8. EEE 459/591 Communication Networks Consider the network architecture in the figure below consisting of a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
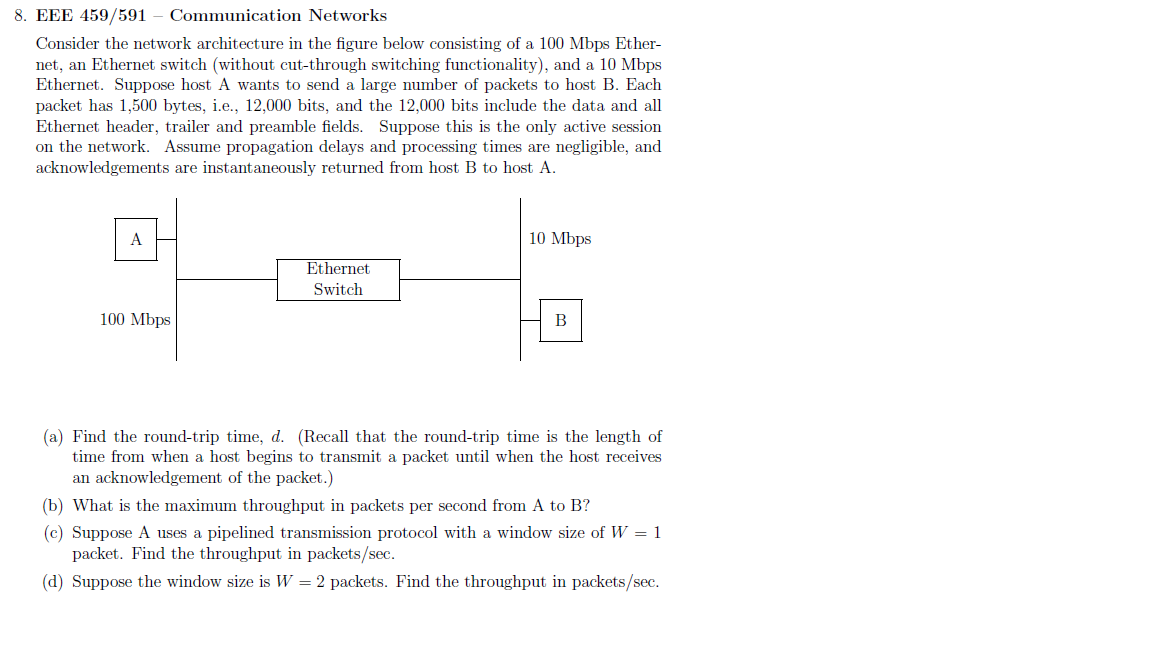
8. EEE 459/591 Communication Networks Consider the network architecture in the figure below consisting of a 100 Mbps Ether- net, an Ethernet switch (without cut-through switching functionality), and a 10 Mbps Ethernet. Suppose host A wants to send a large number of packets to host B. Each packet has 1,500 bytes, i.e., 12,000 bits, and the 12,000 bits include the data and all Ethernet header, trailer and preamble fields. Suppose this is the only active session on the network. Assume propagation delays and processing times are negligible, and acknowledgements are instantaneously returned from host B to host A. A 100 Mbps Ethernet Switch 10 Mbps B (a) Find the round-trip time, d. (Recall that the round-trip time is the length of time from when a host begins to transmit a packet until when the host receives an acknowledgement of the packet.) (b) What is the maximum throughput in packets per second from A to B? (c) Suppose A uses a pipelined transmission protocol with a window size of W = 1 packet. Find the throughput in packets/sec. (d) Suppose the window size is W = 2 packets. Find the throughput in packets/sec. 8. EEE 459/591 Communication Networks Consider the network architecture in the figure below consisting of a 100 Mbps Ether- net, an Ethernet switch (without cut-through switching functionality), and a 10 Mbps Ethernet. Suppose host A wants to send a large number of packets to host B. Each packet has 1,500 bytes, i.e., 12,000 bits, and the 12,000 bits include the data and all Ethernet header, trailer and preamble fields. Suppose this is the only active session on the network. Assume propagation delays and processing times are negligible, and acknowledgements are instantaneously returned from host B to host A. A 100 Mbps Ethernet Switch 10 Mbps B (a) Find the round-trip time, d. (Recall that the round-trip time is the length of time from when a host begins to transmit a packet until when the host receives an acknowledgement of the packet.) (b) What is the maximum throughput in packets per second from A to B? (c) Suppose A uses a pipelined transmission protocol with a window size of W = 1 packet. Find the throughput in packets/sec. (d) Suppose the window size is W = 2 packets. Find the throughput in packets/sec.
