75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
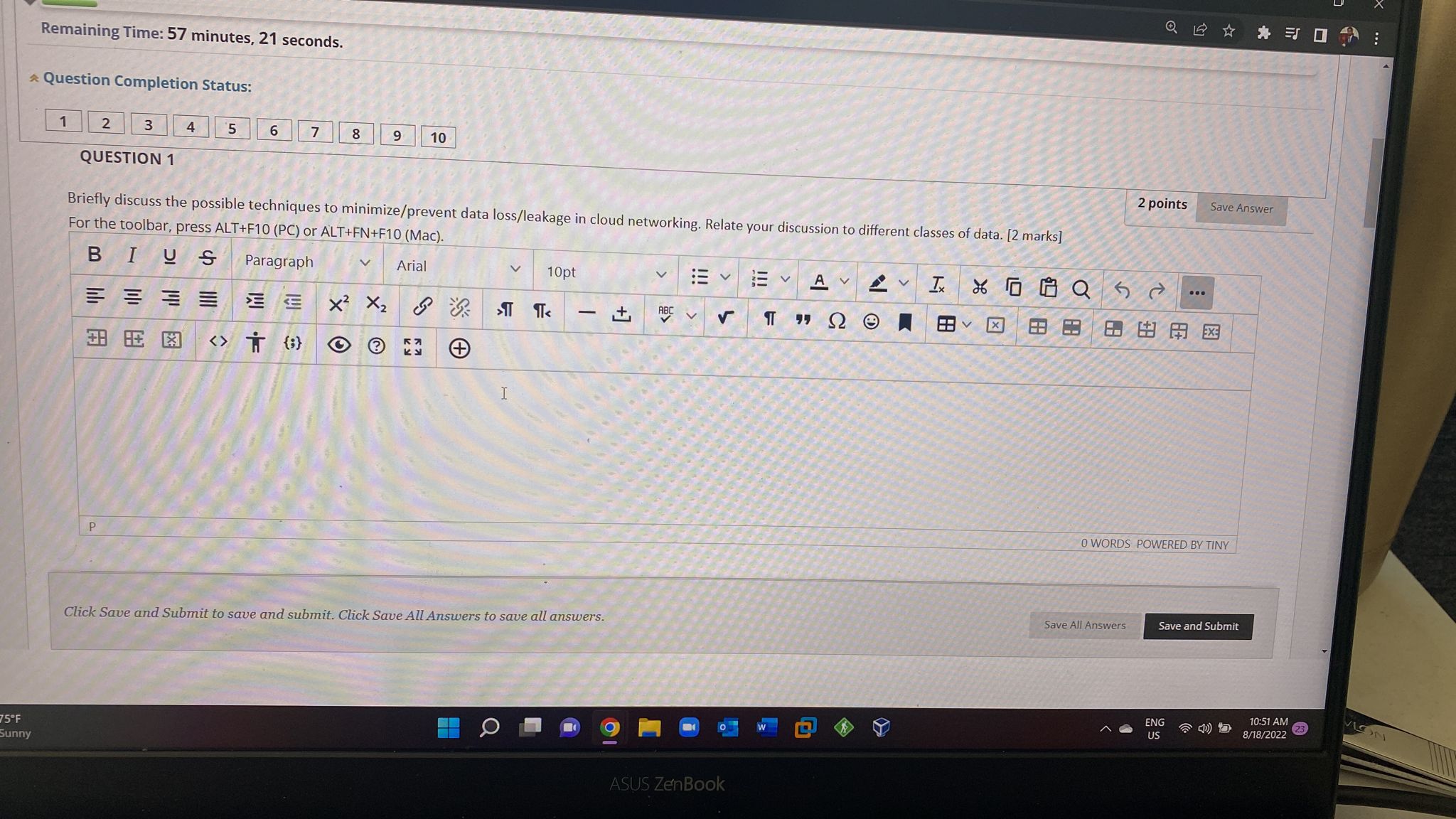
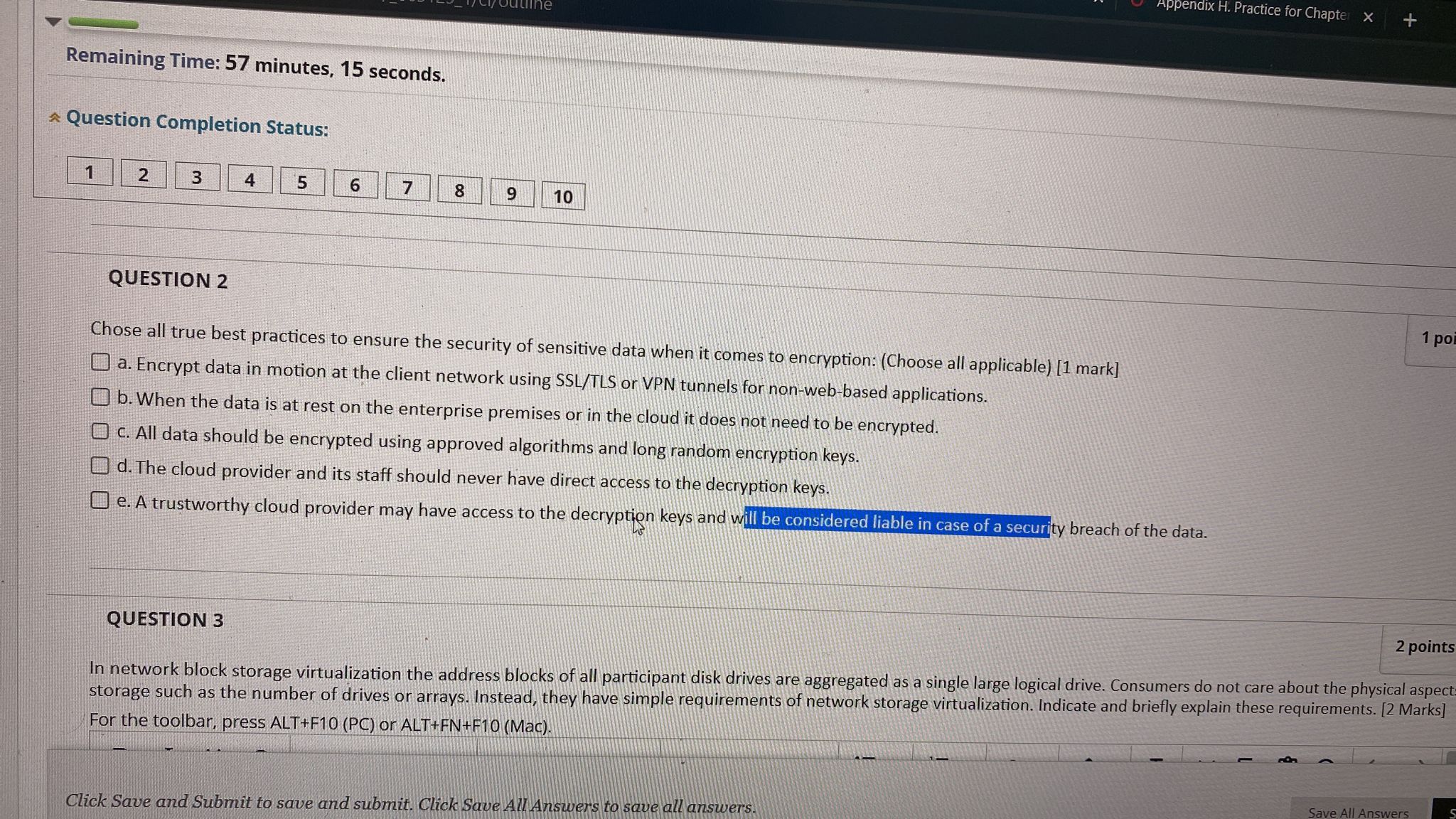
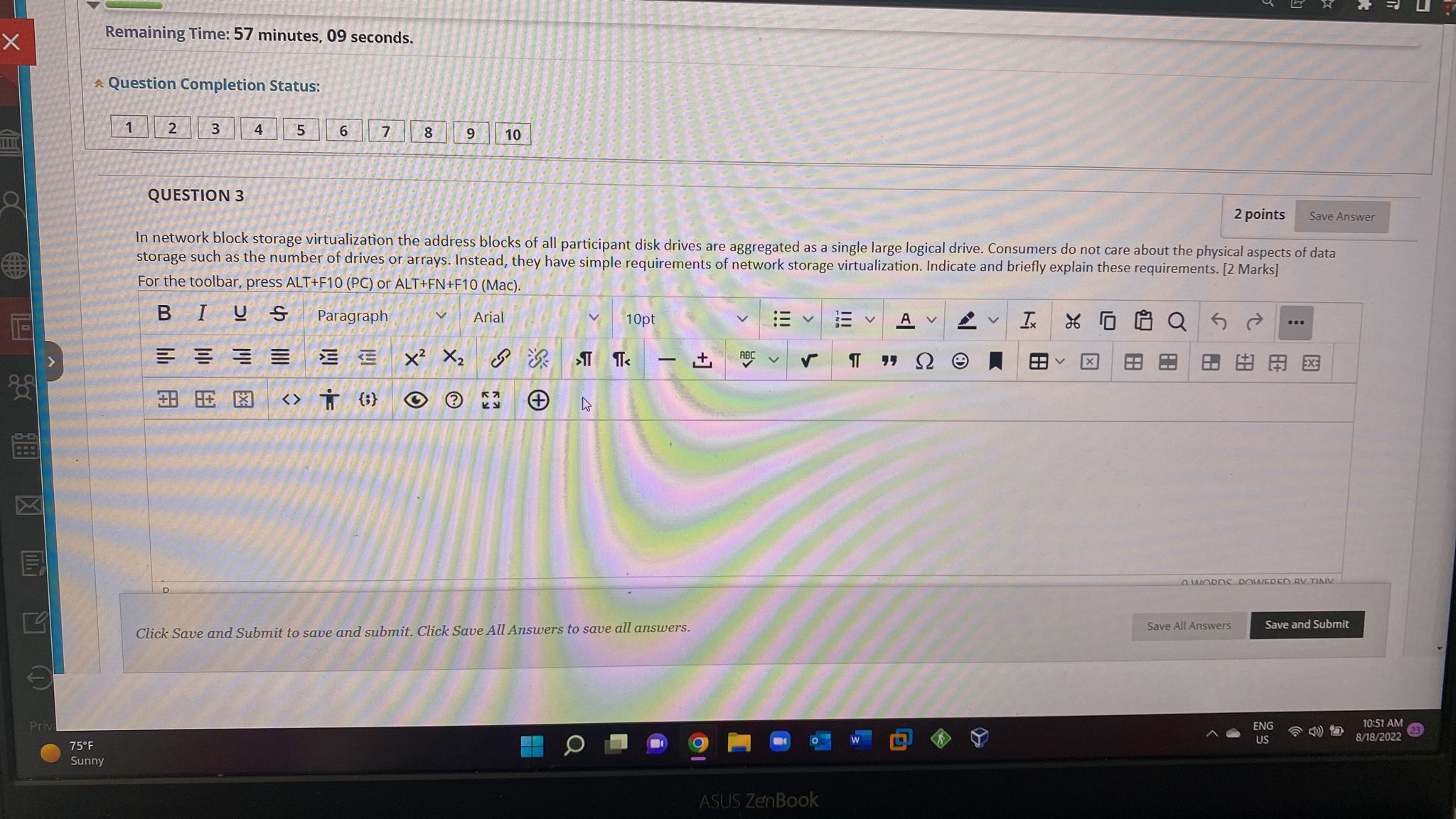
75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION 1 P 5 6 7 8 @X Briefly discuss the possible techniques to minimize/prevent data loss/leakage in cloud networking. Relate your discussion to different classes of data. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph Arial = = = = 3.8 8: 1:3 TO) X X 9 10 & 53 T I 10pt TT < Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC !!! > S ASUS ZenBook !!! A V " A 8.8 - I Q5 2 X C QE = 0 2 points Save All Answers ... 8&A= Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 x : VLON Remaining Time: 57 minutes, 15 seconds. Question Completion Status: 1 2 3 4 QUESTION 3 5 6 7 8 9 10 QUESTION 2 Chose all true best practices to ensure the security of sensitive data when it comes to encryption: (Choose all applicable) [1 mark] a. Encrypt data in motion at the client network using SSL/TLS or VPN tunnels for non-web-based applications. b. When the data is at rest on the enterprise premises or in the cloud it does not need to be encrypted. O