Question: a. What would be the financial advantage for a malware designer to create lots of different malicious code instances that all exploit the same
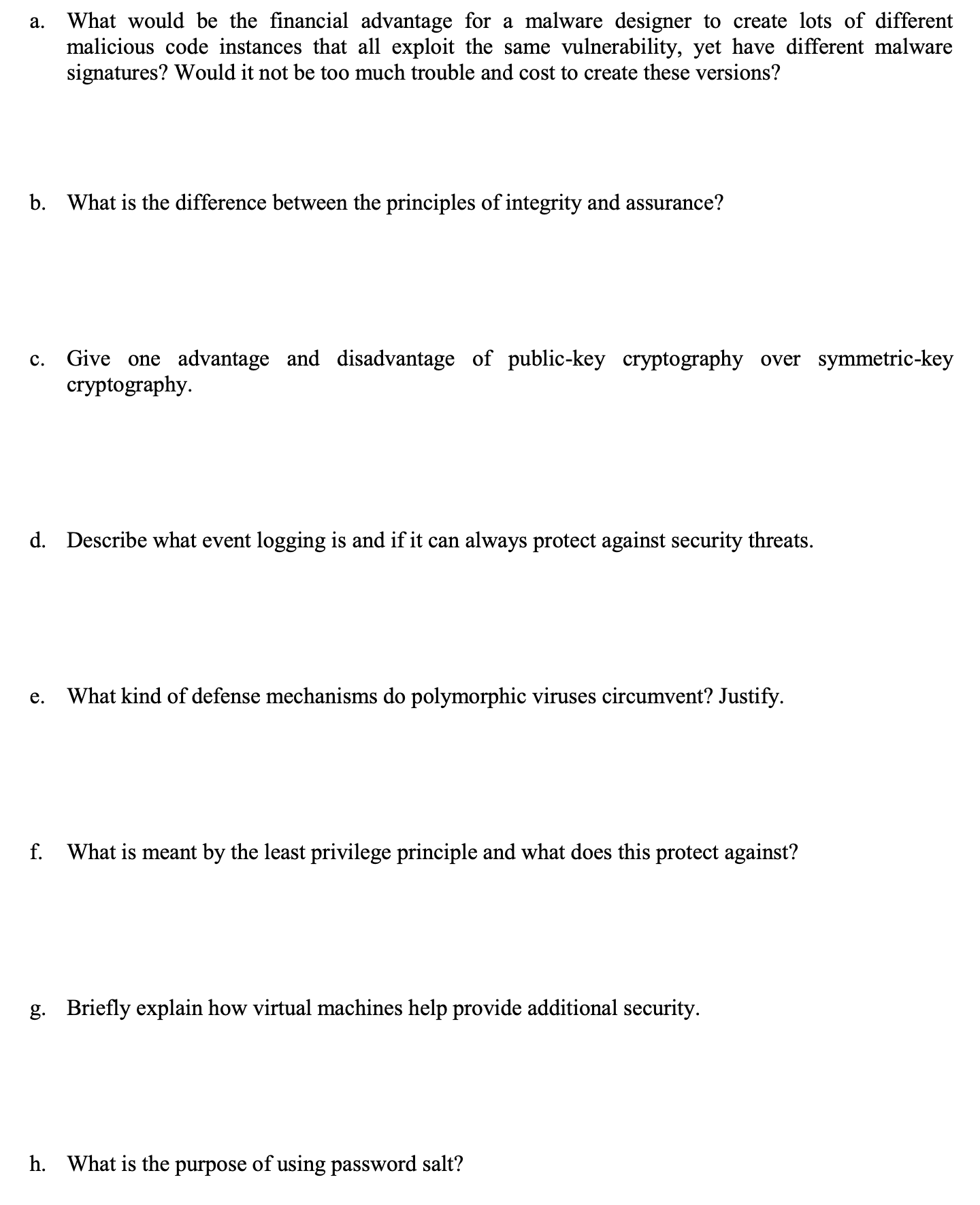
a. What would be the financial advantage for a malware designer to create lots of different malicious code instances that all exploit the same vulnerability, yet have different malware signatures? Would it not be too much trouble and cost to create these versions? b. What is the difference between the principles of integrity and assurance? C. Give one advantage and disadvantage of public-key cryptography over symmetric-key cryptography. d. Describe what event logging is and if it can always protect against security threats. e. What kind of defense mechanisms do polymorphic viruses circumvent? Justify. f. What is meant by the least privilege principle and what does this protect against? g. Briefly explain how virtual machines help provide additional security. h. What is the purpose of using password salt?
Step by Step Solution
3.44 Rating (154 Votes )
There are 3 Steps involved in it
a Financial Advantage for Malware Designer Advantage Creating multiple instances with different signatures makes it harder for antivirus software to d... View full answer

Get step-by-step solutions from verified subject matter experts


