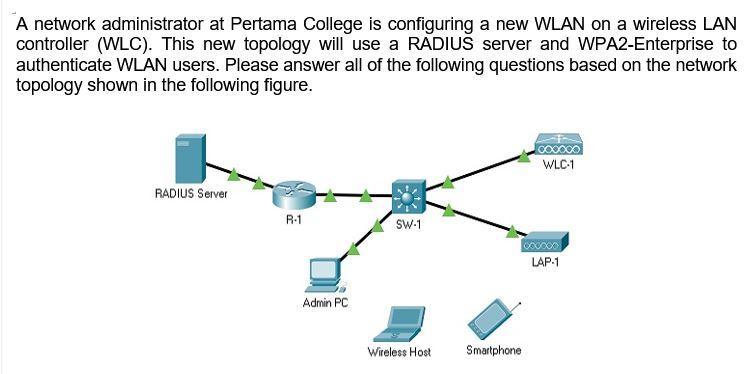
A network administrator at Pertama College is configuring a new WLAN on a wireless LAN controller...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
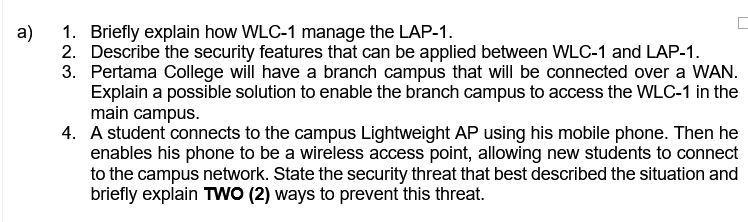
A network administrator at Pertama College is configuring a new WLAN on a wireless LAN controller (WLC). This new topology will use a RADIUS server and WPA2-Enterprise to authenticate WLAN users. Please answer all of the following questions based on the network topology shown in the following figure. WLC-1 RADIUS Server R-1 SW-1 000xxx LAP-1 Admin PC Wireless Host Smartphone a) 1. Briefly explain how WLC-1 manage the LAP-1. 2. Describe the security features that can be applied between WLC-1 and LAP-1. 3. Pertama College will have a branch campus that will be connected over a WAN. Explain a possible solution to enable the branch campus to access the WLC-1 in the main campus. 4. A student connects to the campus Lightweight AP using his mobile phone. Then he enables his phone to be a wireless access point, allowing new students to connect to the campus network. State the security threat that best described the situation and briefly explain TWO (2) ways to prevent this threat. A network administrator at Pertama College is configuring a new WLAN on a wireless LAN controller (WLC). This new topology will use a RADIUS server and WPA2-Enterprise to authenticate WLAN users. Please answer all of the following questions based on the network topology shown in the following figure. WLC-1 RADIUS Server R-1 SW-1 000xxx LAP-1 Admin PC Wireless Host Smartphone a) 1. Briefly explain how WLC-1 manage the LAP-1. 2. Describe the security features that can be applied between WLC-1 and LAP-1. 3. Pertama College will have a branch campus that will be connected over a WAN. Explain a possible solution to enable the branch campus to access the WLC-1 in the main campus. 4. A student connects to the campus Lightweight AP using his mobile phone. Then he enables his phone to be a wireless access point, allowing new students to connect to the campus network. State the security threat that best described the situation and briefly explain TWO (2) ways to prevent this threat.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Samilla works in a human resource office as a training consultant. With each round of new employees, she develops and stages programs during the first few days of employment to help the new employees...
-
QUIZ... Let D be a poset and let f : D D be a monotone function. (i) Give the definition of the least pre-fixed point, fix (f), of f. Show that fix (f) is a fixed point of f. [5 marks] (ii) Show that...
-
The new line character is utilized solely as the last person in each message. On association with the server, a client can possibly (I) question the situation with a client by sending the client's...
-
A city levies property taxes of $2 billion in June 2015for its Fiscal year beginning July 1, 2015. The taxes are due by January 31, 2016. The following (in millions) indicates actual and anticipated...
-
Explain how a price-segmentation fence involving a customer characteristic differs from one involving a characteristic of the purchase situation.
-
List at least three features of eukaryotic cells that clearly differentiate them from prokaryotic cells. What are histones and what do they do?
-
An increasing number of large groups now ask their top managers to invest a large amount of their personal wealth (often more than 40%) in company shares. What is the theory behind this type of...
-
What is the fundamental motivation behind portfolio theory? That is, what are people trying to achieve by investing in portfolios of stocks rather than in a few individual stocks or in debt? What...
-
4) Find the first 4 nonzero terms of the power series around the origin for the following functions., a) 1 - x Show Transcribed Text b) - 1
-
Record your responses on the spreadsheet template. 2014 February 1 - Brady and Manning decide to start up a partnership. Brady brings in $10 000 cash and equipment costing $60 000, with $17 000 in...
-
Current Attempt in Progress Carla Vista Company purchases a licence from Redo Industries for the right to manufacture and sell products using Redo's processes and technologies. Carla Vista estimates...
-
A 1940 case, Maryland Casualty Co. v. jonathon Cook, illustrates that: a. Auditors are responsible to detect material embezzlements. b. Auditors are culpable to clients who carry surety bonds on...
-
An auditor may be held liable under the Securities Act of 1933 for materially false or misleading financial statements if the security purchaser: a. Can establish reliance on the registration...
-
Accountants' liability to third parties under common law: a. Has not changed substantially over the years. b. Is identical to accountants' liability under the Securities Act of 1933. c. Is identical...
-
Which of the following, if material, would be a fraud? a. Errors in the application of accounting principles. b. Clerical errors in accounting data underlying the financial statements. c....
-
The Foreign Corrupt Practices Act requires that: a. Auditors of publicly held companies report all illegal payments to the SEC. b. Publicly held companies establish audit committees consisting only...
-
A 6 0 - day Treasury bill has a bank discount yield of 3 . 2 5 % . What is the effective annual rate?
-
Consider the following cash flows in Table P5.5. (a) Calculate the payback period for each project. (b) Determine whether it is meaningful to calculate a payback period for project D. (c) Assuming...
-
How can a company be sold by means of a capital increase?
-
At what price is a capital increase effected when made with an issue of subscription rights? When made without?
-
What is the consequence of a capital increase on EPS in the short term? In the long term?

Study smarter with the SolutionInn App


