Question: 3-4 Use the CVD model to evaluate the following three locations in termis of access to five destinations: Site 1 is located 3, 245,
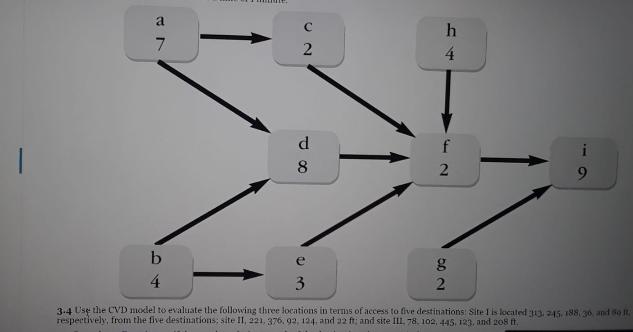
3-4 Use the CVD model to evaluate the following three locations in termis of access to five destinations: Site 1 is located 3, 245, 188, 36 and do It. respectively, from the five destinations, site Il, 221, 376. 92, 124, and 22 ft; and site III, 78. 102, 445, 123, and 208 t. a 4. 8 2 9. b e 4 3 3-4 Use the CVD model to evaluate the following three locations in terms of access to five destinations Sitel is located 33. 245, 188, 30 and do It. respectively, from the five destinations; site II, 221, 376, 92, 124. and 22 ft; and site III, 78. 102, 445, 123, and 208 t.
Step by Step Solution
3.32 Rating (152 Votes )
There are 3 Steps involved in it
In the costvolumedistance CVD approach the desirability of closeness is based on the total cost of m... View full answer

Get step-by-step solutions from verified subject matter experts


