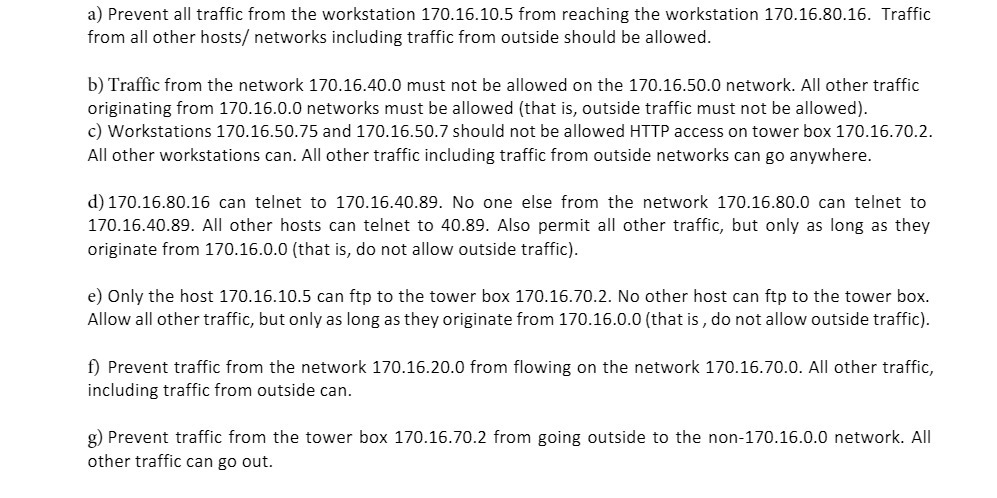
a) Prevent all traffic from the workstation 170.16.10.5 from reaching the workstation 170.16.80.16. Traffic from all...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
a) Prevent all traffic from the workstation 170.16.10.5 from reaching the workstation 170.16.80.16. Traffic from all other hosts/ networks including traffic from outside should be allowed. b) Traffic from the network 170.16.40.0 must not be allowed on the 170.16.50.0 network. All other traffic originating from 170.16.0.0 networks must be allowed (that is, outside traffic must not be allowed). c) Workstations 170.16.50.75 and 170.16.50.7 should not be allowed HTTP access on tower box 170.16.70.2. All other workstations can. All other traffic including traffic from outside networks can go anywhere. d) 170.16.80.16 can telnet to 170.16.40.89. No one else from the network 170.16.80.0 can telnet to 170.16.40.89. All other hosts can telnet to 40.89. Also permit all other traffic, but only as long as they originate from 170.16.0.0 (that is, do not allow outside traffic). e) Only the host 170.16.10.5 can ftp to the tower box 170.16.70.2. No other host can ftp to the tower box. Allow all other traffic, but only as long as they originate from 170.16.0.0 (that is, do not allow outside traffic). f) Prevent traffic from the network 170.16.20.0 from flowing on the network 170.16.70.0. All other traffic, including traffic from outside can. g) Prevent traffic from the tower box 170.16.70.2 from going outside to the non-170.16.0.0 network. All other traffic can go out. a) Prevent all traffic from the workstation 170.16.10.5 from reaching the workstation 170.16.80.16. Traffic from all other hosts/ networks including traffic from outside should be allowed. b) Traffic from the network 170.16.40.0 must not be allowed on the 170.16.50.0 network. All other traffic originating from 170.16.0.0 networks must be allowed (that is, outside traffic must not be allowed). c) Workstations 170.16.50.75 and 170.16.50.7 should not be allowed HTTP access on tower box 170.16.70.2. All other workstations can. All other traffic including traffic from outside networks can go anywhere. d) 170.16.80.16 can telnet to 170.16.40.89. No one else from the network 170.16.80.0 can telnet to 170.16.40.89. All other hosts can telnet to 40.89. Also permit all other traffic, but only as long as they originate from 170.16.0.0 (that is, do not allow outside traffic). e) Only the host 170.16.10.5 can ftp to the tower box 170.16.70.2. No other host can ftp to the tower box. Allow all other traffic, but only as long as they originate from 170.16.0.0 (that is, do not allow outside traffic). f) Prevent traffic from the network 170.16.20.0 from flowing on the network 170.16.70.0. All other traffic, including traffic from outside can. g) Prevent traffic from the tower box 170.16.70.2 from going outside to the non-170.16.0.0 network. All other traffic can go out.
Expert Answer:

