A service provider network has 4 provider edge (PE) routers and 2 provider (P) routers. It...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
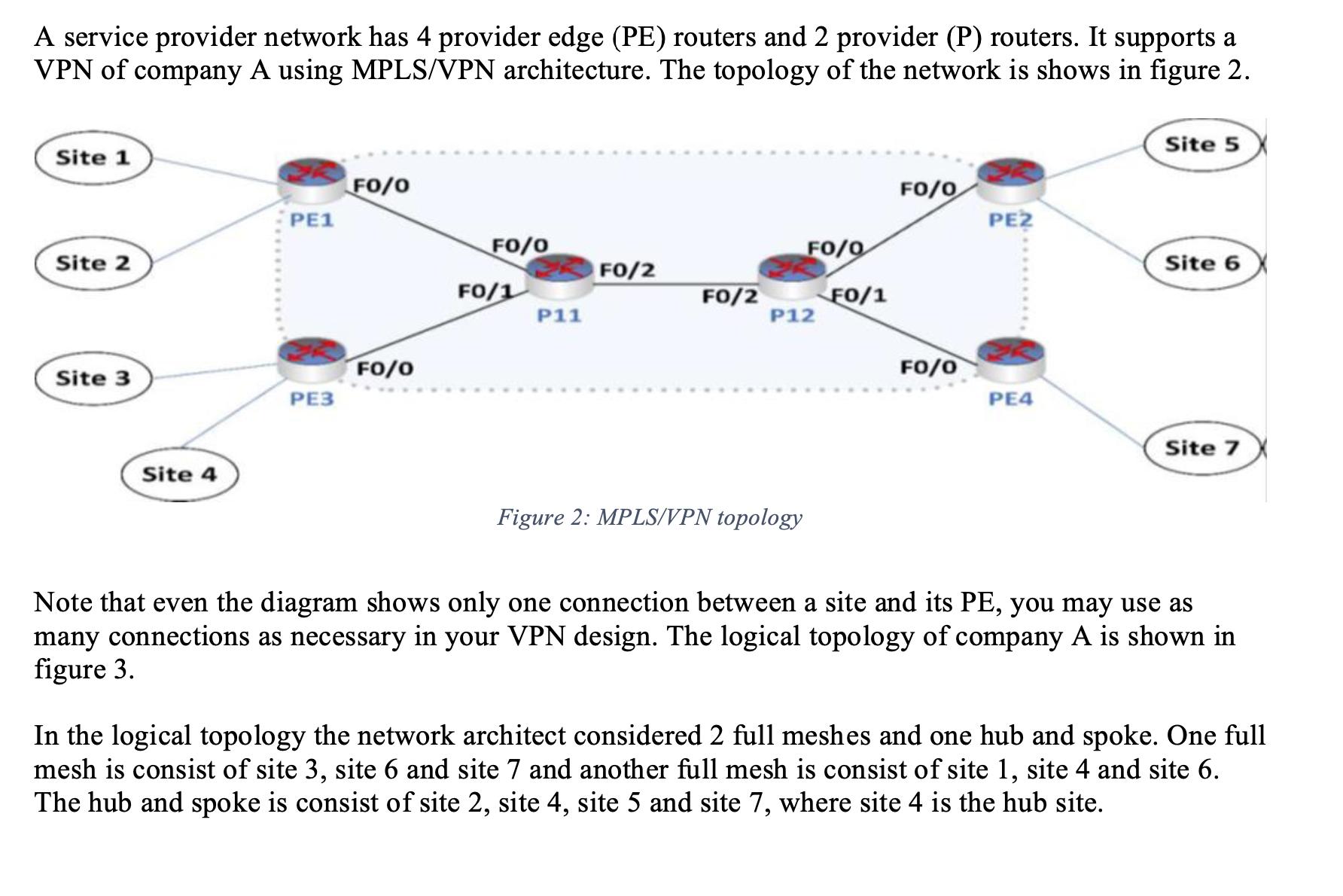
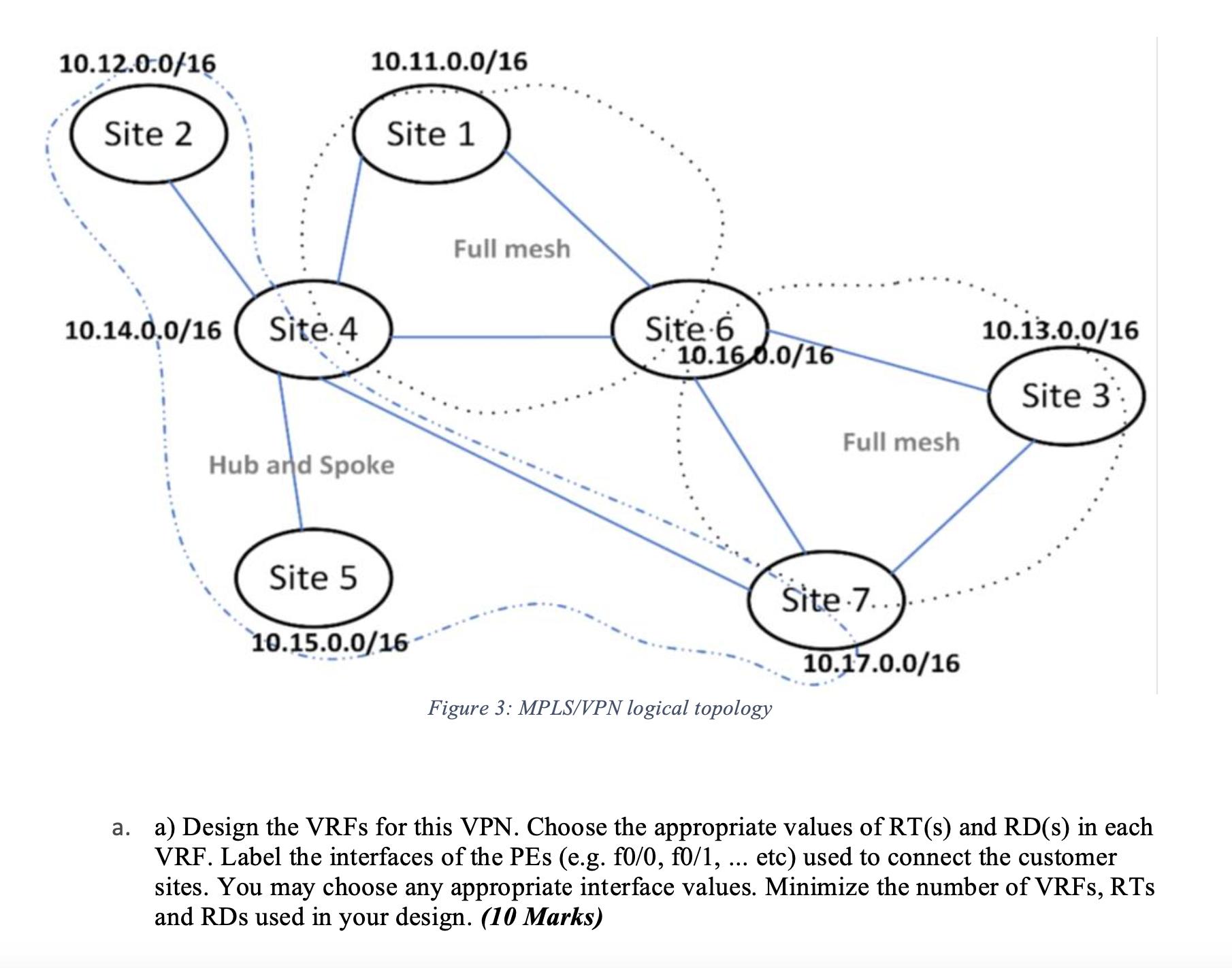
A service provider network has 4 provider edge (PE) routers and 2 provider (P) routers. It supports a VPN of company A using MPLS/VPN architecture. The topology of the network is shows in figure 2. Site 1 Site 2 Site 3 Site 4 PE1 PE3 FO/0 FO/0 FO/0 FO/1 P11 FO/2 FO/2 FO/0 P12 Figure 2: MPLS/VPN topology FO/1 FO/0 FO/0 PE2 PE4 Site 5 Site 6 Site 7 Note that even the diagram shows only one connection between a site and its PE, you may use as many connections as necessary in your VPN design. The logical topology of company A is shown in figure 3. In the logical topology the network architect considered 2 full meshes and one hub and spoke. One full mesh is consist of site 3, site 6 and site 7 and another full mesh is consist of site 1, site 4 and site 6. The hub and spoke is consist of site 2, site 4, site 5 and site 7, where site 4 is the hub site. 10.12.0.0/16 Site 2 10.14.0.0/16 Site 4 10.11.0.0/16 Site 5 Site 1 Hub and Spoke 10.15.0.0/16 Full mesh Site 6 10.160.0/16 Figure 3: MPLS/VPN logical topology Full mesh Site 7.. 10.17.0.0/16 10.13.0.0/16 Site 3: a. a) Design the VRFs for this VPN. Choose the appropriate values of RT(s) and RD(s) in each VRF. Label the interfaces of the PEs (e.g. f0/0, f0/1, ... etc) used to connect the customer sites. You may choose any appropriate interface values. Minimize the number of VRFs, RTS and RDs used in your design. (10 Marks) A service provider network has 4 provider edge (PE) routers and 2 provider (P) routers. It supports a VPN of company A using MPLS/VPN architecture. The topology of the network is shows in figure 2. Site 1 Site 2 Site 3 Site 4 PE1 PE3 FO/0 FO/0 FO/0 FO/1 P11 FO/2 FO/2 FO/0 P12 Figure 2: MPLS/VPN topology FO/1 FO/0 FO/0 PE2 PE4 Site 5 Site 6 Site 7 Note that even the diagram shows only one connection between a site and its PE, you may use as many connections as necessary in your VPN design. The logical topology of company A is shown in figure 3. In the logical topology the network architect considered 2 full meshes and one hub and spoke. One full mesh is consist of site 3, site 6 and site 7 and another full mesh is consist of site 1, site 4 and site 6. The hub and spoke is consist of site 2, site 4, site 5 and site 7, where site 4 is the hub site. 10.12.0.0/16 Site 2 10.14.0.0/16 Site 4 10.11.0.0/16 Site 5 Site 1 Hub and Spoke 10.15.0.0/16 Full mesh Site 6 10.160.0/16 Figure 3: MPLS/VPN logical topology Full mesh Site 7.. 