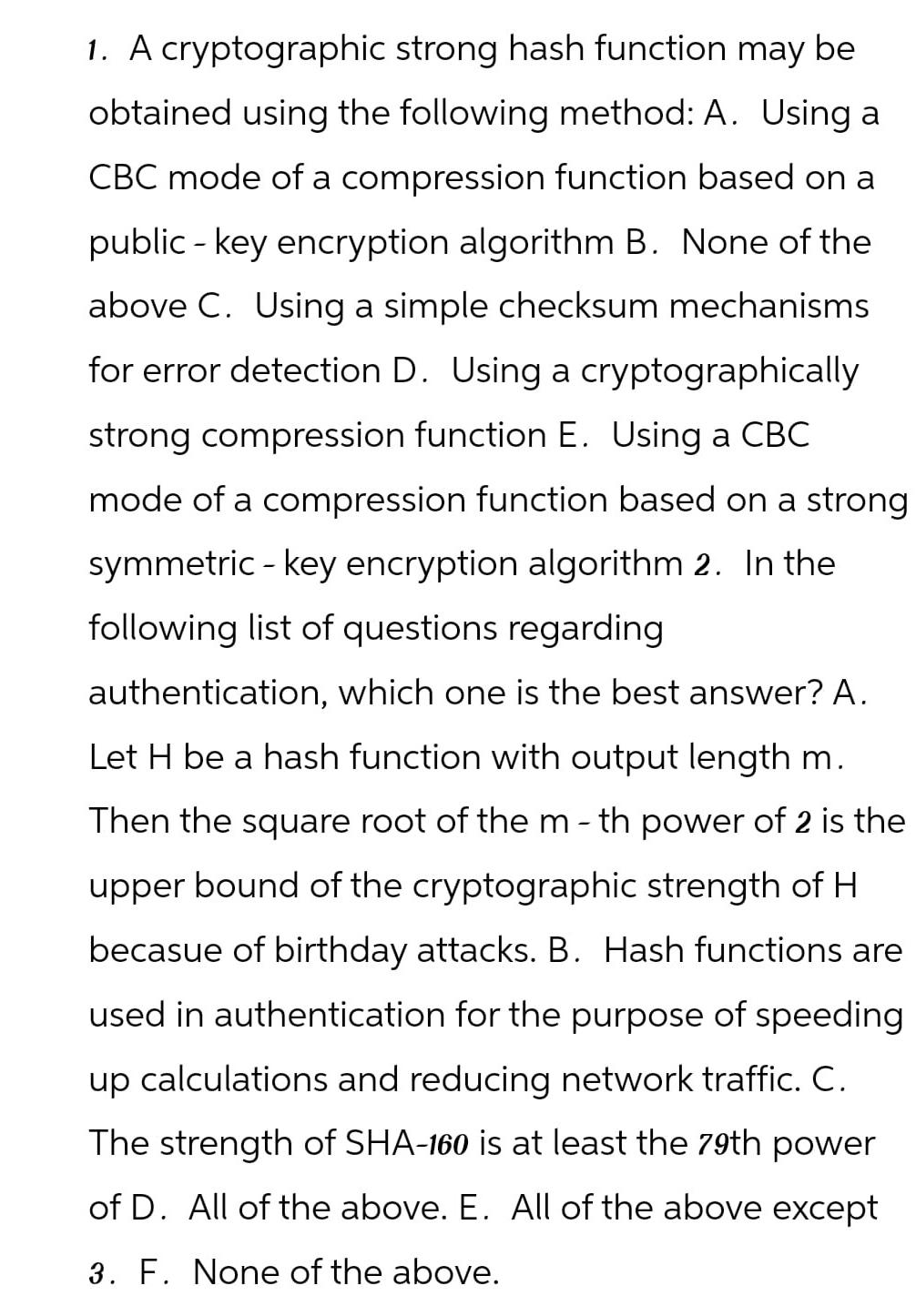
Question: A cryptographic strong hash function may be obtained using the following method: A . Using a C B C mode of a compression function based
A cryptographic strong hash function may be obtained using the following method: A Using a mode of a compression function based on a public key encryption algorithm B None of the above Using a simple checksum mechanisms for error detection Using a cryptographically strong compression function Using a mode of a compression function based on a strong symmetric key encryption algorithm In the following list of questions regarding authentication, which one is the best answer? A Let be a hash function with output length Then the square root of the th power of is the upper bound of the cryptographic strength of becasue of birthday attacks. B Hash functions are used in authentication for the purpose of speeding up calculations and reducing network traffic. C The strength of SHA is at least the th power of All of the above. All of the above except F None of the above.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


