Accountants are often called upon to create an inventory of organizational risks. This may include items...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
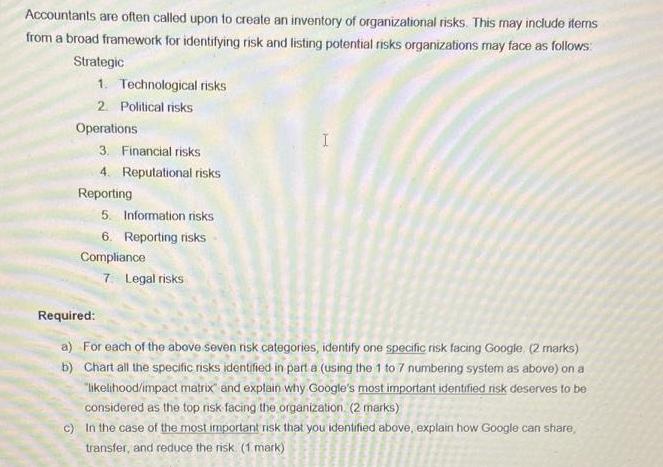
Accountants are often called upon to create an inventory of organizational risks. This may include items from a broad framework for identifying risk and listing potential risks organizations may face as follows: Strategic 1. Technological risks 2. Political risks Operations 3. Financial risks 4. Reputational risks Reporting 5. Information risks 6. Reporting risks Compliance 7 Legal risks I Required: b) a) For each of the above seven nsk categories, identify one specific risk facing Google (2 marks) Chart all the specific risks identified in part a (using the 1 to 7 numbering system as above) on a "likelihood/impact matrix and explain why Google's most important identified risk deserves to be considered as the top risk facing the organization (2 marks) c) In the case of the most important risk that you identified above, explain how Google can share, transfer, and reduce the risk (1 mark) Accountants are often called upon to create an inventory of organizational risks. This may include items from a broad framework for identifying risk and listing potential risks organizations may face as follows: Strategic 1. Technological risks 2. Political risks Operations 3. Financial risks 4. Reputational risks Reporting 5. Information risks 6. Reporting risks Compliance 7 Legal risks I Required: b) a) For each of the above seven nsk categories, identify one specific risk facing Google (2 marks) Chart all the specific risks identified in part a (using the 1 to 7 numbering system as above) on a "likelihood/impact matrix and explain why Google's most important identified risk deserves to be considered as the top risk facing the organization (2 marks) c) In the case of the most important risk that you identified above, explain how Google can share, transfer, and reduce the risk (1 mark)
Expert Answer:
Answer rating: 100% (QA)
Answer Required identify 2 3 0 Technical risks busines Any important harm to ... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these accounting questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Research various global financial services organizations (for example, UBS AG, E-Trade, Schwab, ING, Bank of America, HSBC, RBS) through their company websites and other publicly available...
-
A man drops a stone from a high bridge and hears it strike the water below exactly 4 s later. (a) Estimate the distance to the water based on the assumption that the travel time for the sound to...
-
On the last day of March, Brunswick Corporation borrowed $360,000 on a bank note for 60 days at 10 percent interest. Assume that interest is stated separately. Prepare the following journal entries:...
-
An emf source with E = 120V,a resistor with R = 50.0, and a capacitor with C = 4.00 F are connected in series. As the capacitor charges, when the current in the resistor is0.900 A, what is the...
-
The following data refer to a compound impulse turbine having two rows of moving blades and one row of fixed blades in between them. Nozzle angle \(=15^{\circ}\), Exit velocity of steam from the...
-
Cutler Corporation is authorized to issue 10,000 shares of common stock. It sells 6,000 shares at $19 per share. Required Record the sale of the common stock, given the following independent...
-
An arrow is shot from a height of 1.95 m toward a cliff of height H . It is shot with a velocity of 25 m/s at an angle of 60 above the horizontal. It lands on the top edge of the cliff 3.67 s later....
-
Following are the income statement and balance sheet for Medtronic PLC. Consolidated Statement of Income, 12 Months Ended ($ millions) April 26, 2019 Net Sales $30,557 Costs and expenses Cost of...
-
Find a formula for the sum of n terms. Use the formula to find the limit as n . lim Need Help? Submit Answer lim n Need Help? 30/ n2 Read It Watch It Save Progress Read It -/1 points LarCalc10...
-
How might the principles of servant leadership be applied in organizational contexts to empower leaders to serve the needs of their teams, inspire trust, and foster a culture of empowerment and...
-
Business development for specifically Corporates. Almost like re-opening hotels post pandemic. Here, I would also use the technology element where the database is obsolete and requires clean up as so...
-
What is the total area and cost of the clear and colored glass? Use 3.14 for T. The sample stained-glass window illustration Press a hotspot, then type your response, and press submit. Repeat for...
-
Business Correspondence Letter #3 - Persuasive Letter For this assignment, you will write a persuasive letter with the scenario provided below. Here are some steps that will help get you started: 1....
-
Analyze the fiduciary impacts and resource allocation decisions related to your policy change or new policy in the civil service reform. Analyzes 3 public administration techniques for resolving...
-
3. What will be printed after executing the following Java code? int i, sum = 0; for (i = 0; i <10; i+=2) { sum sum + i; System.out.println("i="+i); } A. i=0 B. i=10 C. i=12 D. 1-20
-
Write a paper by answer the following question: Should Recycling Be Mandatory?
-
Emphasize that the International Information Systems Security Certification Consortium (ISC)2 is considered the foremost organization offering information security certifications today.
-
I. Discuss the concept of deperimeterization and how it applies to information security. II. Emphasize the importance of remote access to systems and how COVID-19 accelerated the need for protected...
-
Discuss the BrewerNash Model, which is designed to prevent a conflict of interest between two parties. Point out that this model is sometimes known as a Chinese Wall.
-
The thermodynamic properties which depend on the mass of the system are called ................ properties.
-
The thermodynamic properties which do not depend on the mass of the system are called ................ properties.
-
Temperature is an ................ property.

Study smarter with the SolutionInn App


