Question: Assignment 2 Due Date: Wednesday, January 5, 2022 1. (30 points) Comsider password authentication (a) Suppose an off-line dictionary attack is used, and suppose the
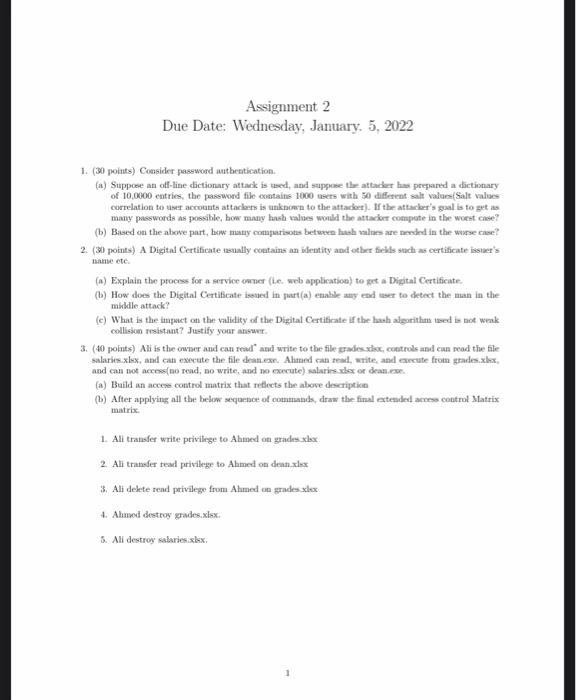
Assignment 2 Due Date: Wednesday, January 5, 2022 1. (30 points) Comsider password authentication (a) Suppose an off-line dictionary attack is used, and suppose the attacker has prepared a dictionary of 10,0000 entries, the password file contains 1000sers with 50 different salt values: Salt values correlation to user accounts attackers is unknown to the attacher). If the attacker's goal is to get as many passwords as possible, bow many hash values would the attacior compute in the woest case? (b) Based on the above part, bww many comparison betwee has als are ended in the wise ce? 2. (30 points) A Digital Certificate tsually contains an identity and other tekis sadh as certificate isster's name etc (a) Explain the process for a service ower (he web application) to get a Digital Certificate. (b) How does the Digital Certificate issued in part(a) enable any end wer to detect the man in the middle attack? (e) What is the impact on the validity of the Digital Certificate if the bash algorithm sed is not weak collision resistant? Justify your answer 3. (40 points) Ali is the owner and can read and write to the file grades de controls and can read the file salaries.xlsx, and can execute the file danes. Ahmed can read, write, and execute from grades.xx and can not access to read, no write, and no execute) salaries ist or dean.exe (a) Build an access control matrix that reflects the above descriptice (1) After applying all the below sequence of commands, draw the final extended to control Matrix matrix 1. Ali transfer write privilege to Ahmed on grades.xbox 2. Ali tramad teadl privilege to Ahmed on dean.xlsx 3. Ali dekte rend privilege from Ahmed on grades xlx 4. Ahmed destroy grades.xlsx 3. Ali destroy salaries.xlsx 1
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


