Alice, Bob and Carol use the the elliptic curves encryption scheme to communicate, and use the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
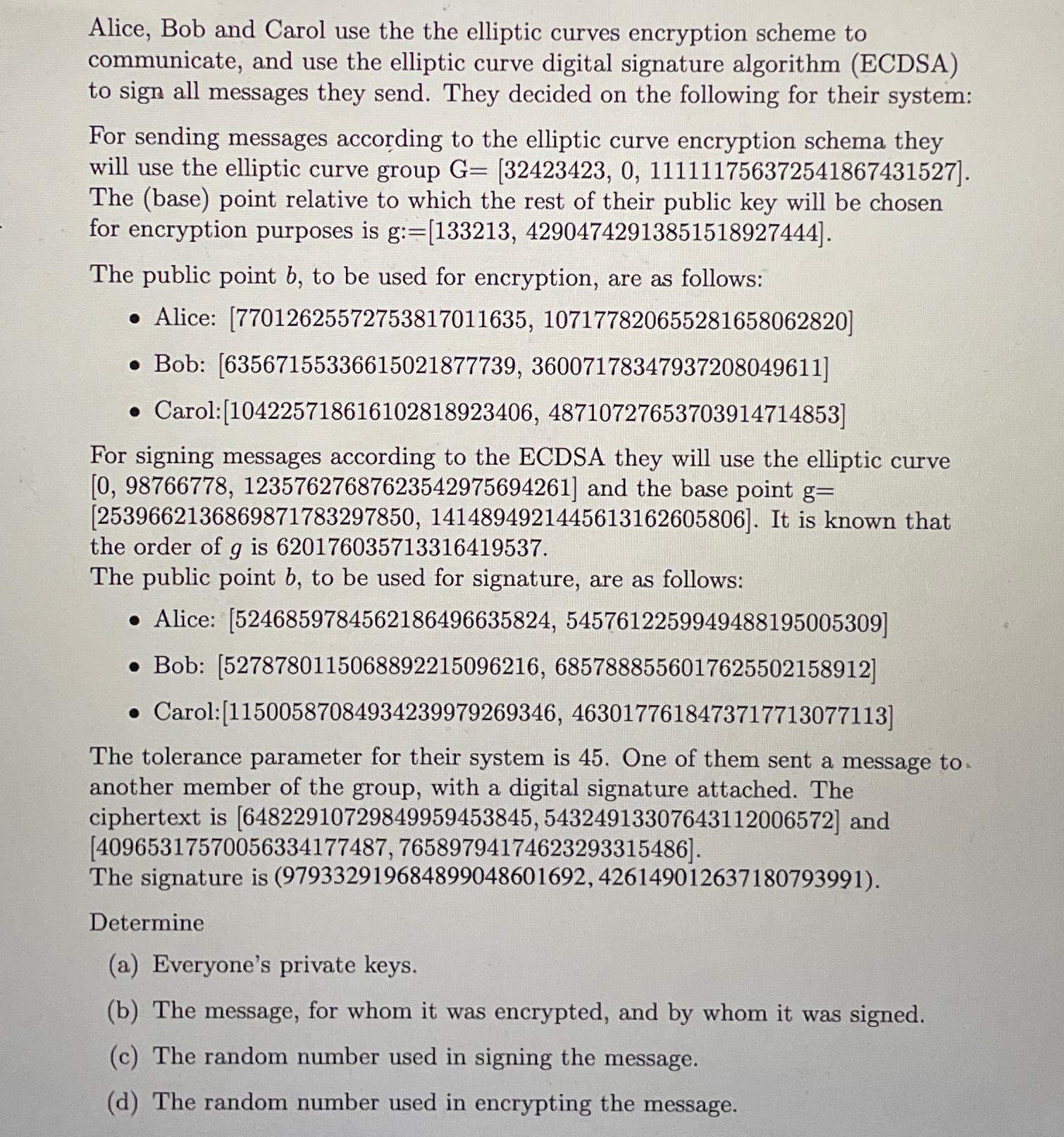
Alice, Bob and Carol use the the elliptic curves encryption scheme to communicate, and use the elliptic curve digital signature algorithm (ECDSA) to sign all messages they send. They decided on the following for their system: For sending messages according to the elliptic curve encryption schema they will use the elliptic curve group G= [32423423, 0, 111111756372541867431527]. The (base) point relative to which the rest of their public key will be chosen for encryption purposes is g:=[133213, 42904742913851518927444]. The public point b, to be used for encryption, are as follows: Alice: [77012625572753817011635, 107177820655281658062820] Bob: [63567155336615021877739, 36007178347937208049611] Carol:[104225718616102818923406, 48710727653703914714853] For signing messages according to the ECDSA they will use the elliptic curve [0, 98766778, 12357627687623542975694261] and the base point g= [2539662136869871783297850, 1414894921445613162605806]. It is known that the order of g is 620176035713316419537. The public point b, to be used for signature, are as follows: Alice: [5246859784562186496635824, 5457612259949488195005309] Bob: [5278780115068892215096216, 6857888556017625502158912] Carol:[11500587084934239979269346, 4630177618473717713077113] The tolerance parameter for their system is 45. One of them sent a message to another member of the group, with a digital signature attached. The ciphertext is [64822910729849959453845, 54324913307643112006572] and [40965317570056334177487, 76589794174623293315486]. The signature is (979332919684899048601692, 426149012637180793991). Determine (a) Everyone's private keys. (b) The message, for whom it was encrypted, and by whom it was signed. (c) The random number used in signing the message. (d) The random number used in encrypting the message. Alice, Bob and Carol use the the elliptic curves encryption scheme to communicate, and use the elliptic curve digital signature algorithm (ECDSA) to sign all messages they send. They decided on the following for their system: For sending messages according to the elliptic curve encryption schema they will use the elliptic curve group G= [32423423, 0, 111111756372541867431527]. The (base) point relative to which the rest of their public key will be chosen for encryption purposes is g:=[133213, 42904742913851518927444]. The public point b, to be used for encryption, are as follows: Alice: [77012625572753817011635, 107177820655281658062820] Bob: [63567155336615021877739, 36007178347937208049611] Carol:[104225718616102818923406, 48710727653703914714853] For signing messages according to the ECDSA they will use the elliptic curve [0, 98766778, 12357627687623542975694261] and the base point g= [2539662136869871783297850, 1414894921445613162605806]. It is known that the order of g is 620176035713316419537. The public point b, to be used for signature, are as follows: Alice: [5246859784562186496635824, 5457612259949488195005309] Bob: [5278780115068892215096216, 6857888556017625502158912] Carol:[11500587084934239979269346, 4630177618473717713077113] The tolerance parameter for their system is 45. One of them sent a message to another member of the group, with a digital signature attached. The ciphertext is [64822910729849959453845, 54324913307643112006572] and [40965317570056334177487, 76589794174623293315486]. The signature is (979332919684899048601692, 426149012637180793991). Determine (a) Everyone's private keys. (b) The message, for whom it was encrypted, and by whom it was signed. (c) The random number used in signing the message. (d) The random number used in encrypting the message.
Expert Answer:
Answer rating: 100% (QA)
