Question: A secure information system uses an advanced authentication mechanism through a username, password, and retina scan per user. For this purpose, the system stores
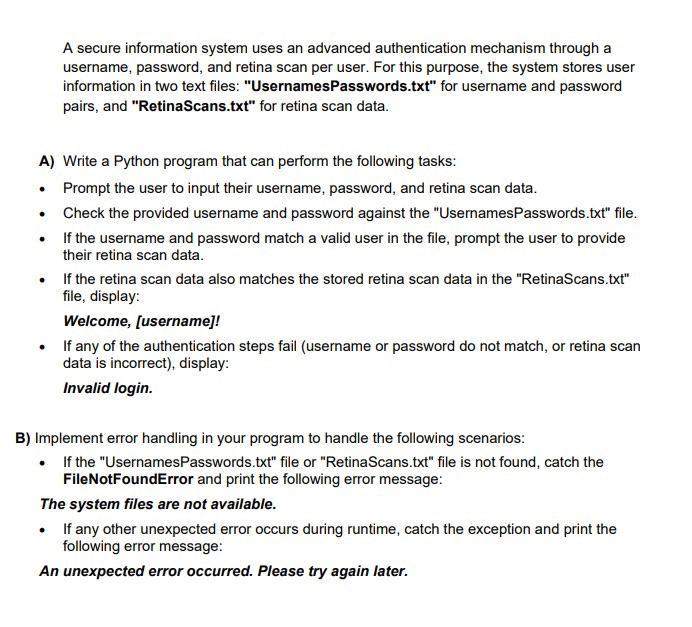
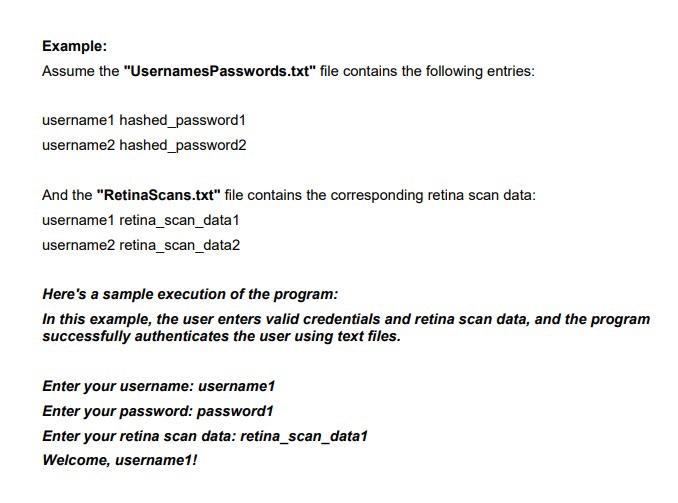
A secure information system uses an advanced authentication mechanism through a username, password, and retina scan per user. For this purpose, the system stores user information in two text files: "UsernamesPasswords.txt" for username and password pairs, and "RetinaScans.txt" for retina scan data. A) Write a Python program that can perform the following tasks: Prompt the user to input their username, password, and retina scan data. Check the provided username and password against the "UsernamesPasswords.txt" file. If the username and password match a valid user in the file, prompt the user to provide their retina scan data. If the retina scan data also matches the stored retina scan data in the "RetinaScans.txt" file, display: Welcome, [username]! If any of the authentication steps fail (username or password do not match, or retina scan data is incorrect), display: Invalid login. B) Implement error handling in your program to handle the following scenarios: If the "UsernamesPasswords.txt" file or "RetinaScans.txt" file is not found, catch the FileNotFoundError and print the following error message: The system files are not available. If any other unexpected error occurs during runtime, catch the exception and print the following error message: An unexpected error occurred. Please try again later. Example: Assume the "UsernamesPasswords.txt" file contains the following entries: username1 hashed_password1 username2 hashed_password2 And the "RetinaScans.txt" file contains the corresponding retina scan data: username1 retina_scan_data1 username2 retina_scan_data2 Here's a sample execution of the program: In this example, the user enters valid credentials and retina scan data, and the program successfully authenticates the user using text files. Enter your username: username1 Enter your password: password1 Enter your retina scan data: retina_scan_data1 Welcome, username1!
Step by Step Solution
3.42 Rating (155 Votes )
There are 3 Steps involved in it
Heres a Python program that fulfills the given requirements python def checkcredentialsusername pass... View full answer

Get step-by-step solutions from verified subject matter experts


