Question: (a) Compute the border array of the string w = (ab) for n>2 and n E N. (b) Perform substring search using the Rabin-Karp
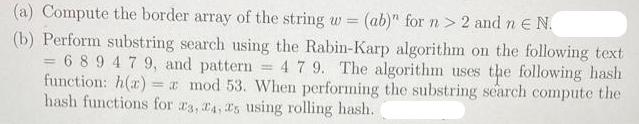
(a) Compute the border array of the string w = (ab)" for n>2 and n E N. (b) Perform substring search using the Rabin-Karp algorithm on the following text = 689479, and pattern 4 79. The algorithm uses the following hash function: h(r): = a mod 53. When performing the substring search compute the hash functions for 3, 4, 5 using rolling hash. -
Step by Step Solution
3.43 Rating (150 Votes )
There are 3 Steps involved in it
a The border array of a string w is an array that stores the length of the longest proper border of each prefix of the string A proper border is a nonempty substring that is both a prefix and suffix o... View full answer

Get step-by-step solutions from verified subject matter experts


