Question: A network device assigns IP addresses for users with a netmask of 255.255.252.0 a. What are the IP address and its purposes? b. Find
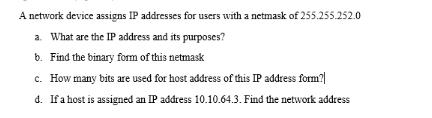
A network device assigns IP addresses for users with a netmask of 255.255.252.0 a. What are the IP address and its purposes? b. Find the binary form of this netmask c. How many bits are used for host address of this IP address form? d. If a host is assigned an IP address 10.10.64.3. Find the network address
Step by Step Solution
There are 3 Steps involved in it
Lets break down the questions one by one a What are the IP address and its purposes The IP address y... View full answer

Get step-by-step solutions from verified subject matter experts


