Question: a. b. C. shows a sample code. int binsearch (int X, int VII, int n) { int low, high, mid; low - 0; ii.
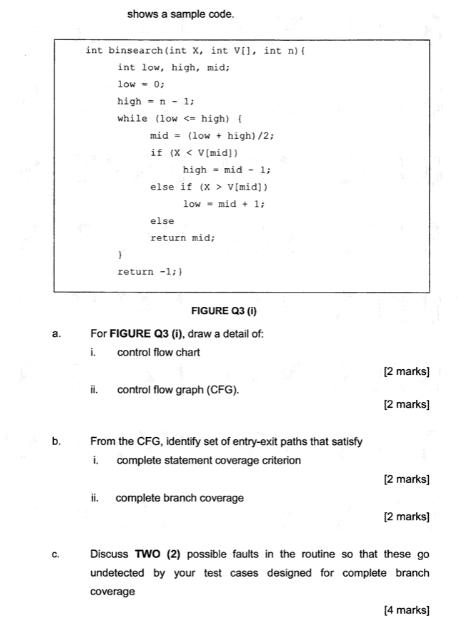
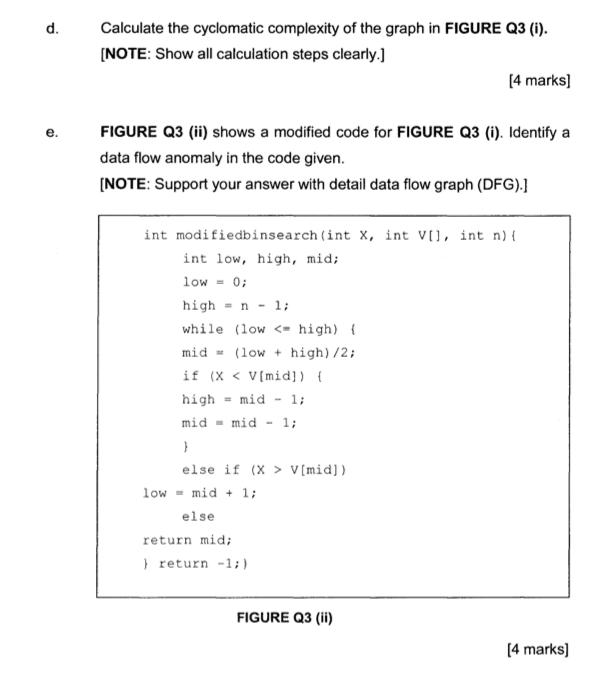
a. b. C. shows a sample code. int binsearch (int X, int VII, int n) { int low, high, mid; low - 0; ii. high = n - 1; while (low < high) { mid= (low+ high)/2; if (X < V[mid)) high-mid - 1; else if (x > V[mid)) low - mid + 1; else return mid; } return -1;) FIGURE Q3 (i) For FIGURE Q3 (i), draw a detail of: i. control flow chart control flow graph (CFG). From the CFG, identify set of entry-exit paths that satisfy complete statement coverage criterion i ii. complete branch coverage [2 marks] [2 marks] [2 marks] [2 marks] Discuss TWO (2) possible faults in the routine so that these go undetected by your test cases designed for complete branch coverage [4 marks] d. e. Calculate the cyclomatic complexity of the graph in FIGURE Q3 (i). [NOTE: Show all calculation steps clearly.] FIGURE Q3 (ii) shows a modified code for FIGURE Q3 (i). Identify a data flow anomaly in the code given. [NOTE: Support your answer with detail data flow graph (DFG).] int modifiedbinsearch (int X, int V[], int n) { int low, high, mid; low= 0; high n 1; while (low V[mid]) [4 marks] low mid + 1; else return mid; } return -1;) FIGURE Q3 (ii) [4 marks]
Step by Step Solution
3.40 Rating (163 Votes )
There are 3 Steps involved in it
Answer Given Below is the CGF of the provided function the pa... View full answer

Get step-by-step solutions from verified subject matter experts


