Question: begin{tabular}{l|ll} Term & Definition & OSI Layer hline end{tabular} Whaling Credential Harvesting Typosquatting Principles of effective Social Engineering Impersonation Keylogger Rootkit Brute Force Attack
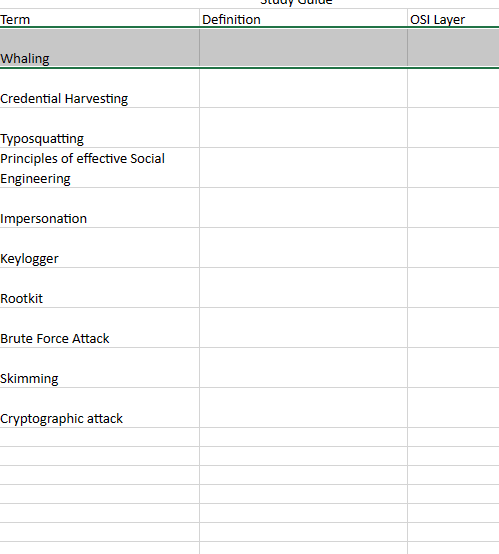
\begin{tabular}{l|ll} Term & Definition & OSI Layer \\ \hline \end{tabular} Whaling Credential Harvesting Typosquatting Principles of effective Social Engineering Impersonation Keylogger Rootkit Brute Force Attack Skimming Cryptographic attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


