A solution to the critical-section problem must satisfy the following three requirements: Mutual Exclusion, Progress, and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
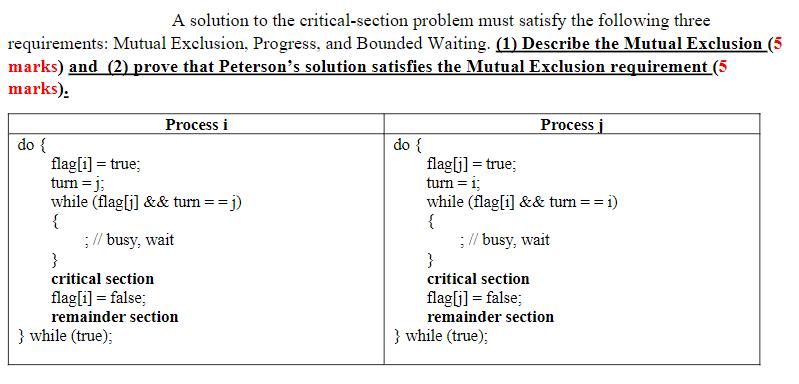
A solution to the critical-section problem must satisfy the following three requirements: Mutual Exclusion, Progress, and Bounded Waiting. (1) Describe the Mutual Exclusion (5 marks) and (2) prove that Peterson's solution satisfies the Mutual Exclusion requirement (5 marks): do { Process i flag[i]= true; turn = j; while (flag[j] && turn == j) { ; // busy, wait } critical section flag [i] = false; remainder section } while (true); do { Process j flag[j] = true; turn = i; while (flag[i] && turn ==1) { ; // busy, wait critical section flag[j] = false; remainder section } while (true); A solution to the critical-section problem must satisfy the following three requirements: Mutual Exclusion, Progress, and Bounded Waiting. (1) Describe the Mutual Exclusion (5 marks) and (2) prove that Peterson's solution satisfies the Mutual Exclusion requirement (5 marks): do { Process i flag[i]= true; turn = j; while (flag[j] && turn == j) { ; // busy, wait } critical section flag [i] = false; remainder section } while (true); do { Process j flag[j] = true; turn = i; while (flag[i] && turn ==1) { ; // busy, wait critical section flag[j] = false; remainder section } while (true);
Expert Answer:
Answer rating: 100% (QA)
1 Mutual Exclusion Mutual Exclusion is a property of a solution to the criticalsection problem that ensures that at most one process is executing its ... View the full answer

Related Book For 

Operating Systems Internals and Design Principles
ISBN: 978-0133805918
8th edition
Authors: William Stallings
Posted Date:
Students also viewed these programming questions
-
Find the y-intercept of f(x) = 7(x+2)+1. (Enter your answer as a ordered pair.) Provide your answer below: The y-intercept is
-
Concurrent or parallel execution can contribute to issues involving the integrity of data shared by several processes. Furthermore, the growing importance of multicore systems has brought an...
-
Most rain gauge networks (such as the CoCORAHS network) have rainfall totals measured every 24 hours, providing a single measurement for the day. Describe why it is difficult to monitor rainfall...
-
This section contains 6 questions. Questions 83 to 88 have four statements (A, B C and D) given in Column I and four statements (p, q, r and s) in Column II. Any given statement in Column I can have...
-
A researcher is interested in whether allowing employees to wear casual clothing will increase the likelihood that employees come to work on time. She observes that the probability of an employee...
-
Assume all of the same facts and scenarios as E 12-30, except that Bloom Corporation classifies their Taylor investment as AFS. In E12-30 Bloom Corporation purchased $1,000,000 of Taylor Company 5%...
-
Good Times Express Company had retained earnings of \(\$ 160\) million at December 31, 2006. The company reported these figures for 2007: Requirement Beginning with net income, prepare a combined...
-
Cooperative enterprises are collectively owned, and their affairs are directed through shared governance. Use the preceding theory to discuss the management of some cooperative enterprises with which...
-
. Project Information You estimate the investment required to undertake the project will be equal to 20% of the Property Plant and Equipment (PPE) shown in the Core Lithium Ltd 2023 Balance Sheet...
-
How would you detect the distribution of the constituents of human hair with a diameter of about 80 m using methods of vibrational spectroscopy? Describe the use of at least two different approaches;...
-
Write a program: Supermarket Promotions Even though this assignment carries a lot of points, it's smaller and easier than the last two assignments. Hopefully this will give you an opportunity to get...
-
Describe how one important defect in the consideration rules has been remedied by statute in five of the provinces.
-
What is the difference between a public and a private nuisance?
-
What strategies does business use to manage legal risk?
-
Why is gratitude not a sufficient consideration to bind a promisor?
-
Distinguish the civil law system from the common law system.
-
Indicate how many flip-flops 3, (b) mod-6, (c) mod-9. are required to construct each of the following counters: (a) mod-
-
A genetically engineered strain of Escherichia coli (E. coli) is used to synthesize human insulin for people suffering from type I diabetes mellitus. In the following simplified reaction scheme,...
-
To implement the various placement algorithms discussed for dynamic partitioning (Section 7.2), a list of the free blocks of memory must be kept. For each of the three methods discussed (best-fit,...
-
The program execution of Figure is described in the text using six steps. Expand this description to show the use of the MAR and MBR. Fetch stage Execute stage CPU registers Memory CPU registers emo...
-
Write the binary translation of the logical address 0001010010111010 under the following hypothetical memory management schemes, and explain your answer: a. A paging system with a 256-address page...
-
Arrange the three main statement of financial position items (assets, liabilities, equity) as an equation.
-
A statement of financial position appears to show what a business is worth. What are the main problems with this statement?
-
Which of the following are shown on a statement of financial position: assets; expenses; liabilities; sales; share capital; profit for the year?

Study smarter with the SolutionInn App


