Question: 7. How could an air gap be exploited by a cybercriminal to gain access to protected devices in an industrial network? A. By using hacked
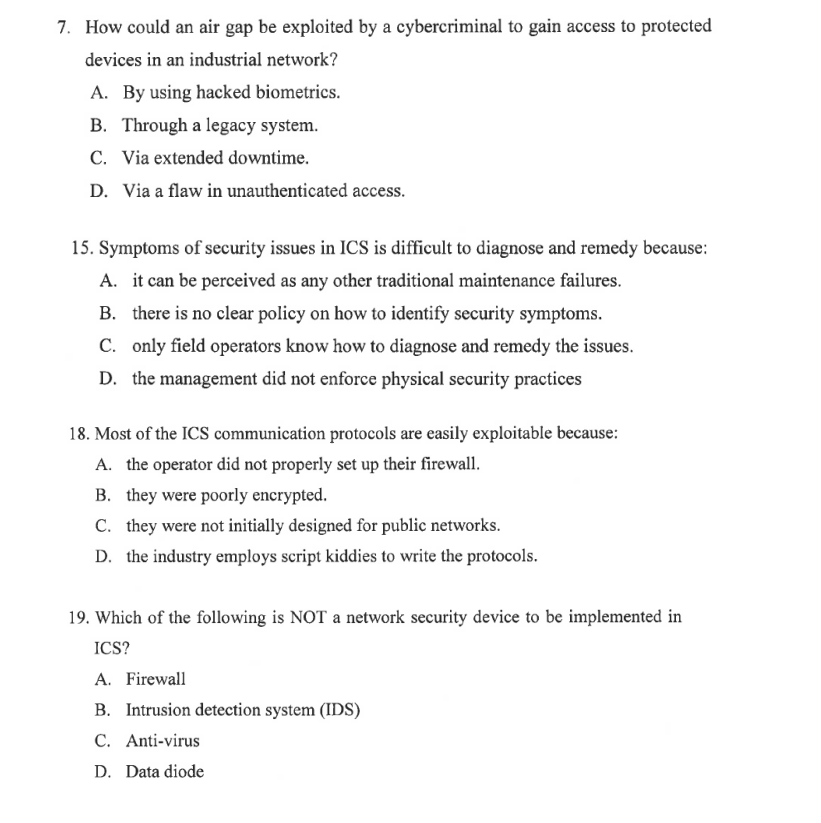
7. How could an air gap be exploited by a cybercriminal to gain access to protected devices in an industrial network? A. By using hacked biometrics. B. Through a legacy system. C. Via extended downtime. D. Via a flaw in unauthenticated access. 15. Symptoms of security issues in ICS is difficult to diagnose and remedy because: A. it can be perceived as any other traditional maintenance failures. B. there is no clear policy on how to identify security symptoms. C. only field operators know how to diagnose and remedy the issues. D. the management did not enforce physical security practices 18. Most of the ICS communication protocols are easily exploitable because: A. the operator did not properly set up their firewall. B. they were poorly encrypted. C. they were not initially designed for public networks. D. the industry employs script kiddies to write the protocols. 19. Which of the following is NOT a network security device to be implemented in ICS? A. Firewall B. Intrusion detection system (IDS) C. Anti-virus D. Data diode
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


