Question: After a system compromise, a security engineer attempts to connect to an adversary's system as a hack - back action. What incident type does the
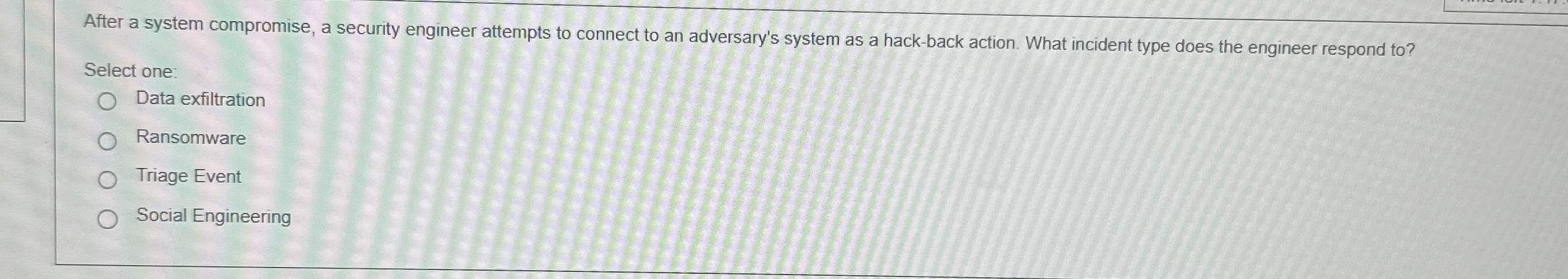
After a system compromise, a security engineer attempts to connect to an adversary's system as a hackback action. What incident type does the engineer respond to
Select one:
Data exfiltration
Ransomware
Triage Event
Social Engineering
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


