Question: A security analyst is investigating a potential breach. Upon gathering, documenting, and securing the evidence, which of the following actions is the NEXT step to
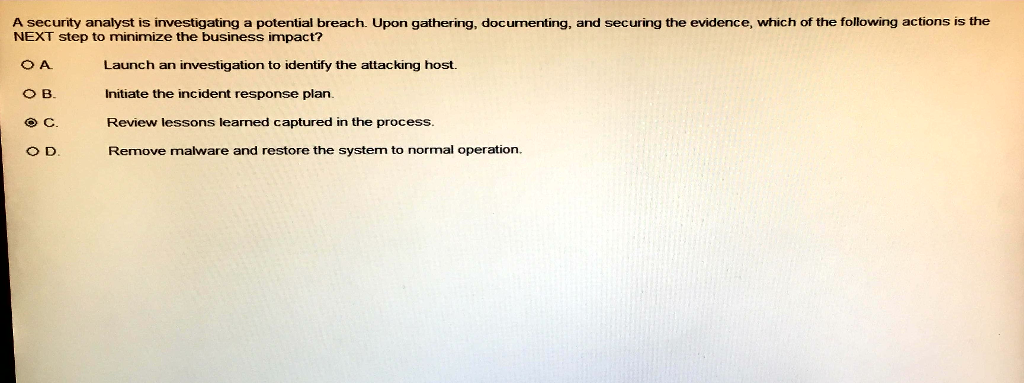
A security analyst is investigating a potential breach. Upon gathering, documenting, and securing the evidence, which of the following actions is the NEXT step to minimize the business impact? Launch an investigation to identify the attacking host. Initiate the incident response plan Review lessons learned captured in the process. Remove malware and restore the system to normal operation. B
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


