Question: Briefly provide an explanation for go back-oriented programming: what sort of software vulnerability and countermeasure does this class of attacks goal, how does it work,
Briefly provide an explanation for go back-oriented programming: what sort of software vulnerability and countermeasure does this class of attacks goal, how does it work, and under what conditions is it applicable? [6 marks] (b) Identify and connect a capacity vulnerability inside the following C characteristic: [2 marks] #include void *bitmalloc(size_t bits) return malloc((bits + 7)/eight);
(c) On a Linux file server, you locate this document: $ ls -l -rw----r-- 1 frank college students 13593 May 31 14:fifty five query.Tex User frank is a member of institution college students. (i) Based at the POSIX get admission to-manage settings proven, illustrate how the server's running system will authorize get admission to (if-assertion pseudo code). [3 marks] (ii) What does an equal Windows NTFS get admission to-manage list seem like? [3 marks] (iii) Does the Windows GUI for manipulating NTFS get entry to-control lists permit users to enter this configuration? [2 marks] (d) Give an instance of how POSIX record-system get entry to manage can be used to offer the equal of password safety for parts of the document area. In precise, show how user alice can set up a listing papers such that only the ones individuals of organization committee (which includes alice) who understand the name of the game string "SEL-4sB3" can examine a record confined.Pdf. Show the setup both as a sequence of shell instructions that alice can use to create it, or inside the form of the metadata of the files and directories worried (as ls -l could output it).
(a) (i) Describe the 4 training in Flynn's taxonomy of computing structures. [4 marks] (ii) Describe Amdahl's law and use it to calculate the most speedup conceivable by using walking a program, P, on a multicore system, S, wherein eighty% of P is parallel and S includes 16 cores. [4 marks] (b) Consider the subsequent pseudo-code this is run on a SIMD processor with eight lanes, in which i gives the lane variety. R1 = load X[i] r2 = load Y[i] if (i%2 == 0) if (i%8 == zero) r1 = r1 * 2 r1 = r1 + r2 endif else r1 = r1 - r2 endif save r1, X[i] (i) Describe how the processor can help branch divergence among the exclusive lanes. [4 marks] (ii) With the aid of a diagram, display the utilisation of the SIMD lanes for each pseudo-code operation, therefore calculate the code's performance (average utilisation of the SIMD lanes). [6 marks] (iii) What architectural technique do GPUs employ to allow them to carry out beneficial work despite the fact that the loads from X and Y often motive stalls? [
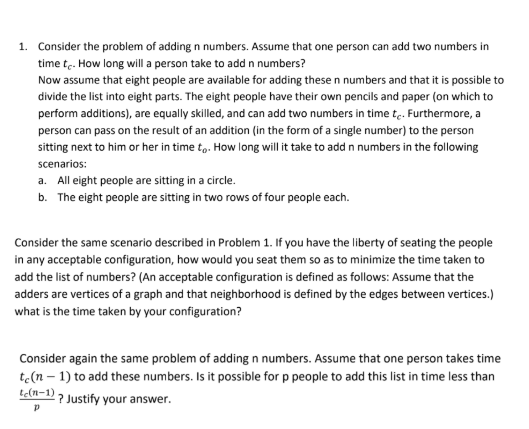
1. Consider the problem of adding n numbers. Assume that one person can add two numbers in time tc. How long will a person take to add n numbers? Now assume that eight people are available for adding these n numbers and that it is possible to divide the list into eight parts. The eight people have their own pencils and paper (on which to perform additions), are equally skilled, and can add two numbers in time tc. Furthermore, a person can pass on the result of an addition (in the form of a single number) to the person sitting next to him or her in time to. How long will it take to add n numbers in the following scenarios: a. All eight people are sitting in a circle. b. The eight people are sitting in two rows of four people each. Consider the same scenario described in Problem 1. If you have the liberty of seating the people in any acceptable configuration, how would you seat them so as to minimize the time taken to add the list of numbers? (An acceptable configuration is defined as follows: Assume that the adders are vertices of a graph and that neighborhood is defined by the edges between vertices.) what is the time taken by your configuration? Consider again the same problem of adding n numbers. Assume that one person takes time te(n-1) to add these numbers. Is it possible for p people to add this list in time less than te(n-1)? Justify your answer.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


