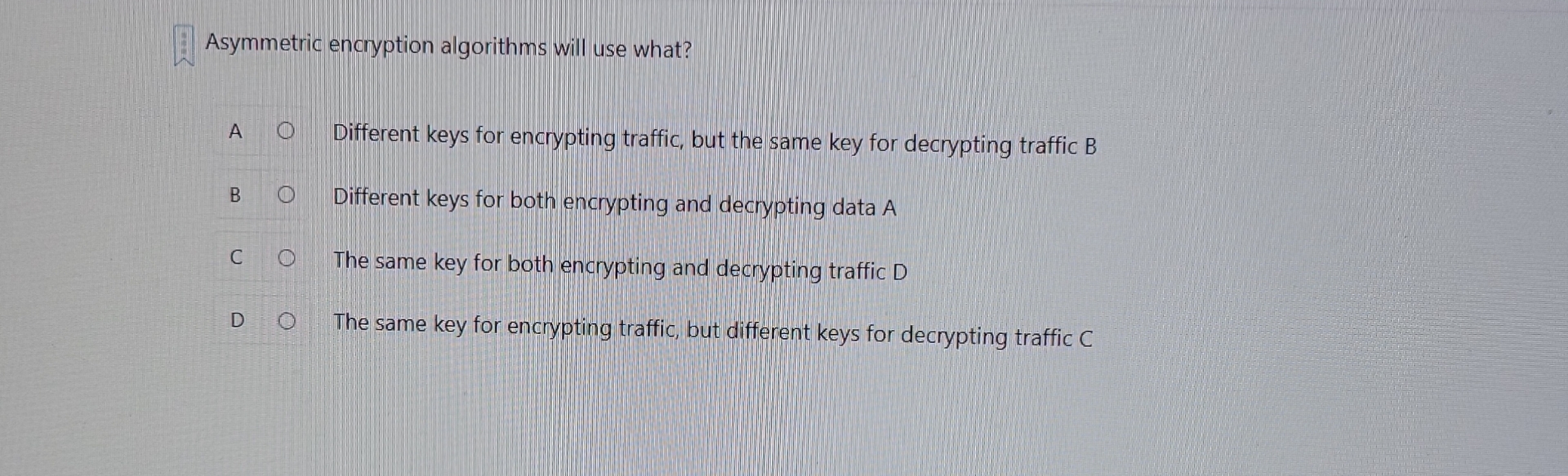
Question: Asymmetric encryption algorithms will use what? A Different keys for encrypting traffic, but the same key for decrypting traffic B B Different keys for both
Asymmetric encryption algorithms will use what?
A
Different keys for encrypting traffic, but the same key for decrypting traffic B
B
Different keys for both encrypting and decrypting data A
C
The same key for both encrypting and decrypting traffic
D
The same key for encrypting traffic, but different keys for decrypting traffic C
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