c. All data should be encrypted using approved algorithms and long random encryption keys. d. The cloud provider and its staff should never have direct access to the decryption keys. e. A trustworthy cloud provider may have access to the decryption keys and will be considered liable in case of a security breach of the data. Appendix H. Practice for Chapter X Click Save and Submit to save and submit. Click Save All Answers to save all answers. + 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspect- storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 Marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). 1 po Save All Answers S X T- 200 XI E Priva Remaining Time: 57 minutes, 09 seconds. 75F Sunny Question Completion Status: 1 2 3 QUESTION 3 4 5 6 7 8 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspects of data storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph EEEE * 9 10 X XG 3.8 8 13 {:} O Arial KH + 10pt > < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC ASUS ZenBook V A V " V Ix V XQ5 Save All Answers Save Answer QWORDS POWERED RV TINV Save and Submit ENG US C 10:51 AM 8/18/2022 75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION 1 P 5 6 7 8 @X Briefly discuss the possible techniques to minimize/prevent data loss/leakage in cloud networking. Relate your discussion to different classes of data. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph Arial = = = = 3.8 8: 1:3 TO) X X 9 10 & 53 T I 10pt TT < Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC !!! > S ASUS ZenBook !!! A V " A 8.8 - I Q5 2 X C QE = 0 2 points Save All Answers ... 8&A= Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 x : VLON Remaining Time: 57 minutes, 15 seconds. Question Completion Status: 1 2 3 4 QUESTION 3 5 6 7 8 9 10 QUESTION 2 Chose all true best practices to ensure the security of sensitive data when it comes to encryption: (Choose all applicable) [1 mark] a. Encrypt data in motion at the client network using SSL/TLS or VPN tunnels for non-web-based applications. b. When the data is at rest on the enterprise premises or in the cloud it does not need to be encrypted. O c. All data should be encrypted using approved algorithms and long random encryption keys. d. The cloud provider and its staff should never have direct access to the decryption keys. e. A trustworthy cloud provider may have access to the decryption keys and will be considered liable in case of a security breach of the data. Appendix H. Practice for Chapter X Click Save and Submit to save and submit. Click Save All Answers to save all answers. + 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspect- storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 Marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). 1 po Save All Answers S X T- 200 XI E Priva Remaining Time: 57 minutes, 09 seconds. 75F Sunny Question Completion Status: 1 2 3 QUESTION 3 4 5 6 7 8 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspects of data storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph EEEE * 9 10 X XG 3.8 8 13 {:} O Arial KH + 10pt > < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC ASUS ZenBook V A V " V Ix V XQ5 Save All Answers Save Answer QWORDS POWERED RV TINV Save and Submit ENG US C 10:51 AM 8/18/2022
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
20 -101 10 in- laminate substrate Fig.2 Q2: The tool shown in Fig.2 is used in a gluing operation to press a thin laminate to a thicker substrate. If the wheels at points A and B both have 2 in...
