Question: (a) Consider ElGamal encryption with g = 7, p = 11. Bob chooses x = 3 as his private key. What is his public
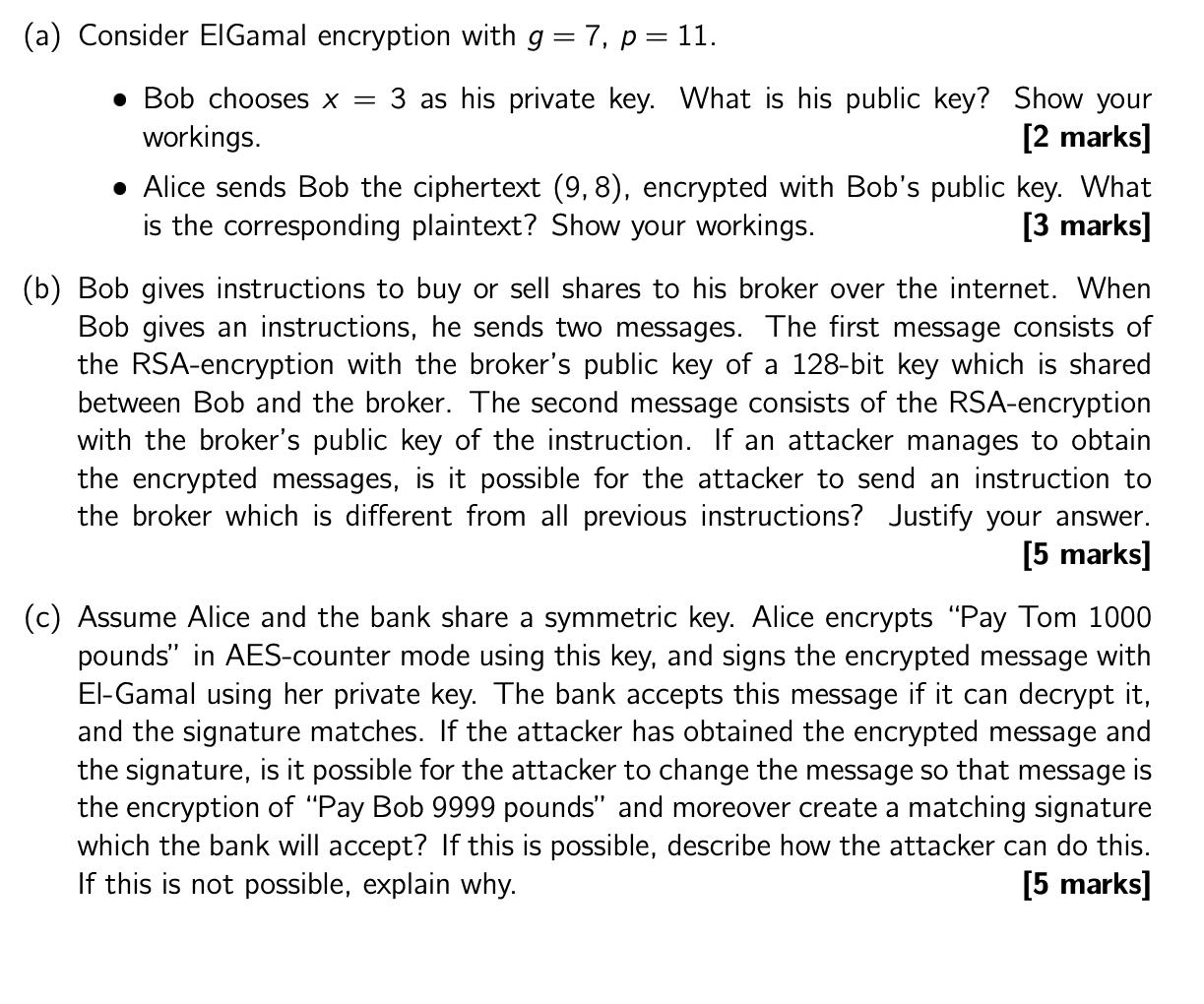
(a) Consider ElGamal encryption with g = 7, p = 11. Bob chooses x = 3 as his private key. What is his public key? Show your workings. [2 marks] Alice sends Bob the ciphertext (9,8), encrypted with Bob's public key. What is the corresponding plaintext? Show your workings. [3 marks] (b) Bob gives instructions to buy or sell shares to his broker over the internet. When Bob gives an instructions, he sends two messages. The first message consists of the RSA-encryption with the broker's public key of a 128-bit key which is shared between Bob and the broker. The second message consists of the RSA-encryption with the broker's public key of the instruction. If an attacker manages to obtain the encrypted messages, is it possible for the attacker to send an instruction to the broker which is different from all previous instructions? Justify your answer. [5 marks] (c) Assume Alice and the bank share a symmetric key. Alice encrypts "Pay Tom 1000 pounds" in AES-counter mode using this key, and signs the encrypted message with El-Gamal using her private key. The bank accepts this message if it can decrypt it, and the signature matches. If the attacker has obtained the encrypted message and the signature, is it possible for the attacker to change the message so that message is the encryption of "Pay Bob 9999 pounds" and moreover create a matching signature which the bank will accept? If this is possible, describe how the attacker can do this. If this is not possible, explain why. [5 marks]
Step by Step Solution
There are 3 Steps involved in it
a ElGamal Encryption Bobs Public Key Given parameters g 7 p 11 and Bobs private key x 3 Compute Bobs ... View full answer

Get step-by-step solutions from verified subject matter experts