10.17.0.0/16 10.13.0.0/16 Site 3: a. a) Design the VRFs for this VPN. Choose the appropriate values of RT(s) and RD(s) in each VRF. Label the interfaces of the PEs (e.g. f0/0, f0/1, ... etc) used to connect the customer sites. You may choose any appropriate interface values. Minimize the number of VRFs, RTS and RDs used in your design. (10 Marks)
Expert Answer:

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
1. House-painting is a job that can be done by several people working si- multaneously, so we can measure the amount of work done in "staff-hours." Consider a house-painting business run by some...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Which of the following is not true regarding a promissory note? a. Promissory notes may not be transferred to another party by endorsement. b. Promissory notes may be sold to another party. c....
-
Research and discuss the backgrounds of one woman and one man presently working in Local Politics from a similar locality/state Research and Report the Backgrounds of One Woman and One Man Currently...
-
Do you think society's expectations for corporate social responsibility will change in the next decade? Explain.
-
Partnerships have operating expenses each month. Advertising, depreciation, and rent expense are examples of those operating expenses. Controlling these expenses affects the net income of the...
-
During the 2011 annual accounting period, BSP Company completed the following transactions: (a) On January 1, 2011, purchased a patent for $28,000 cash (estimated useful life, seven years). (b) On...
-
NEU bonds issued on March 8 , 2 0 2 3 have a par value of VND 1 0 0 , 0 0 0 with a term of 5 years. Bonds pay interest and principal once at maturity with coupon interest rate of 1 5 % / year ....
-
Problem #12: Planning and Control Don't-Cha-Wanna-a-Coffee, a large-scale coffee company that has a chain of 125 retail coffee stores throughout New England, was embroiled in an ethics scandal 3...
-
Maxie and Bianca own Umbrella Corporation, LLC, and they are the top producers of black market Goucher Basketball jerseys. Despite prior team records, these jerseys are in hot demand. Maxie and...
-