-
The drawing shows a hydraulic system used with disc brakes. The force is applied perpendicularly to the brake pedal. The pedal rotates about the axis shown in the drawing and causes a force to be...
-
An ice cream maker is in the form of a soccer ball (Figure P20.71). You fill the inner container with a mixture of cream and sugar at \(32.0^{\circ} \mathrm{C}\) and add rock salt and ice to the...
-
Early Start Bakery mass-produces bread using three sequential processing departments: Mixing, Baking, and Packaging. The following transactions occurred during February: Requirements: 1. Post each of...
-
Morello Inc. manufactures basketballs for the National Basketball Association (NBA). For the first 6 months of 2014, the company reported the following operating results while operating at 90% of...
-
6. To a ground observer the block C is moving with v, and the block A with v. B is moving with v relative to C as shown in the figure. Identify the correct statement. (a) V-V =Vo (b)= A C B (c) V+V =...
-
Imagine that you are Magna's new corporate controller and answer the following: 1. Describe Magna's strategy in terms of how it competes for customers. 2. Based on Magna's strategy and the data...
-
Use Euler's method with step sizes h = 0.1 and h 0.05 to find approximate values of the solution of the initial value problem y = +1, y (1) = 1 at = 0, 0.1, and 1.0 3 !! %3D Compare these...
-
Provide Vertical and Horizontal Analysis based on the attached income statement. ($ in millions, except per share amounts) 2021 2020 2019 REVENUES Base management fees S 669 $ 443 $ 1,180 Franchise...
-
1. Why do you think the author included this chapter in the reading? 2. What are the three (3) main take aways from reading the material? Provide reasons for your selection.
-
Explain why non-HR and line managers are becoming more involved in the HRM function and implementation of HRM activities and programs
-
Consider the following three projects: Year 1 2 3 4 5 6 Project A -$10,000 $6,000 $6,000 $6,000 $6,000 $6,000 Project B -$1,000 -$1,000 -$1,000 -$1,000 -$1,000 $28,000 Project C -$20,000 $0 $0 $0 $0...
-
1. Why is project planning so important? 2. How might we plan for risks that we cannot identify in the risk management section of the project charter? 3. Might milestones and phase-gates both occur...
-
A laboratory rat is exposed to an alpha-radiation source whose activity is 14.3 mCi. a) What is the activity of the radiation in disintegrations per second? b) The rat has a mass of 385 g and is...
-
Archangel Corporation prepared the following variance report. Instructions Fill in the appropriate amounts or letters for the question marks in the report. ARCHANGEL CORPORATION Variance...
-
The Consolidated Edison Company sells electricity (82% of revenues), gas (13%), and steam (5 %) in New York City and Westchester County. Bart Thomas, company forecaster, is assigned the task of...
-
You have been hired to help Mary with her forecasting problem. Write her a memo that summarizes her efforts to date and that recommends a course of action to her. Be sure your memo addresses the...
-
A large construction company is trying to establish a useful way to view typical profits from jobs obtained from competitive bidding. Because the jobs vary substantially in size and the final amount...
-
A single-tank liquid-level system with inflow rate \(q_{i}\) as its input and liquid level \(h\) as its output is modeled as \(R A \dot{h}+g h=R q_{i}(t), h(0)=0\), where \(R, A, g=\) const. If the...
-
The mechanical system in Figure 8.37, where all parameter values are in consistent physical units, is subject to initial conditions \(x_{1}(0)=1, x_{2}(0)=1, \dot{x}_{1}(0)=-1, \dot{x}_{2}(0)=1\)....
-
Find the state vector via the formal-solution approach. \(\dot{\mathbf{x}}=\left[\begin{array}{cc}5 & 1 \\ -4 & 1\end{array} ight] \mathbf{x}+\left[\begin{array}{c}1 \\ -1\end{array} ight] u, \quad...

Study smarter with the SolutionInn App