7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
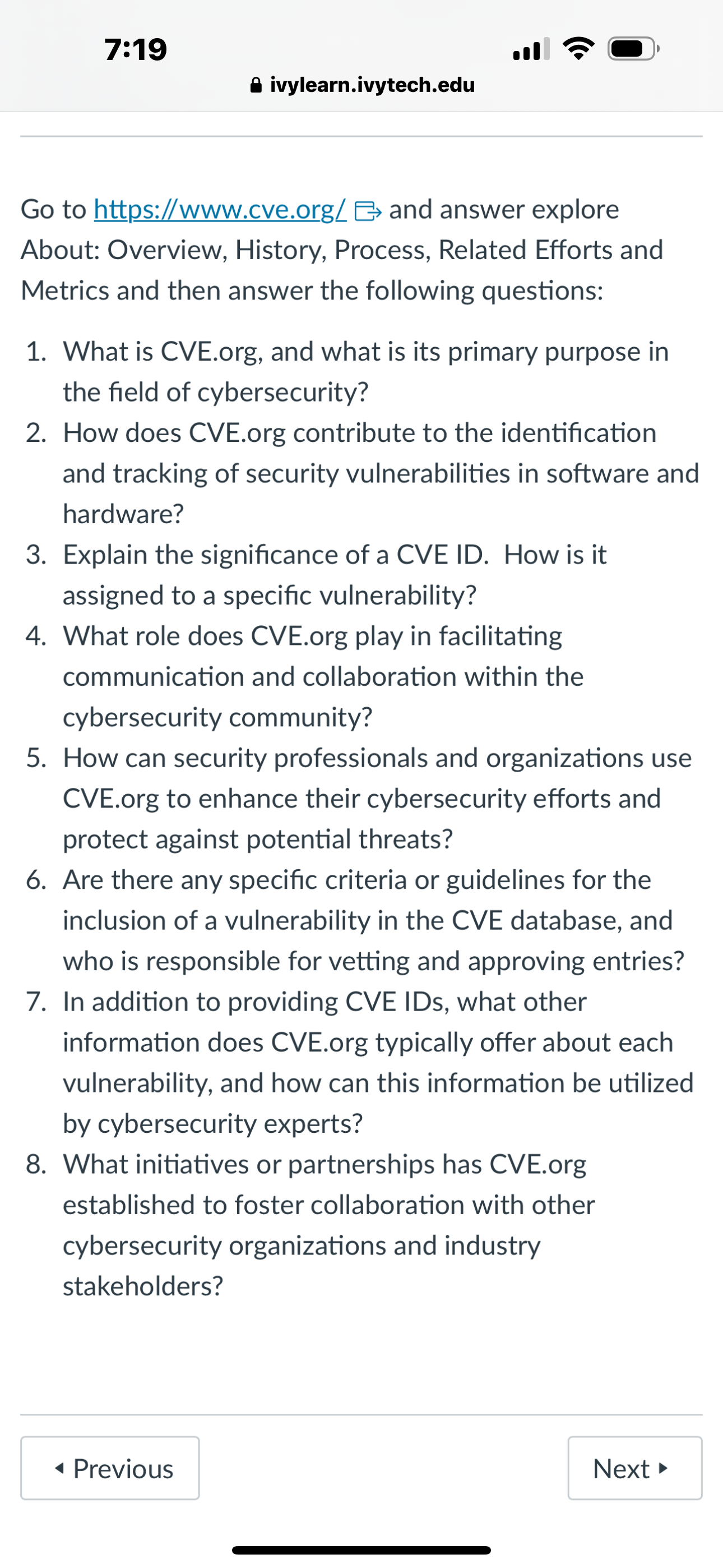
7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and then answer the following questions: 1. What is CVE.org, and what is its primary purpose in the field of cybersecurity? 2. How does CVE.org contribute to the identification and tracking of security vulnerabilities in software and hardware? 3. Explain the significance of a CVE ID. How is it assigned to a specific vulnerability? 4. What role does CVE.org play in facilitating communication and collaboration within the cybersecurity community? 5. How can security professionals and organizations use CVE.org to enhance their cybersecurity efforts and protect against potential threats? 6. Are there any specific criteria or guidelines for the inclusion of a vulnerability in the CVE database, and who is responsible for vetting and approving entries? 7. In addition to providing CVE IDs, what other information does CVE.org typically offer about each vulnerability, and how can this information be utilized by cybersecurity experts? 8. What initiatives or partnerships has CVE.org established to foster collaboration with other cybersecurity organizations and industry stakeholders? Previous Next 7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and then answer the following questions: 1. What is CVE.org, and what is its primary purpose in the field of cybersecurity? 2. How does CVE.org contribute to the identification and tracking of security vulnerabilities in software and hardware? 3. Explain the significance of a CVE ID. How is it assigned to a specific vulnerability? 4. What role does CVE.org play in facilitating communication and collaboration within the cybersecurity community? 5. How can security professionals and organizations use CVE.org to enhance their cybersecurity efforts and protect against potential threats? 6. Are there any specific criteria or guidelines for the inclusion of a vulnerability in the CVE database, and who is responsible for vetting and approving entries? 7. In addition to providing CVE IDs, what other information does CVE.org typically offer about each vulnerability, and how can this information be utilized by cybersecurity experts? 8. What initiatives or partnerships has CVE.org established to foster collaboration with other cybersecurity organizations and industry stakeholders? Previous Next
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these algorithms questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Dissertation Topic: "The Effects of Cybersecurity Measures on the Productivity and Well-being of Teleworkers in the Healthcare Industry". Introduction Draft no more than TWO paragraphs here -...