a Private Keys We can use the fact that the private key d corresponding to a public key b is the int... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
Which of these is NOT one of the validity conditions for a t-test for the slope of a regression line? A. We should have a large sample size, typically n 20. B. The scatterplot of the sample data...
-
Fred, a cash basis taxpayer, received a $15,000 bonus from his employer in 2013. The bonus was based on the company's profits for 2012. In 2014, the company discovered that its 2012 profits were...
-
You drew the two chair conformations of lindane. Carefully inspect them, and predict the difference in energy between them, if any.
-
On January 2, 2018, The Register, a science and technology news site based in Britain, published an article revealing the existence of two major bugs leaving virtually all computers and smartphones...
-
Modular houses are Homes, Inc.s specialty. The companys best-selling model is a three-bedroom, 1,400-square-foot house with an impressive front entrance. Last year, the standard costs for the six...
-
Criticism of the World Bank is generally on a diverse range of issues but they generally centre around concern about the approaches adopted by the World Bank in formulating their policies, and the...
-
Place the different information: Packets , frames , segments , data and bits: 1- 2- 3- 4- 5- Electronic Email Data Network Header Message Frame Network Header Header Data Data Data Data Data End of...
-
Consider four finalists in a treasure hunt who are brought to the center of a large, flat field. Each is given a meterstick, a compass, a calculator, a shovel, and (in a different order for each...
-
Investment analysts expect Warren plc's profits for the next year to be around 50 million, the highest level ever achieved by the company. However, it is believed that in future the company will not...
-
Use the "up-down" binomial pricing method to derive call option values for the following conditions: A. S = 50, K = 54, r = 3%, t = .25, u = 1.5, d = .5 and there is only one step or "jump" before...
-
Explain the difference between the economically optimal harvest, the maximum sustained yield, the open-access equilibrium for a fishery. Illustrate the answer with a graph showing a marginal cost...
-
Bryce Carson, CFO of Elk Corporation, has written a memo to Richard Washington, Controller, addressing items brought up in the review of the June 20X5 financial statements. Elk Corporation is on a...
-
Question 15 S = X1+ X2 + X3 + X4 Each of the X random variables (independent and identical ) are Geometric with p= 1/2. What is mean of S What is the standard deviation of S (rounded 2 decimal...
-
For all of the following words, if you move the first letter to the end of the word, and then spell the result backwards, you will get the original word: banana dresser grammar potato revive uneven...
-
Suppose we have a set of blocks encoded with the RSA algorithm and we don't have the private key. Assume \(n=p q, e\) is the public key. Suppose also someone tells us they know one of the plaintext...
-
Find the multiplicative inverse of each nonzero element in \(Z_{5}\).
-
Describe a classification of computer crime based on the role that the computer plays in the criminal activity.
-
Suppose you want to create a price index for the price of a personal pizza across several Canadian university campuses, as of March 1 , 201 6. The data are as follows: a. Using Calgary as the "base...
-
Fill in the blanks to make the following statements correct. a. Ceteris paribus, the price of a product and the quantity demanded are related ________ b. Ceteris paribus, the price of a product and...
-
The following questions will provide practice working with simple linear functions. All questions refer to a coordinate graph with the variable \(X\) on the horizontal axis and the variable \(Y\) on...

Study smarter with the SolutionInn App