Expert Answer:
Answer rating: 100% (QA)
a The roundtrip time d is the time from when host A begins to transmit a packet until when host A re... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these accounting questions
-
Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has three links, of rates RI =500 kbps, R2 =2 Mbps, and R) = I Mbps. a. Assuming no other traffic in the network,...
-
Consider a 100 Mbps 100BASE-T Ethernet with all nodes directly connected to a hub. To have an efficiency of 0.50, what should be the maximum distance between a node and the hub? Assume a frame length...
-
A node in a communication network receives data packets of variable length. Each packet has a random number of bits that is uniformly distributed over the integers {100, 101, 102 999}. The number of...
-
How does inventory turnover provide information about a companys short-term liquidity?
-
Use the accounting equation to answer each of the following questions. (a) The liabilities of Alli Company are $90,000. Common stock account is $150,000; dividends are $40,000; revenues, $450,000;...
-
Use the complete information in the file c13_01.xlsx to answer the following questions: 1. Approximately what fraction of the time is Betty idle? Is Bens estimate correct? 2. Approximately how many...
-
Discuss the uses and limitations of the statement of financial position for decision-making purposes.
-
On January 1, 2011, Brendan, Inc., reports net assets of $760,000 although equipment (with a four year life) having a book value of $440,000 is worth $500,000 and an unrecorded patent is valued at...
-
Explain how the communication tone, structure and style may impact on others. Provide an example of each. Question Explain how the communication tone, structure and style may impact on others. (40-80...
-
Derive and solve the equation of motion for the mass m in terms of the variable x for the system shown. Neglect the mass of the lever AOC and assume small oscillations. C k2 k1 ww TxB = bo cos ot A a
-
1. A moving coil meter has a full scale reading of 1 mA and aresistance of 80 ohm. Determine the shunt resistance necessary forthe meter to be used to measure 100mA full scale? 2.Calculate the value...
-
3 . Answer all parts of the question a . Modern portfolio theory is built on a mean - variance framework. What assumptions are necessary for this framework to be a credible working hypothesis? Are...
-
Give an example of a time you have had to deal with change, professionally or personally.
-
Assume no insurance coverage . The pharmaceutical company producing Spinraza noticed that this drug was demanded slightly more after the price fell from $790,000 to $750,000: sales rose from 10,000...
-
Yocto, Ltd . is located in Alabama. Yocto sells cd players. At a volume of 4 , 6 8 8 units, Yocto has variable and fixed costs for natural gas of $ 3 1 8 , 0 9 3 and $ 2 5 9 , 1 4 0 respectively....
-
Prompt: RSF is 1 0 , 0 0 0 . GSF is 8 , 0 0 0 . Going in income is $ 1 0 0 / RSF growing 3 % per year. Going in expenses are $ 3 5 / GSF growing 1 . 5 % per year. Acquisition is made at a 5 . 5 % cap...
-
7. When a company has operating and non-operating items on its Income Statement, it determines the Tax on Operating Profit by Adding the tax shield to the Income tax expense reported on the Income...
-
Place a tick in the appropriate grid to identify the balance that would be brought down in each of the following named accounts, in the books of Rizwy Mohamed: (a) In the Cash account: if Rizwy...
-
Consider the network below. a) Suppose that this network is a datagram network. Show the forwarding table in router A, such that all traffic destined to host H3 is forwarded through interface 3. b)...
-
Describe some hypothetical services that the network layer can provide to a single packet. Do the same for a flow of packets. Are any of your hypothetical services provided by the Internet's network...
-
Describe how loops in paths can be detected in BGP.
-
The finite element method is a. an approximate analytical method b. a numerical method c. an exact analytical method
-
What is the role of transformation matrices in the finite element method?
-
True or False. The element mass matrices are always singular.

Study smarter with the SolutionInn App


