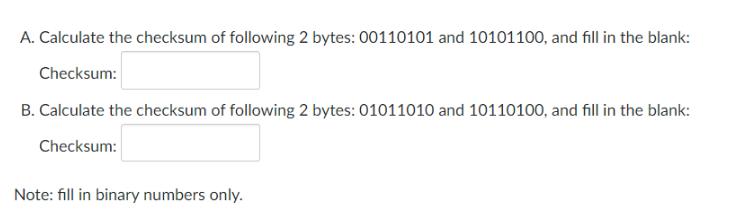
A. Calculate the checksum of following 2 bytes: 00110101 and 10101100, and fill in the blank:...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
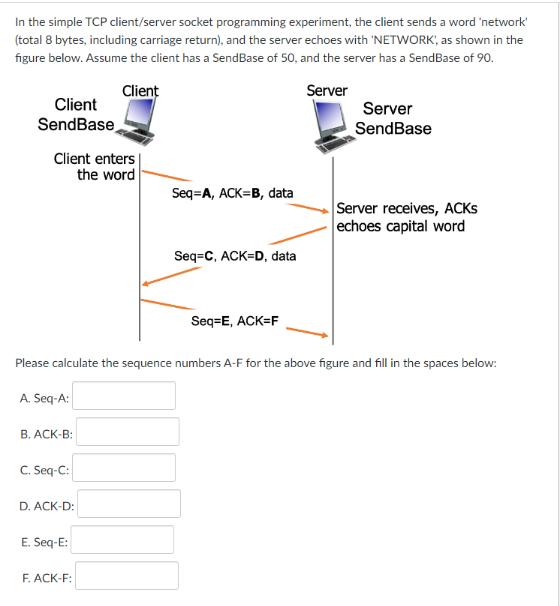
A. Calculate the checksum of following 2 bytes: 00110101 and 10101100, and fill in the blank: Checksum: B. Calculate the checksum of following 2 bytes: 01011010 and 10110100, and fill in the blank: Checksum: Note: fill in binary numbers only. In the simple TCP client/server socket programming experiment, the client sends a word 'network' (total 8 bytes, including carriage return), and the server echoes with 'NETWORK', as shown in the figure below. Assume the client has a SendBase of 50, and the server has a SendBase of 90. Client Server Client SendBase Client enters the word A. Seq-A: B. ACK-B: C. Seq-C:: D. ACK-D: Please calculate the sequence numbers A-F for the above figure and fill in the spaces below: E. Seq-E: Seq=A, ACK=B, data F. ACK-F: Seq=C, ACK=D, data Seq=E, ACK=F Server SendBase Server receives, ACKS echoes capital word A. Calculate the checksum of following 2 bytes: 00110101 and 10101100, and fill in the blank: Checksum: B. Calculate the checksum of following 2 bytes: 01011010 and 10110100, and fill in the blank: Checksum: Note: fill in binary numbers only. In the simple TCP client/server socket programming experiment, the client sends a word 'network' (total 8 bytes, including carriage return), and the server echoes with 'NETWORK', as shown in the figure below. Assume the client has a SendBase of 50, and the server has a SendBase of 90. Client Server Client SendBase Client enters the word A. Seq-A: B. ACK-B: C. Seq-C:: D. ACK-D: Please calculate the sequence numbers A-F for the above figure and fill in the spaces below: E. Seq-E: Seq=A, ACK=B, data F. ACK-F: Seq=C, ACK=D, data Seq=E, ACK=F Server SendBase Server receives, ACKS echoes capital word
Expert Answer:
Answer rating: 100% (QA)
Answer the checksum of the bytes 00110101 and 10101100 00110101 ... View the full answer

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
10- Highlight each node in the following AVL-Tree with balance. 5 1 2 3 4 9 7 O I 00 8 10
-
Butler Corporation has provided the following information pertaining to the year ended December 31, 2020 Accounts Payable $16,700 Interest Expense $2,500 Accounts Receivable $24,000 Inventory $15,200...
-
Manually simulate the Fletcher algorithm (Figure 10.18) to calculate the checksum of the following bytes: (2B) 16 , (3F) 16 , (6A) 16 , and (AF) 16 . Also show that the result is a weighted checksum....
-
How could not having a strategy hurt a brand on social media? What are some content ideas for those who are at the "Awareness" stage of the sales funnel? What does it mean to A/B test on a social...
-
Determine the length of member AB of the truss by first establishing a Cartesian position vector from A to B and then determining its magnitude. Given: a = 1.2 m b = 0.8 m c = 0.3 m d = 1.5 m θ...
-
9. A 2mx2mx1m block is held with its bottom just touching the water surface (see figure below), then released from rest at t=0. Assume that the block moves only vertically with its bottom remaining...
-
Eighteen plots of land in Indiana were given different applications of nitrogen. In each case, the previous crop had been soybeans and all other factors were roughly comparable. Use the 18...
-
The following costs result from the production and sale of 480,000 CD sets manufactured by Trace Company for the year ended December 31, 2011. The CD sets sell for $4.50 each. The company has a 25%...
-
Image transcription text Problem 2 Consider the following cantilever beam in Figure P2a, which is supported by a fixed support at point O. The beam is loaded with a diagonal force F = 950 N at point...
-
Crane Library, a nonprofit organization, presented the following statement of financial position and statement of activities for its fiscal year ended February 28, 2024. Assets Current Assets Cash...
-
What is the Relationship between Customer Satisfaction and Customer Loyalty in the Banking Sector in Syria?
-
With regard to pedigree analysis, make a list of observations that distinguish recessive, dominant, and X-linked patterns of inheritance.
-
Explain the role of RNase H (a component of reverse transcriptase) during the synthesis of HIV DNA.
-
Describe how changes in chromosome structure and number may promote cancer.
-
Describe how lytic bacteriophages are released from their host cells.
-
What is the difference between an oncogene and a tumorsuppressor gene? Give two examples of each type of gene.
-
Amazon.com is an example of a A. b2b organization B. retail outlet with many branches C. brick-and-mortar virtual organization D. click-and-mortar online vendor
-
Is the modified 5-question approach to ethical decision making superior to the modified moral standards or modified Past in approach?
-
In JPEG, explain why we need to round the result of division in the quantization step.
-
Repeat Problem 6-4 if each output slot carries 2 bits from each source. Problem 6-4 We need to use synchronous TDM and combine 20 digital sources, each of 100 Kbps. Each output slot carries 1 bit...
-
Explain why we do not need the router in Figure 9.15.
-
According to research on ethics in the workplace, _________ is/are often a major and frequent source of pressures that create ethical dilemmas for people in their jobs. (a) declining morals in...
-
A business owner makes a decision to reduce a plants workforce by 10% in order to cut costs and be able to save jobs for the other 90% of employees. This decision could be justified as ethical using...
-
If a manager fails to enforce a late-to-work policy for all workersthat is, by allowing some favored employees to arrive late without penaltiesthis would be considered a violation of _________. (a)...

Study smarter with the SolutionInn App


