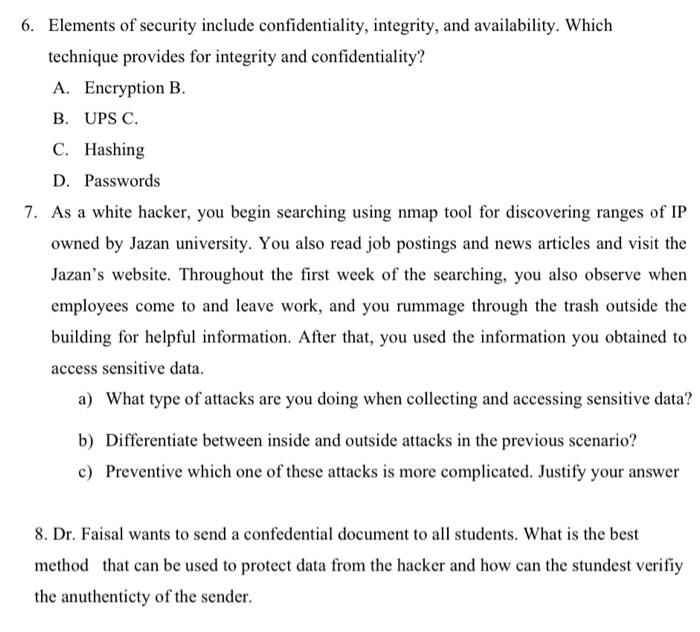
6. Elements of security include confidentiality, integrity, and availability. Which technique provides for integrity and confidentiality? A. Encryption B. B. UPS C. C. Hashing D. Passwords 7. As a white hacker, you begin searching using nmap tool for discovering ranges of IP owned by Jazan university. You also read job postings and news articles and visit the Jazan's website. Throughout the first week of the searching, you also observe when employees come to and leave work, and you rummage through the trash outside the building for helpful information. After that, you used the information you obtained to access sensitive data. a) What type of attacks are you doing when collecting and accessing sensitive data? b) Differentiate between inside and outside attacks in the previous scenario? c) Preventive which one of these attacks is more complicated. Justify your answer 8. Dr. Faisal wants to send a confedential document to all students. What is the best method that can be used to protect data from the hacker and how can the stundest verifiy the anuthenticty of the sender
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


