Question: A suspicious program is run in a controlled environment, where a security analyst monitors the program's execution to track the effect it has on computer
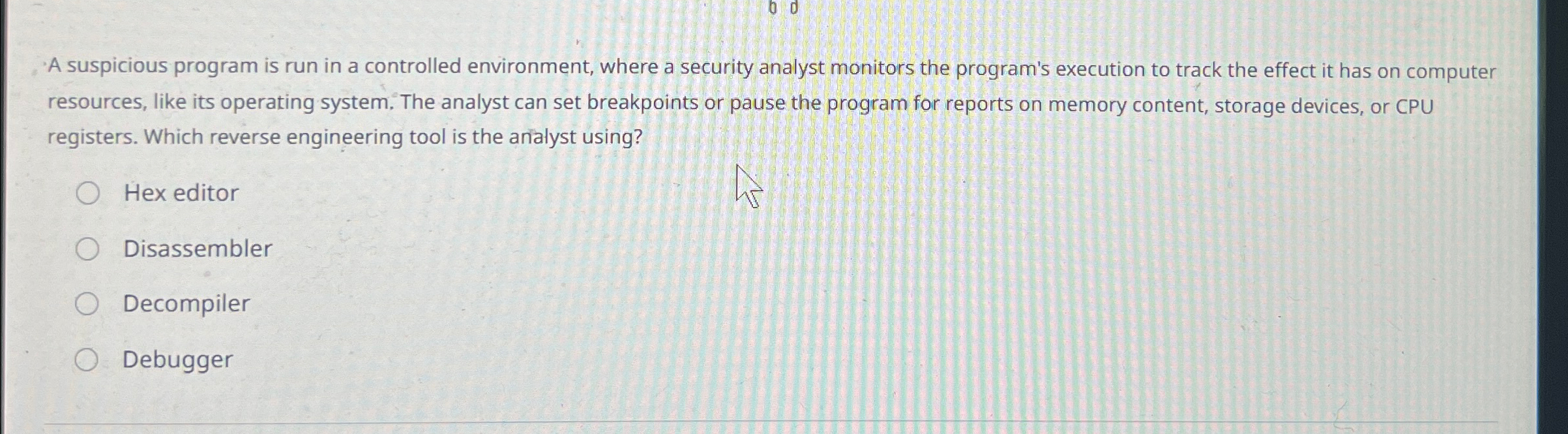
A suspicious program is run in a controlled environment, where a security analyst monitors the program's execution to track the effect it has on computer resources, like its operating system. The analyst can set breakpoints or pause the program for reports on memory content, storage devices, or CPU registers. Which reverse engineering tool is the arialyst using?
Hex editor
Disassembler
Decompiler
Debugger
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


