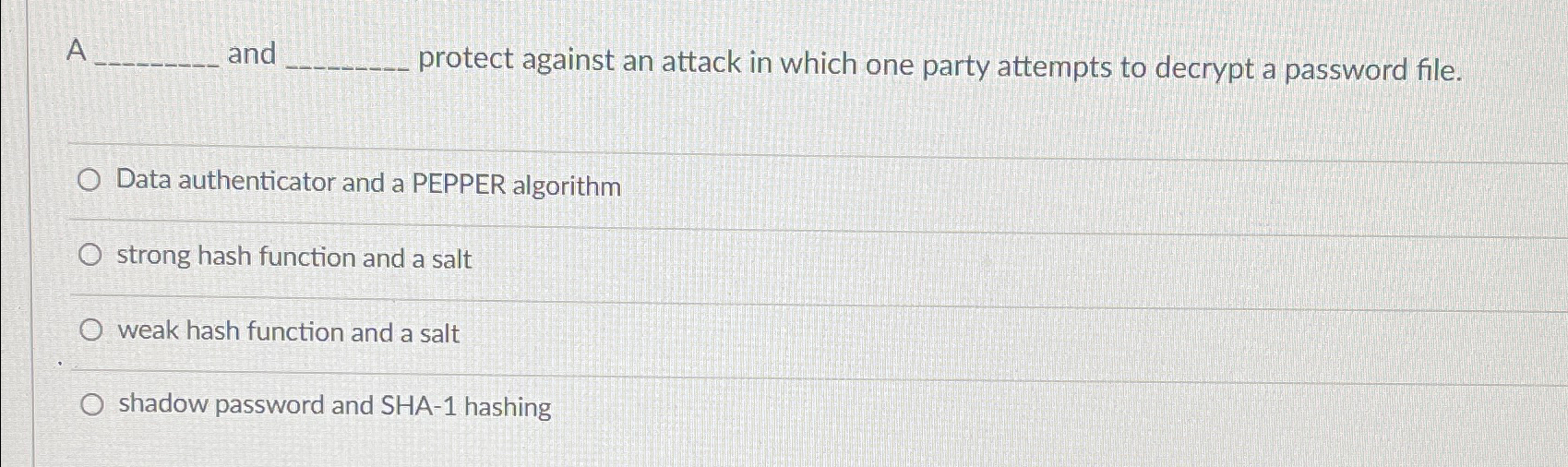
Question: A and protect against an attack in which one party attempts to decrypt a password file. Data authenticator and a PEPPER algorithm strong hash function
A and protect against an attack in which one party attempts to decrypt a password file.
Data authenticator and a PEPPER algorithm
strong hash function and a salt
weak hash function and a salt
shadow password and SHA hashing
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