-
George and Weezy received $29,100 of Social Security benefits this year ($11,000 for George: $18,100 for Weezy). They also received $4,800 of Interest from jointly owned City of Ranburne Bonds and...
-
What specific statements in this case appear to reflect individualized consideration, a core component of transformational leadership, by Branson?
-
Give an example of a general coaching statement as contrasted to a pinpointed coaching statement. Which is more effective and why?
-
At 3:00 a.m. on November 22, 2010, 16-year-old Sydney McLemore was driving a Mazda3 with her friend, Natalie Hurst, in the front passenger seat. The vehicle was traveling south on Ross Bridge Highway...
-
Zebra Imaginarium, a retail business, had the following cash receipts during December 20--. The sales tax is 6%. Dec. 1 Received payment on account from Michael Anderson, $1,360. 2 Received payment...
-
. Conduct research and review the pricing models for Amazon Web Services and Microsoft's Azure. . How are they similar and how are they different?
-
Yvonne Delaney is playing Chris Becker a single point for the womens world tennis championship. She has won the coin toss and elected to serve. if she tries a hard serve, her probability of getting...
-
If Indias economic growth slows and incomes grow more slowly, and if other things remain the same, how will the demand for or supply of loanable funds in India change? The government of India set a...
-
Job boards have become popular with organizations and job applicants. However, one major ethical concern has to do with information privacy. Two considerations seem especially important to consider....
-
Pedro Aguilar, twenty-nine, and John Anderson, thirty, graduated in 2017 from Caltech (California Institute of Technology), both obtaining a Master of Science in Electrical Engineering. Pedro, a...
-
What do you think happened to inflation expectations between 2010 and 2017 and why? From 2010 to 2017, the long-term real interest rate paid by the safest corporations decreased from 3 percent to...
-
In 2016, suppose that the stock market crashes and the default risk increases. Explain how this increase in default risk influences the Lee familys supply of loanable funds curve. In 2015, the Lee...
-
XYZ Corp. has a large positive market value added (MVA). As a result, which of the following statements must be true? Select one: a. XYZ will have a basic earning power ratio that exceeds its...
-
What are the principal alloying elements in SAE 4340 steel?
-
Scott Butterfield is self-employed as a CPA. He uses the cash method of accounting, and his Social Security number is 644-47-7833. His principal business code is 541211. Scott's CPA practice is...
-
Joan is a self-employed attorney in New York City. Joan took a trip to San Diego, CA, primarily for business, to consult with a client and take a short vacation. On the trip, Joan incurred the...
-
Jim (age 50) and Martha (age 49) are married with three dependent children. They file a joint return for 2012. Their income from salaries totals $50,000, and they received $10,000 in taxable...
-
Repeat problem 41 with the specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) and the dimensions of the cavity \(104 \times 104 \times 9 \mathrm{~mm}^{3}\). Elastic constants of the...
-
Repeat problem 41 with elastic constants of the plastic as \(E=10 \mathrm{GPa}\) and \(v=0.485\). Problem 42: A rectangular plastic specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) is...
-
A rectangular plastic specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) is placed in a rectangular metal cavity. The dimensions of the cavity are \(101 \times 101 \times 9...

Study smarter with the SolutionInn App