Mr. John Nicos, financial manager of Cbles Chat Lte (CCL), must choose between two investment projects intended to increase the company's capacity to meet growing customer demand. The Refit project...
-
Texas Boots Inc. is considering the production of a new line of boots. Based on preliminary market research, management has decided that each pair of boots should be priced at $300. Furthermore,...
-
Let s say you are buying a home, putting 1 5 % down and financing the rest with a 3 0 - year mortgage. The price of the home you are buying is $ 1 , 0 0 0 , 0 0 0 and the APR is 6 . 8 5 % . 1 ....
-
Determine the stability of the sytem whose zero-pole plot is shown Stable Marginally stable Unstable 7 where all poles are of multiplicity 1.
-
The cost of flood damage from significant storms varies as a function of the severity of the storm. Estimate the expected flood damage due to the next significant storm. Flood Flow, Million Acre-Ft...
-
In January, Tongo, Incorporated, a branding consultant, had the following transactions. a. Received $18,400 cash for consulting services rendered in January. b. Issued common stock to investors for...
-
Write electron configurations for the following ions, and determine which have noble-gas configurations: (a) Cd2+ (b) p3- (c) Zr4+ (d) Ru3+ (e) As3- (f) Ag+
-
True or False: The Domain Name System (DNS) is a function of the World Wide Web that converts a URL (Uniform Resource Locator) such as www.course.com into the IP address of the Web server host.
-
True or False: Signature-based IDPS technology is widely used because many attacks have clear and distinct signatures.
-
Recall that everyone does not have carte blanche access to all data that is transmitted, processed, or stored within or outside an organization. Comprehend that security is never an absolute as it is...
-
Fowler Corporation is engaged in the manufacture and distribution of a variety of chemicals. In analyzing the financial statements of this corporation, why would you want to refer to the ratios and...
-
Net sales of the Oneida General Store have been increasing at a reasonable rate, but net income has been declining steadily as a percentage of these sales. What appears to be the problem?
-
Felker, Inc., experiences a considerable seasonal variation in its business. The high point in the year's activity comes in November, the low point in July. During which month would you expect the...

Study smarter with the SolutionInn App


