Question: An adversary can perform an attack to a hash algorithm by applying random inputs and repeating until finding two inputs x and y (zy) that
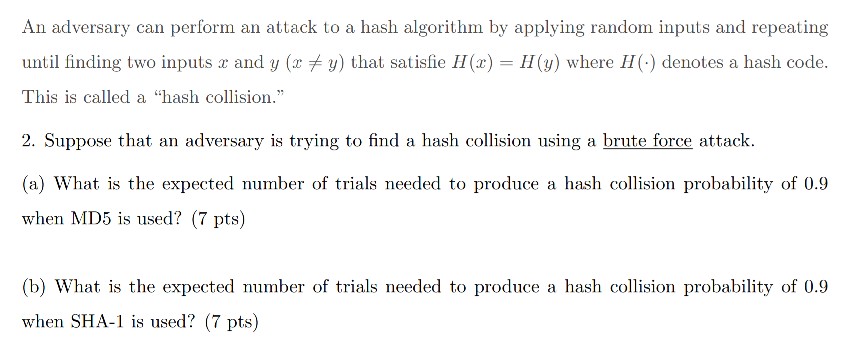
An adversary can perform an attack to a hash algorithm by applying random inputs and repeating until finding two inputs x and y (zy) that satisfie 11(x) = H(y) where 11(.) denotes a hash code. This is called a "hash collision. 2. Suppose that an adversary is trying to find a hash collision using a brute force attaclk (a) What is the expected number of trials needed to produce a hash collision probability of 0.9 when MD5 is used? (7 pts) (b) What is the expected number of trials needed to produce a hash collision probability of 0.9 when SHA- s used? 7 pts)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


