Alice(A) and Bob(B) use ElGamal encryption system with public key parameters: q = 23, g =...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
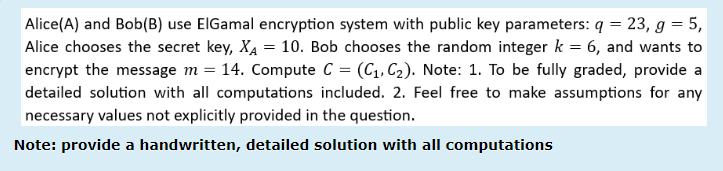
Alice(A) and Bob(B) use ElGamal encryption system with public key parameters: q = 23, g = 5, Alice chooses the secret key, XA = 10. Bob chooses the random integer k = 6, and wants to encrypt the message m = 14. Compute C = (C₁, C₂). Note: 1. To be fully graded, provide a detailed solution with all computations included. 2. Feel free to make assumptions for any necessary values not explicitly provided in the question. Note: provide a handwritten, detailed solution with all computations Alice(A) and Bob(B) use ElGamal encryption system with public key parameters: q = 23, g = 5, Alice chooses the secret key, XA = 10. Bob chooses the random integer k = 6, and wants to encrypt the message m = 14. Compute C = (C₁, C₂). Note: 1. To be fully graded, provide a detailed solution with all computations included. 2. Feel free to make assumptions for any necessary values not explicitly provided in the question. Note: provide a handwritten, detailed solution with all computations
Expert Answer:
Answer rating: 100% (QA)
Step 1 Find the value of g Since q23 we need to find a primitive root modulo 23 We can do this by te... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
Why dont physicians guarantee their work as do many auto repair shops?
-
How do state and federal laws regulate door-to-door sales?
-
Exercise 12.6 implements the hex2Dec method to throw a NumberFormatException if the string is not a hex string. Define a custom exception called HexFormatException. Implement the hex2Dec method to...
-
Petitioner Christy Brzonkala met respondents Antonio Morrison and James Crawford at a campus party at Virginia Polytechnic Institute (Virginia Tech), where they were all students. At the party, the...
-
A local television station plans to drop four Friday evening programs at the end of the season. Steve Botuchis, the station manager, developed a list of six potential replacement programs. Estimates...
-
Question 2 (50 points) When does the complex exponential prefactor for the solutions to the time- independent Schrodinger's equation matter? Let's find out with this example. An electron is confined...
-
Classify each function as a power function, root function, polynomial (state its degree), rational function, algebraic function, trigonometric function, exponential function, or logarithmic function....
-
For a given pump design, use the step wise method of repeating variables to generate a dimensionless relationship for the output variables gH as a function of discharge Q, impeller diameter D, shaft...
-
How do checks and balances work in the U.S. Government? Why is this important? Please use examples to support your answer. Examples can be from the text or from current articles/research in the news.
-
What would be the impact on the supreme court should justice brown be removed from the court ?
-
When does trademark infringement occur? . What trademarks are protected by law? How does the license protect intellectual property? What works are protected by copyright? What federal legislation...
-
Analyze a minimum of three (3) objectives of the negotiation process within the aviation industry. Analysis should also outline three (3) strategies to resolve the causes of disputes during the...
-
What are the key points in Ethics Opinion CAL 2012-184: Virtual Law Office. Please explain the Facts, Issue, Rules of Law, Application and Analysis and the Conclusion.
-
Which factors need to be considered when the hotel reaches full accommodation capacity based on the future forecast for 2016/17? Given the modernisation of the operation, the director in conjunction...
-
Juanita owns a home in Richardson, TX. She purchases a Homeowners Policy (HO-3) from Farm State Ins. Co. The policy provides $100,000 in liability coverage (coverage E) and $5,000 in Med Pay coverage...
-
Consider the previous problem, but instead of containing the binary of the numbers 0 through 9 suppose these 10 bytes contain a, the binary representation of the numbers I through 10, b, the ASCII...
-
Suppose you are interested in detecting the number of hosts behind a NAT. You observe that the IP layer stamps an identification number sequentially on each IP packet. The identification number of...
-
Write a simple TCP program for a server that accepts lines of input from a client and prints the lines onto the server's standard output. (You can do this by modifying the TCPServer java program in...
-
From the following trial balance of G. Foot after his first year's trading, you are required to draw up a statement of profit or loss for the year ending 30 June 2016. A statement of financial...
-
At the beginning of the financial year on 1 April 2017, a company had a balance on plant account of 372,000 and on provision for depreciation of plant account of 205,400. The company's policy is to...
-
What circumstances might lead you to write-off a debt as bad and not close the debtor's account?

Study smarter with the SolutionInn App


