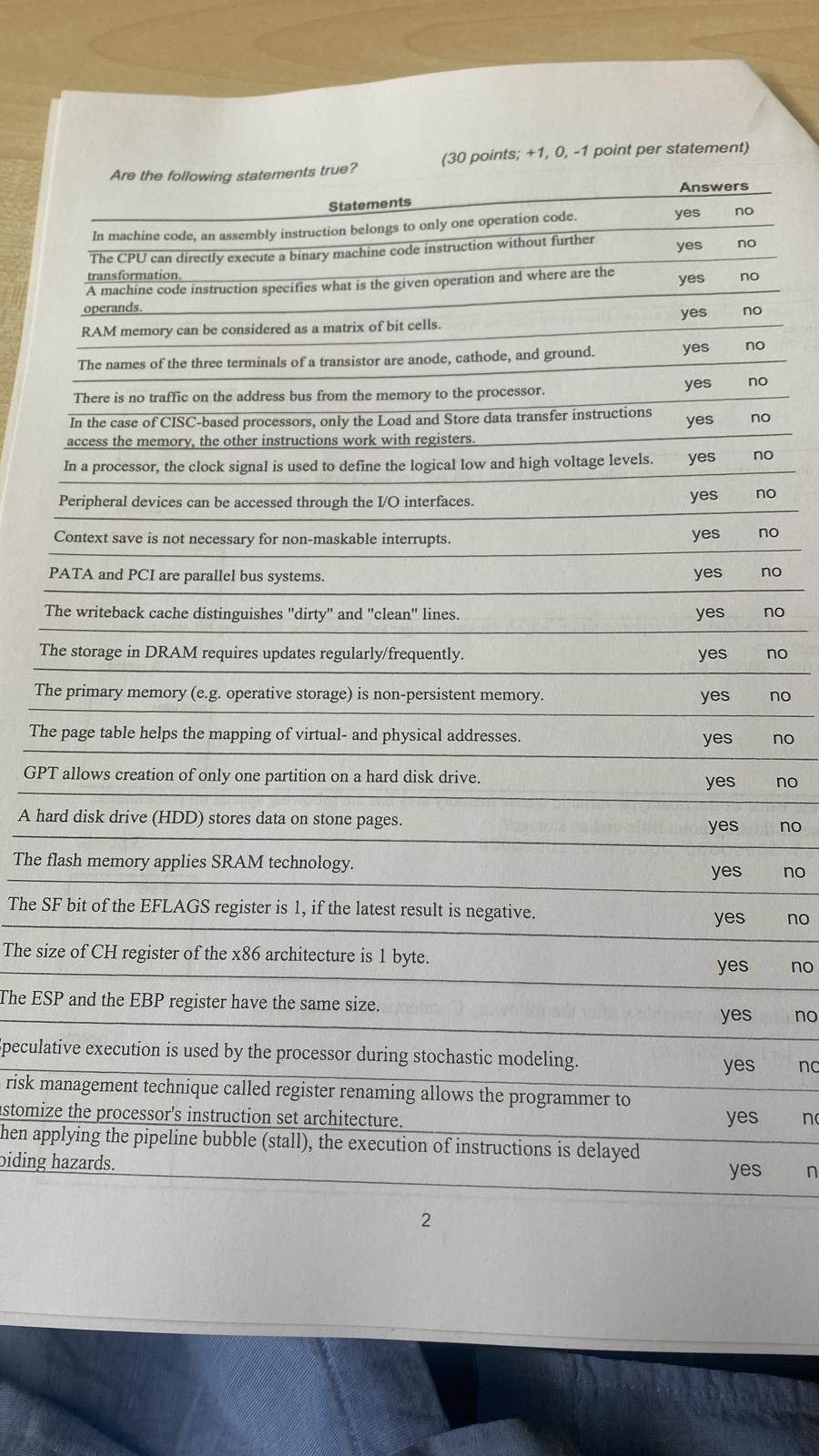
Question: Are the following statements true? ( 3 0 points; + 1 , 0 , - 1 point per statement ) Statements In mansers transformation. A
Are the following statements true?
points; point per statement
Statements
In mansers transformation.
A machine code instruction specifies what is the given operation and where are the operands.
RAM memory can be considered as a matrix of bit cells.
The names of the three terminals of a transistor are anode, cathode, and ground.
There is no traffic on the address bus from the memory to the processor.
In the case of CISCbased processors, only the Load and Store data transfer instructions access the memory, the other instructions work with registers.
In a processor, the clock signal is used to define the logical low and high voltage levels.
Peripheral devices can be accessed through the IO interfaces.
Context save is not necessary for nonmaskable interrupts.
PATA and PCI are parallel bus systems.
The writeback cache distinguishes "dirty" and "clean" lines.
peculative execution is used by the processor during stochastic modeling.
risk management technique called register renaming allows the programmer to
stomize the processor's instruction set architecture.
hen applying the pipeline bubble stall the execution of instructions is delayed oiding hazards.
The pipeline operation is impossible in GPU.
The instruction execution speed of a processor is inver yes no of its clock signal.
frequency
tablencyyes,noyes,noyes,nonmunicate with each other.,yes,no
What do you know about pipeline hazards? Meaning types, treatment methods, etc. Write some sentences about them.
points
Are the following statements true?
points; point per statement
Statements
In mansers transformation.
A machine code instruction specifies what is the given operation and where are the operands.
RAM memory can be considered as a matrix of bit cells.
The names of the three terminals of a transistor are anode, cathode, and ground.
There is no traffic on the address bus from the memory to the processor.
In the case of CISCbased processors, only the Load and Store data transfer instructions access the memory, the other instructions work with registers.
In a processor, the clock signal is used to define the logical low and high voltage levels.
Peripheral devices can be accessed through the IO interfaces.
Context save is not necessary for nonmaskable interrupts.
PATA and PCI are parallel bus systems.
The writeback cache distinguishes "dirty" and "clean" lines.
peculative execution is used by the processor during stochastic modeling.
risk management technique called register renaming allows the programmer to
stomize the processor's instruction set architecture.
hen applying the pipeline bubble stall the execution of instructions is delayed oiding hazards.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


