Question: Almost all data transferred over the Internet use the Internet Protocol at the Network layer. Choose any webpage that is freely available via the
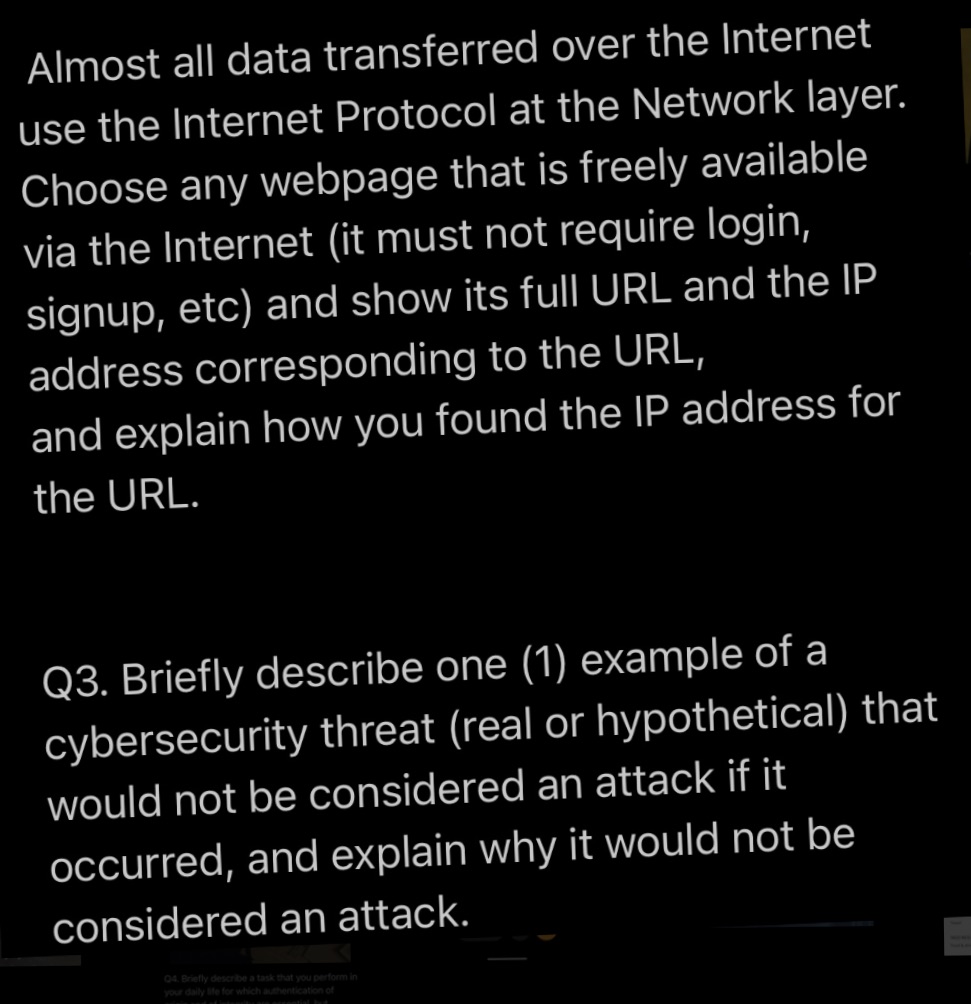
Almost all data transferred over the Internet use the Internet Protocol at the Network layer. Choose any webpage that is freely available via the Internet (it must not require login, signup, etc) and show its full URL and the IP address corresponding to the URL, and explain how you found the IP address for the URL. Q3. Briefly describe one (1) example of a cybersecurity threat (real or hypothetical) that would not be considered an attack if it occurred, and explain why it would not be considered an attack. 04. Briefly describe a task that you perform in your daily life for which authentication of
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


