Asia Pacific University is a technological based university located at Technology Park Malaysia (TPM), and is...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
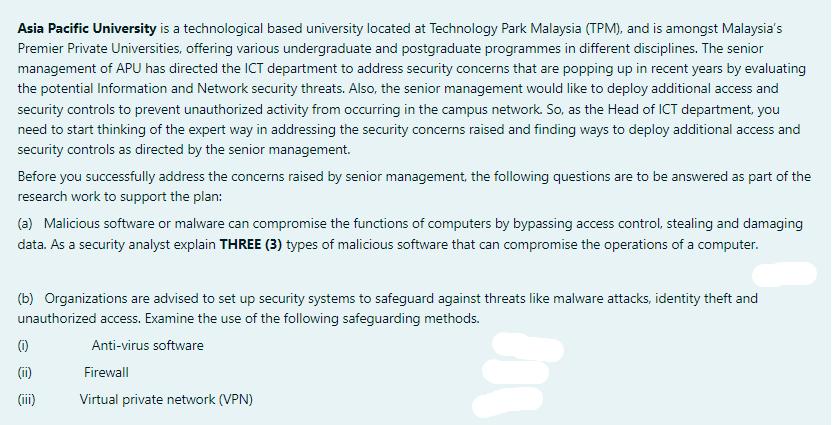
Asia Pacific University is a technological based university located at Technology Park Malaysia (TPM), and is amongst Malaysia's Premier Private Universities, offering various undergraduate and postgraduate programmes in different disciplines. The senior management of APU has directed the ICT department to address security concerns that are popping up in recent years by evaluating the potential Information and Network security threats. Also, the senior management would like to deploy additional access and security controls to prevent unauthorized activity from occurring in the campus network. So, as the Head of ICT department, you need to start thinking of the expert way in addressing the security concerns raised and finding ways to deploy additional access and security controls as directed by the senior management. Before you successfully address the concerns raised by senior management, the following questions are to be answered as part of the research work to support the plan: (a) Malicious software or malware can compromise the functions of computers by bypassing access control, stealing and damaging data. As a security analyst explain THREE (3) types of malicious software that can compromise the operations of a computer. (b) Organizations are advised to set up security systems to safeguard against threats like malware attacks, identity theft and unauthorized access. Examine the use of the following safeguarding methods. Anti-virus software Firewall Virtual private network (VPN) (1) (11) (iii) 08 Asia Pacific University is a technological based university located at Technology Park Malaysia (TPM), and is amongst Malaysia's Premier Private Universities, offering various undergraduate and postgraduate programmes in different disciplines. The senior management of APU has directed the ICT department to address security concerns that are popping up in recent years by evaluating the potential Information and Network security threats. Also, the senior management would like to deploy additional access and security controls to prevent unauthorized activity from occurring in the campus network. So, as the Head of ICT department, you need to start thinking of the expert way in addressing the security concerns raised and finding ways to deploy additional access and security controls as directed by the senior management. Before you successfully address the concerns raised by senior management, the following questions are to be answered as part of the research work to support the plan: (a) Malicious software or malware can compromise the functions of computers by bypassing access control, stealing and damaging data. As a security analyst explain THREE (3) types of malicious software that can compromise the operations of a computer. (b) Organizations are advised to set up security systems to safeguard against threats like malware attacks, identity theft and unauthorized access. Examine the use of the following safeguarding methods. Anti-virus software Firewall Virtual private network (VPN) (1) (11) (iii) 08
Expert Answer:
Answer rating: 100% (QA)
a Three types of malicious software malware that can compromise the operations of a computer 1 Viruses This type of malware is known for attaching its... View the full answer

Related Book For 

Essentials Of Modern Business Statistics With Microsoft Excel
ISBN: 9780357131626
8th Edition
Authors: David R. Anderson, Dennis J. Sweeney, Thomas A. Williams, Jeffrey D. Camm, James J. Cochran
Posted Date:
Students also viewed these computer network questions
-
Write a java program to perform square of a given number?
-
San Lorenzo General Store uses a periodic inventory system and the retail inventory method to estimate ending inventory and cost of goods sold. The following data are available for the month of...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
If a= 3 m, determine the magnitudes of P and Q required to maintain the cable in the shape shown. DI 120 kN
-
(a) What are the two important documents required by the Securities Act of 1933? (b) Under the provisions of the federal Securities Act of 1933, there are three important time periods concerning when...
-
Q4 How do global information systems affect supply chain profitability?
-
Compute Topp Companys price-earnings ratio if its common stock has a market value of $32.60 per share and its EPS is $3.95. Would an analyst likely consider this stock potentially over- or...
-
Company A has three debt issues of $3,000 each. The interest rate on issue A is 4 percent, on B the rate is 6 percent, and on C the rate is 8 percent. Issue B is subordinate to A, and issue C is...
-
[The following information applies to the questions displayed below.] Data for Hermann Corporation are shown below: Percent of Sales 100% 61% Per Unit $ 100 61 Selling price Variable expenses ol...
-
The management of Zigby Manufacturing prepared the following balance sheet for March 31. Cash Accounts receivable Raw materials inventory Assets ZIGBY MANUFACTURING Balance Sheet March 31 Liabilities...
-
1 - Preliminary Questions For an electromagnetic wave traveling along the x-axis direction E (x,t) = E cos (kx- wt+ q) and B(x, t) = Bcos(kx- wt+ () Where E, and Bo indicate the maximum values of the...
-
Describe in your own words how you would expect the data points on a scatterplot to be distributed if the following features were present (i.e. for each part, explain how the feature would look on a...
-
imagine this experimental setup: One temperature probe is in embedded in a small block of frozen sugar water at -20. The frozen sugar water is in a small test tube The melting/freezing point of this...
-
Question 2: (40 points: 10 each) During September, Sweet Foods manufactures a single product. The Company's material purchases amounted to 9,000 pounds at a price of $9.80 per pound. Actual costs...
-
E12-23 (Algo) (Supplement 12B) Preparing a Statement of Cash Flows, Indirect Method: T-Account Approach [LO 12-S2] Golf Goods Incorporated is a regional and online golf equipment retailer. The...
-
A symmetric compound channel in over bank flow has a main channel with a bottom width of 30 m, side slopes of 1:1, and a flow depth of 3m. The floodplains on either side of the main channel are both...
-
1. The chart of accounts and post-closing trial balance (April 2017) for Mike Shaw Contractors is shown below. For each account in the post-closing trial balance, enter the balance in the appropriate...
-
(a) Given a mean free path = 0.4 nm and a mean speed vav = 1.17 105 m/s for the current flow in copper at a temperature of 300 K, calculate the classical value for the resistivity of copper. (b)...
-
A sample of 16 items from population 1 has a sample variance s 2 1 = 5.8 and a sample of 21 items from population 2 has a sample variance s 2 2 = 2.4. Test the following hypotheses at the .05 level...
-
Consider a binomial experiment with two trials and p = .4. a. Draw a tree diagram for this experiment. b. Compute the probability of one success, f (1). c. Compute f (0). d. Compute f (2). e. Compute...
-
Given are data for two variables, x and y. a. Develop an estimated regression equation for these data. b. Compute the residuals. c. Develop a plot of the residuals against the independent variable x....
-
2. Modifying organizational structure to fit the communication needs of the organization
-
1. Clarifying and defining jobs
-
8. Can paperwork regarding this job be eliminated?

Study smarter with the SolutionInn App