Question: A security analyst performs incident response activities after a recent security incident. They need to analyze a suspicious email attachment and verify the email's authentication
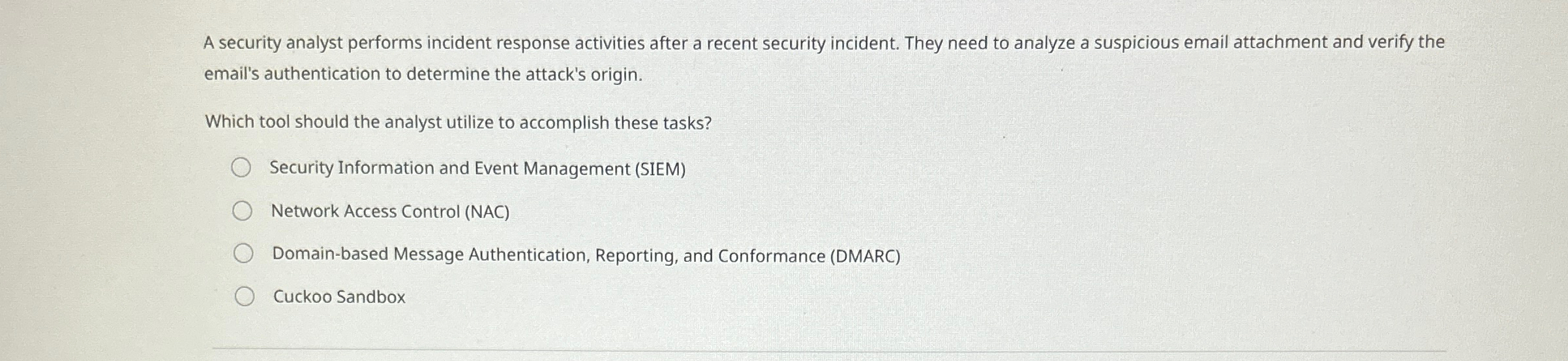
A security analyst performs incident response activities after a recent security incident. They need to analyze a suspicious email attachment and verify the email's authentication to determine the attack's origin.
Which tool should the analyst utilize to accomplish these tasks?
Security Information and Event Management SIEM
Network Access Control NAC
Domainbased Message Authentication, Reporting, and Conformance DMARC
Cuckoo Sandbox
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


