Question: Apply the framework for vulnerability assessment and vulnerability management by assuming an example. Monitoring Ongoing Assessments Continuous Improvement IT Asset Inventory Threat Identification Vulnerability Identification
Apply the framework for vulnerability assessment and vulnerability management by assuming an example. 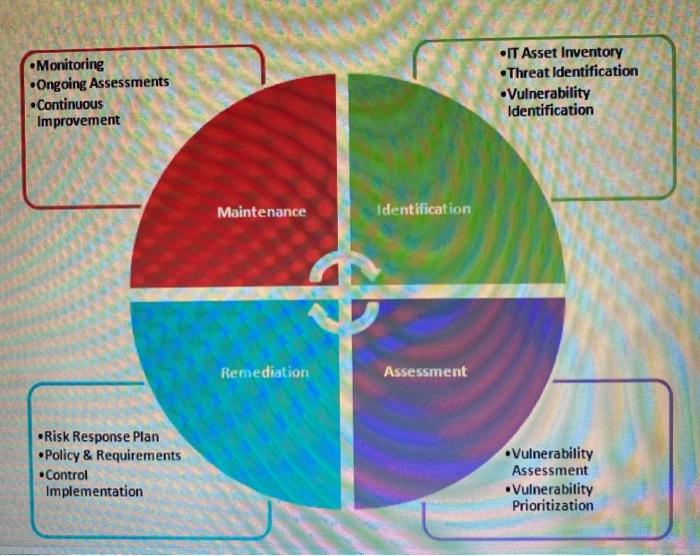
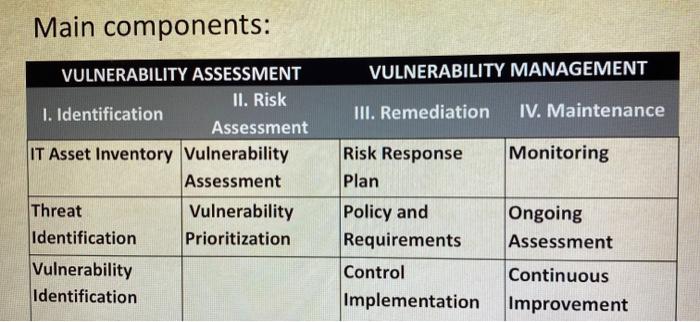
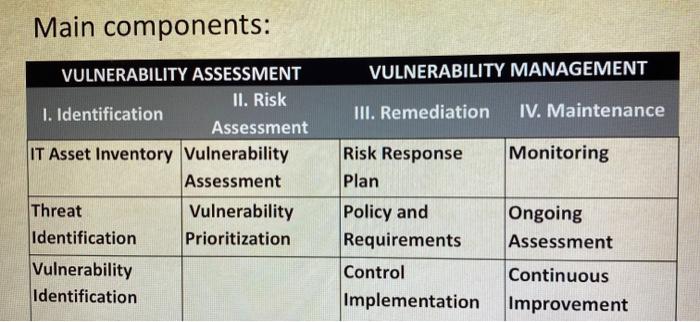
Monitoring Ongoing Assessments Continuous Improvement IT Asset Inventory Threat Identification Vulnerability Identification Maintenance Identification Remediation Assessment Risk Response Plan Policy & Requirements Control Implementation Vulnerability Assessment Vulnerability Prioritization Main components: VULNERABILITY MANAGEMENT III. Remediation IV. Maintenance Monitoring VULNERABILITY ASSESSMENT II. Risk 1. Identification Assessment IT Asset Inventory Vulnerability Assessment Threat Vulnerability Identification Prioritization Vulnerability Identification Risk Response Plan Policy and Requirements Control Implementation Ongoing Assessment Continuous Improvement 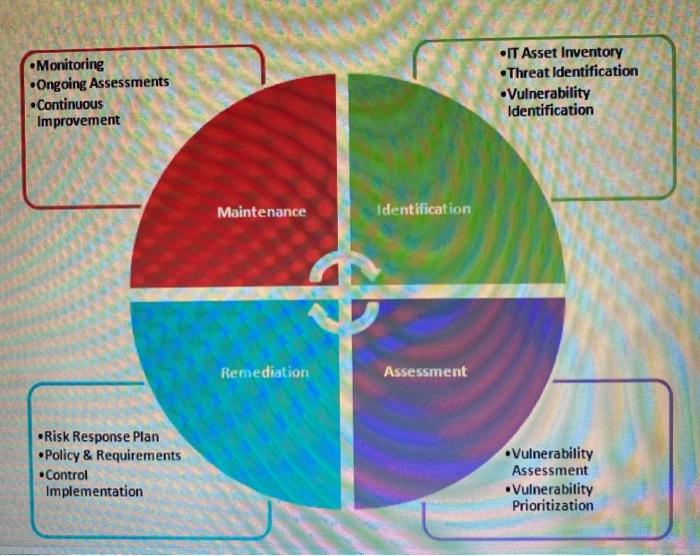
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


