Introduction Cyberattacks rank as the fastest growing crime in the US, causing catastrophic business disruption. As a
Question:
Introduction
Cyberattacks rank as the fastest growing crime in the US, causing catastrophic business disruption. As
a result, cybersecurity is high stakes with the threat to enterprises expected to increase in frequency
and force. How to secure organizations against cyberattacks?
Security Onion is an open-source suite of Network Security Monitoring (NSM) tools that run on an
Ubuntu Linux distribution. Security Onion can be installed as a standalone installation or as a sensor
and server platform. The threat landscape is constantly changing as new vulnerabilities are discovered,
and new threats evolve. As user and organizational needs change, so does the attack surface. Threat
actors have learned how to quickly vary the features of their exploits in order to evade detection. It is
impossible to design measures to prevent all exploits. Exploits will inevitably evade protection
measures, no matter how sophisticated they may be. Sometimes, the best that can be done is to
detect exploits during or after they have occurred. Detection rules should be overly conservative. In
other words, it is better to have alerts that are sometimes generated by innocent traffic than to have
rules that miss malicious traffic. For this reason, it is necessary to have skilled cybersecurity analysts
to investigate alerts to determine if an exploit has occurred.
Question:
By referring to the Security Onion architecture as shown in Figure 1 and the network environment
as in Figure 2, draw an NSM system (tools and network components) that can mitigate cyber-
attacks to the scenarios. Select only TWO (2) scenarios.
You also need to explain about your designed NSM system including the following:
a. detection system
b. prevention system
c. alert system
d. risk type
e. possible impacts
f. possible type of attacks, and
g. possible attack surfaces
Note: The system should be able to mitigate cybersecurity risk by identifying weaknesses and
building resilience, as well as the ability to reduce the impact of existing and possible threats.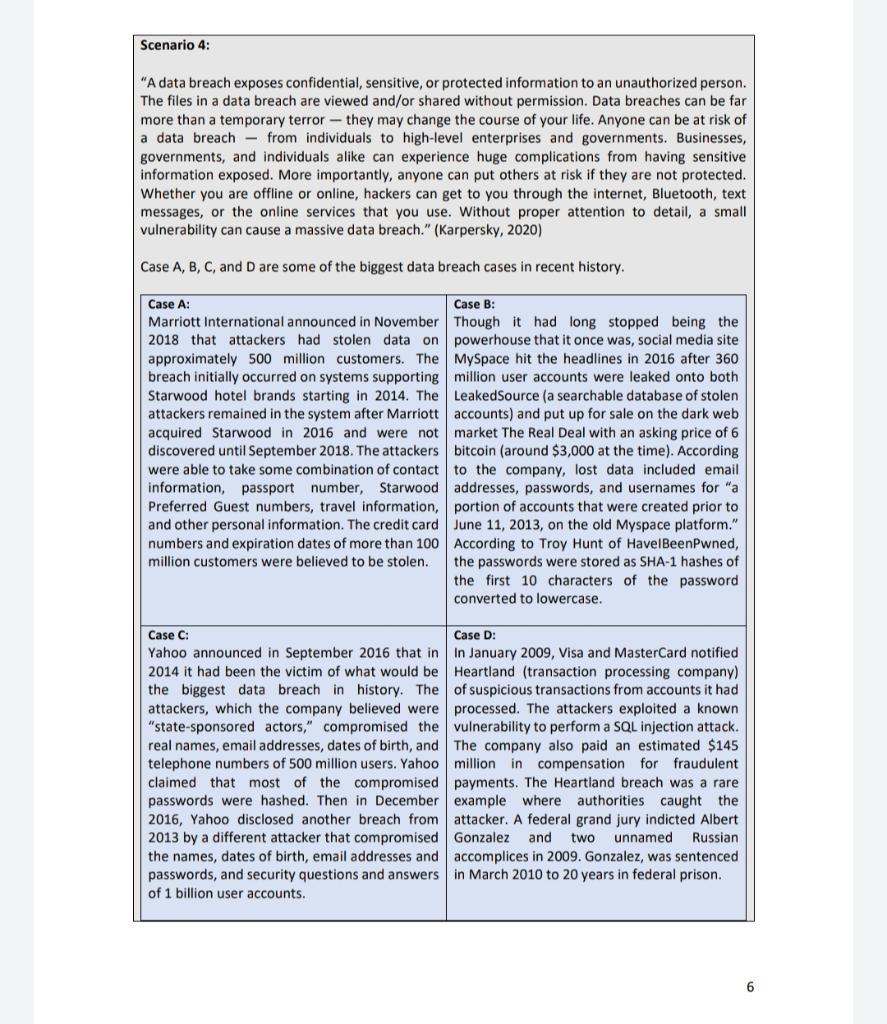

Mathematical Statistics with Applications in R
ISBN: 978-0124171138
2nd edition
Authors: Chris P. Tsokos, K.M. Ramachandran