Question: (a) Full Stealth and Boot Time Filtering are two of the critical features of modern Firewalls -state briefly what are the purpose of these
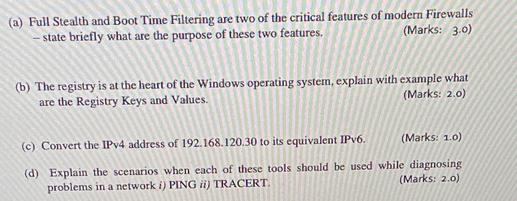
(a) Full Stealth and Boot Time Filtering are two of the critical features of modern Firewalls -state briefly what are the purpose of these two features. (Marks: 3.0) (b) The registry is at the heart of the Windows operating system, explain with example what are the Registry Keys and Values. (Marks: 2.0) (c) Convert the IPv4 address of 192.168.120.30 to its equivalent IPv6. (Marks: 1.0) (d) Explain the scenarios when each of these tools should be used while diagnosing (Marks: 2.0) problems in a network i) PING ii) TRACERT.
Step by Step Solution
3.45 Rating (152 Votes )
There are 3 Steps involved in it
a Full Stealth This feature helps a firewall remain invisible to potential attackers by not respondi... View full answer

Get step-by-step solutions from verified subject matter experts


