Question: Ben replaces sensitive data in his database with unique identifiers. The identifiers allow him to continue to take actions on the data without exposing the
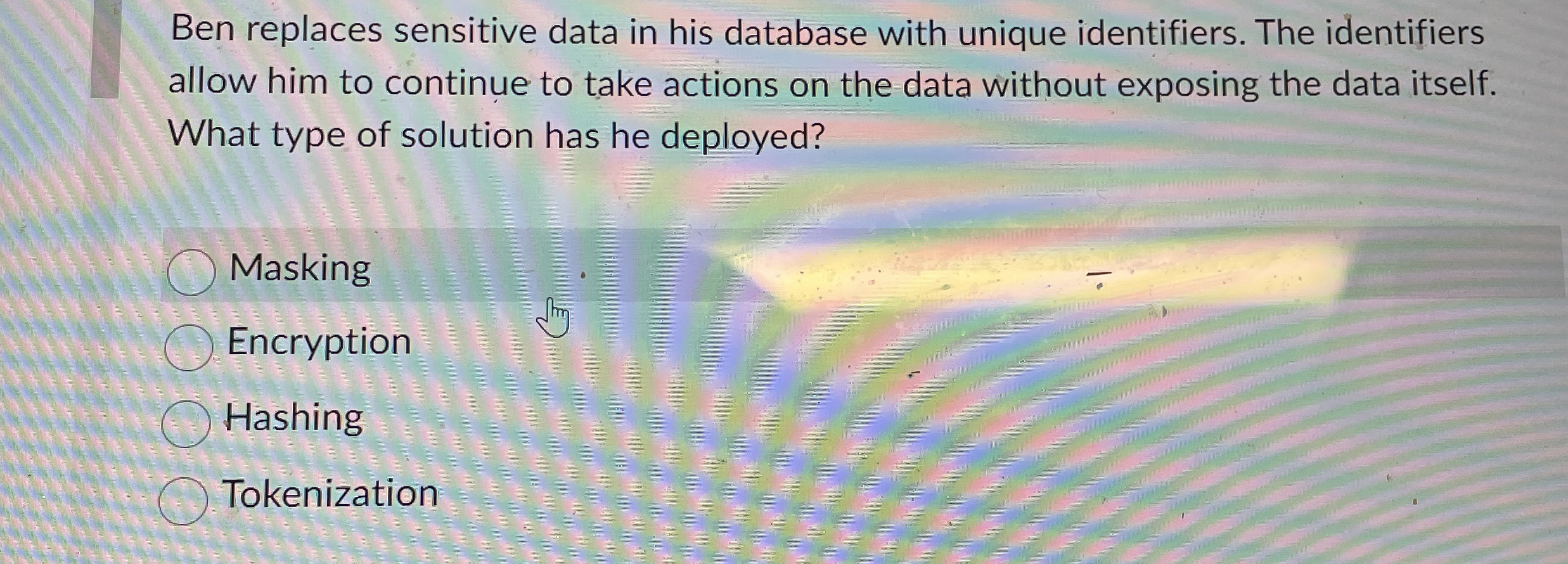
Ben replaces sensitive data in his database with unique identifiers. The identifiers allow him to continue to take actions on the data without exposing the data itself. What type of solution has he deployed?
Masking
Encryption
Hashing
Tokenization
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


