Question: Alice uses an RSA algorithm with the private key Ks and the public key KP given by ( 5 , 2 4 7 ) and
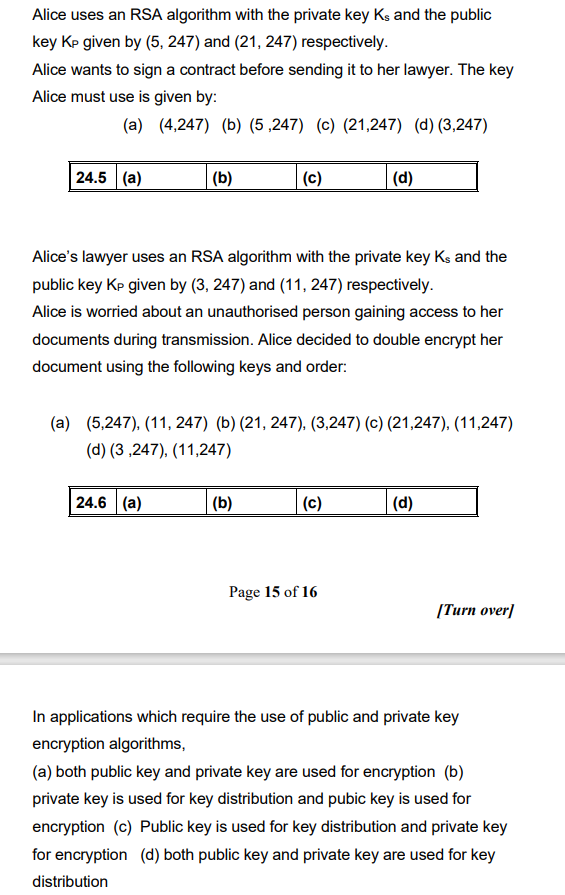
Alice uses an RSA algorithm with the private key Ks and the public
key KP given by and respectively.
Alice wants to sign a contract before sending it to her lawyer. The key
Alice must use is given by:
abcd
Alices lawyer uses an RSA algorithm with the private key Ks and the
public key KP given by and respectively.
Alice is worried about an unauthorised person gaining access to her
documents during transmission. Alice decided to double encrypt her
document using the following keys and order:
abc
d
In applications which require the use of public and private key
encryption algorithms,
a both public key and private key are used for encryption b
private key is used for key distribution and pubic key is used for
encryption c Public key is used for key distribution and private key
for encryption d both public key and private key are used for key
distribution
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


