A network service provider assigns you a global routing prefix of 2001:db9:acad::/48. What is the compressed...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
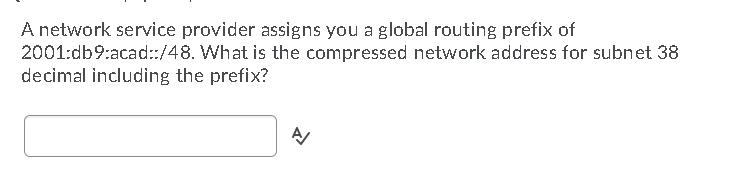
A network service provider assigns you a global routing prefix of 2001:db9:acad::/48. What is the compressed network address for subnet 38 decimal including the prefix? A A network service provider assigns you a global routing prefix of 2001:db9:acad::/48. What is the compressed network address for subnet 38 decimal including the prefix? A
Expert Answer:
Answer rating: 100% (QA)
The compressed network address for subnet 38 decimal including the prefix is 2001db9acad3848 ... View the full answer

Related Book For 

Business Data Networks and Security
ISBN: 978-0134817125
11th Edition
Authors: Raymond R. Panko, Julia L. Panko
Posted Date:
Students also viewed these computer network questions
-
A person pulls on the handle of a lawnmower with a force of 280 N. If the handle makes an angle of 40.0 degrees with the ground, calculate the coefficient of friction if the lawnmower weighs 350 N...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
a. What field in an IPv6 global uni-cast address corresponds to the network part of an IPv4 address? 3a1.) Which is NOT one of the three parts of a public IPv6 uni-cast address? a. Subnet ID b....
-
The atomic mass of 14c is 14.003242 u. Show that the decay of 14C is energetically possible, and calculate the energy released in the decay.
-
Pebbles dropped successively at the same point, into a water-channel flow of depth 65 cm, create two circular ripples, as in Fig. P10.7. From this information, estimate (a) The Froude number; and (b)...
-
If u(k) is an approximation to the solution to A u = b, then the residual vector r(k) = b - Au(k) measures how accurately the approximation solves the system. (a) Show that the Jacobi iteration can...
-
Figure 20.26 shows the flowsheet for a process for the production of G from A. The feed stream of A (entering through valve V-1) is mixed with a makeup stream of \(B\) (entering through valve...
-
An internal auditor should have a sound understanding of basic data processing concepts such as data organization and storage in order to adequately evaluate systems and make use of retrieval...
-
Cognito Crafts creates captivating carved creations for competent customers that crave cinching challenges. Cognito Crafts specializes in hand - assembled wooden puzzles. Anya, the sole craftsperson,...
-
KJJ Corp. was formed on October 10, 2001 by Kimberly Jen (123-45-6789), Jennifer James (234-56\(7890)\) and James \(\operatorname{Kim}(345-67-8901)\). It is a hardware store and is located at 175...
-
A firm with a 13% WACC is evaluating two projects for this year's capital budget. After-tax cash flows, including depreciation, are as follows: 0 ii 2 3 4 5 H Project M -$24,000 $8,000 $8,000 $8,000...
-
Obama and his wife have applied for a $350,000 mortgage to be amortized over 25 years at a fixed rate of 2.8% and a term of 5 years. Payments will be monthly. The Bank of Canada benchmark 5-year...
-
The shaft rotating with a uniform speed carries two discs with masses of 5 kg and 4 kg. The gravity center of each discs is 2.7 mm away from the rotation center. And the angle between two discs is...
-
Most organizations are just scratching the surface of what they can learn and accomplish through the analysis of unstructured text. Opportunities for large and small businesses, as well as...
-
How does the compensation vary by region and/o state?
-
Precise Definition: We say lim f(x) = L if for every e > 0 there is a 8 >0 such that whenever 0 0 and x' is real for negative x b then lim-0 Note: sgn(a)=1 if a>0 and sgn(a)=-1 if a <0. 1. lime &...
-
In a study it is observed that the right ovary ovulates more than the left, all are possible explanation for the cause except a) Anatomical difference between right and left side b) Difference in...
-
What are some of the various ways to implement an awareness program?
-
a. What are networked applications? b. Is the client always a browser? 11b.) The client program is nearly always a browser. a. True b. False c. Is the server always a webserver? 11c.) The server...
-
The sender uses HTTP to transmit mail. What standard or standards will the receiver use to download the message?
-
a. Why are hackers now focusing on taking over applications? 2a.) Typically, the most common way for an attacker to get extensive privileges on a computer is to ________. a. Take over an application...
-
What factors is a judge likely to consider when determining best interest?
-
What is the best interest standard?
-
What criticisms are commonly made about the best interest standard?

Study smarter with the SolutionInn App