Related Book For 

Project Management The Managerial Process
ISBN: 9781260570434
8th Edition
Authors: Eric W Larson, Clifford F. Gray
Posted Date:
Students also viewed these computer network questions
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
The following are some examples of typical business transactions: 1. Purchased office equipment on credit. 2. The owner contributed capital. 3. Purchased office furniture for cash. 4. Received...
-
Roche and Young, CAs, are preparing their service revenue (sales) budget for 2012. Their practice is divided into three departments: auditing, tax, and consulting. Billable hours for each department,...
-
What does a customhouse broker do?
-
In testing cutoff for purchases and payables at December 31, an auditor is confronted with the following four scenarios. Which of the four most likely represents a cutoff error, requiring that the...
-
Dont tell me weve lost another bid! exclaimed Sandy Kovallas, president of Lenko Products, Inc. Im afraid so, replied Doug Martin, the operations vice president. One of our competitors underbid us by...
-
You are asked to review amounts paid to employees at a state agency. You do not have sufficient time to review all the employees listed below in detail; but you do have time to look at supporting...
-
Table, from a General Social Survey, relates responses on R = religious service attendance (1 = at most a few times a year, 2 = at least several times a year), P = political views (1 = liberal, 2 =...
-
Recall your earliest memories of money and its meaning. Identify one word to associate with money and explain why you chose that word?
-
The scores on a university entrance exam are normally distributed with a mean of 72% and a standard deviation of 15. a. Find the probability that a student taking the entrance exam will score below...
-
A tourism magazine surveyed 5,000 people for their expected travel plans in the following year. The response rate of the survey is seventy-five per cent. Forty-five per cent of the respondents of the...
-
Trevs Gardening Services purchased a trailer on 1 July 2019 for $26 200. It was estimated to have a useful life of 5 years and a residual value at the end of that time of $2800. Required (a) What is...
-
At the end of the first year of operations, Arch Etec, owner of Architect Designs, engaged you to prepare yearly financial statements for the year ended 30 June 2019, on both the cash basis and the...
-
Karen Broderick commenced business on 1 July 2018. On 30 June 2019, she found that she had written off debts amounting to $1875. In addition, she found it necessary to create an allowance for...
-
Q 10: Two very long parallel wires are traversed by the same current i, as shown. The following figure. Rank in ascending order the magnetic field modulus of the three points shown. P i P3 1. 2d GUDC
-
You've been asked to take over leadership of a group of paralegals that once had a reputation for being a tight-knit, supportive team, but you quickly figure out that this team is in danger of...
-
Which of the eight characteristics associated with positive synergy were evident in the case of the Redeem team?
-
How does having a product vision and using Scrum rituals help teams manage tension and conflict?
-
Given the following network, compute the early, late, and slack time for each activity. Clearly identify the critical path A Design 3 Lag 2 Legend ID ES EF SL Description SL LS Duration LF D Build...
-
For the conditions of Sample Problem 5/17, determine the angular acceleration of \(A C\) and the acceleration of \(A\) relative to the rotating slot in \(\operatorname{arm} O D\). Problem 5/17, The...
-
Aircraft \(B\) has a constant speed of \(150 \mathrm{~m} / \mathrm{s}\) as it passes the bottom of a circular loop of 400-m radius. Aircraft \(A\) flying horizontally in the plane of the loop passes...
-
Examples of random variables used in this chapter included (a) the sex of the next person you meet, (b) the number of times a wireless network fails, (c) the time it takes to commute to school, (d)...

Study smarter with the SolutionInn App