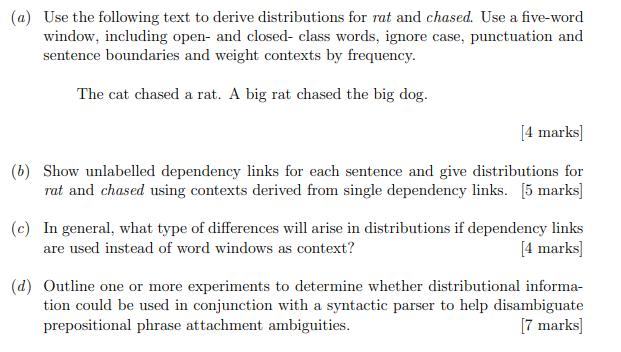
(a) Use the following text to derive distributions for rat and chased. Use a five-word window,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
(a) Use the following text to derive distributions for rat and chased. Use a five-word window, including open- and closed- class words, ignore case, punctuation and sentence boundaries and weight contexts by frequency. The cat chased a rat. A big rat chased the big dog. [4 marks] (b) Show unlabelled dependency links for each sentence and give distributions for rat and chased using contexts derived from single dependency links. [5 marks] (c) In general, what type of differences will arise in distributions if dependency links are used instead of word windows as context? [4 marks] (d) Outline one or more experiments to determine whether distributional informa- tion could be used in conjunction with a syntactic parser to help disambiguate prepositional phrase attachment ambiguities. [7 marks] (a) Use the following text to derive distributions for rat and chased. Use a five-word window, including open- and closed- class words, ignore case, punctuation and sentence boundaries and weight contexts by frequency. The cat chased a rat. A big rat chased the big dog. [4 marks] (b) Show unlabelled dependency links for each sentence and give distributions for rat and chased using contexts derived from single dependency links. [5 marks] (c) In general, what type of differences will arise in distributions if dependency links are used instead of word windows as context? [4 marks] (d) Outline one or more experiments to determine whether distributional informa- tion could be used in conjunction with a syntactic parser to help disambiguate prepositional phrase attachment ambiguities. [7 marks] (a) Use the following text to derive distributions for rat and chased. Use a five-word window, including open- and closed- class words, ignore case, punctuation and sentence boundaries and weight contexts by frequency. The cat chased a rat. A big rat chased the big dog. [4 marks] (b) Show unlabelled dependency links for each sentence and give distributions for rat and chased using contexts derived from single dependency links. [5 marks] (c) In general, what type of differences will arise in distributions if dependency links are used instead of word windows as context? [4 marks] (d) Outline one or more experiments to determine whether distributional informa- tion could be used in conjunction with a syntactic parser to help disambiguate prepositional phrase attachment ambiguities. [7 marks]
Expert Answer:
Answer rating: 100% (QA)
It looks like youve provided an image with a series of questions related to computational linguistics particularly focusing on distributional semantics and syntactic parsing Lets address each question ... View the full answer

Related Book For 

Chemistry The Central Science
ISBN: 978-0321696724
12th edition
Authors: Theodore Brown, Eugene LeMay, Bruce Bursten, Catherine Murphy, Patrick Woodward
Posted Date:
Students also viewed these programming questions
-
ttth Suppose that the sequence of bags {Bn | n N} is recursively enumerated by the computable function e(n, x) = fn(x), [7 marks] Hence prove that the set of all recursive bags cannot be recursively...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
QUIZ... Let D be a poset and let f : D D be a monotone function. (i) Give the definition of the least pre-fixed point, fix (f), of f. Show that fix (f) is a fixed point of f. [5 marks] (ii) Show that...
-
In order to have $391,185 in 26 years, how much needs to be deposited each month into a bank account whose annual rate is 1.8% with monthly compounding?
-
Firm 1 has a capital structure with 20% debt and 80% equity. Firm 2s capital structure consists of 50% debt and 50% equity. Both firms pay 7% annual interest on their debt. Finally, suppose that both...
-
Discuss precisely the number of matters: 1. What makes the flow of energy through ecosystems fundamentally different from the flow of nutrients? 2. How do food chains and food webs differ? Which is...
-
2-1. What is the difference between a for-profit and a nonprofit organization?
-
Farrah and Davidson had beginning capital balances of $25,000 and $20,000, respectively. The two partners fail to agree on a profit-and-loss ratio. For the first month (June 2012), the partnership...
-
please help Drake Corporation is reviewing an investment proposal. The initial cost and estimates of the book value of the investment at the end of each year, the net cash flows for each year, and...
-
Barnett Industries, Inc., issued $600,000 of 8% bonds on January 1, 2019. The bonds pay interest semiannually on July 1 and January 1. The maturity date on these bonds is December 31, 2028. The firm...
-
Ratchet Ltd expects to sell 30,000 units this year. The selling price is set at $25 per unit. The variable cost per unit is $12 and annual fixed cost is $345,000. Assume a tax rate of 28%. Required:...
-
Financial Statement Items Identify the financial statement (or statements) in which each of the following items would appear: income statement (IS), statement of stockholders' equity (SSE), balance...
-
Recall from Chapter 4 that Tiger Stripe Copy Center is a small business located near a large university campus. Tiger Stripe Copy offers a range of services to walk-in customers, including passport...
-
Accounting Processes Identify the following processes as either measuring or communicating. a. Prepare financial statements for the entity b. Identify relevant economic activities of the entity c....
-
To estimate future values of the cost indices, one is tempted to assume that the average value for the year occurred at midyear (June 30-July 1) and that the linear fit to the recent data can be...
-
Reston Manufacturing Corporation produces a cosmetic product in three consecutive processes. The costs of Department | for May 2016 were as follows: Department | handled the following units during...
-
Check my work Nathan Herrmann has completed the basic format to be used in preparing the statement of cash flows (indirect method) for CEO Consultants. Listed below in random order are line items to...
-
Prairie Outfitters, Inc., a retailer, accepts paymnent through credit cards. During August, credit card sales amounted to $12,000. The processor charges a 3% fee. Assuming that the credit card...
-
Consider the following reaction between mercury (II) chloride and oxalate ion: 2 HgCI2(aq) + C2O42- (aq) 2 CIË (aq) + 2 CO2(g) + Hg2CI2(s) The initial rate of this reaction was determined for...
-
Consider the reaction of peroxydisulfate ion (S2O8-2) with iodide ion (I) in aqueous solution: S2O82- (aq) + 3 I (aq) - 2 SO42- (aq) + I3(aq) At a particular temperature the initial rate of...
-
Little is known about the properties of astatine, At, because of its rarity and high radioactivity. Nevertheless, it is possible for us to make many predictions about its properties. (a) Do you...
-
1. The chapter discusses three classes of factors (people, structure, and technology) in determining what should be changed. With P&Gs eStore, how have each of these factors been affected?
-
One of the major challenges facing business in the twenty-first century is the rapid pace of changing technology. How would these challenges directly impact a company like Homestar runner?
-
3. How do the Chapman brothers measure job performance?

Study smarter with the SolutionInn App