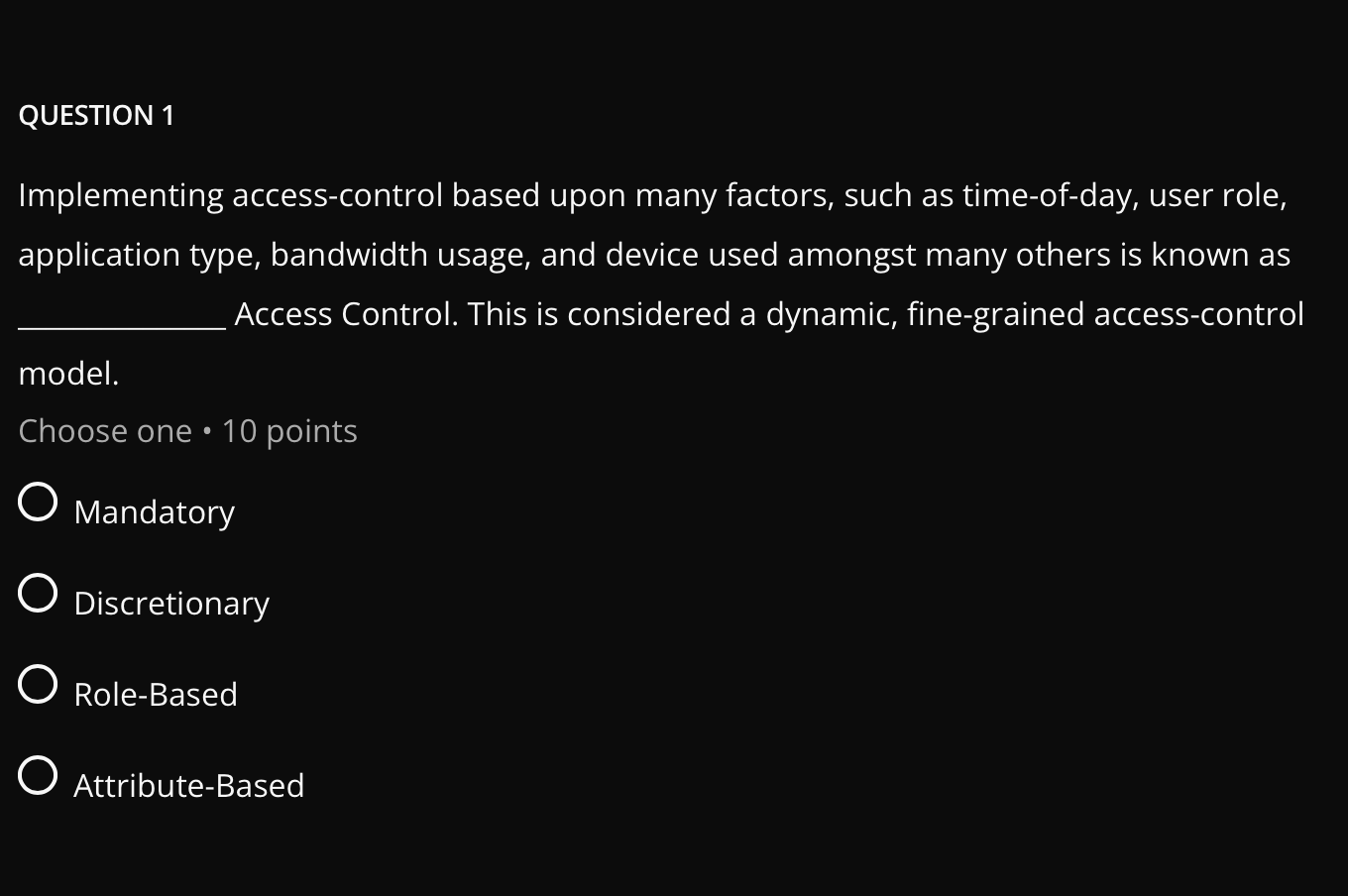
Question: answer QUESTION 1 Implementing access-control based upon many factors, such as time-of-day, user role, application type, bandwidth usage, and device used amongst many others is
answer
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


