Question: Build a file server from which a client can request files. Pick a programming language and investigate how to use its networking libraries. Conduct
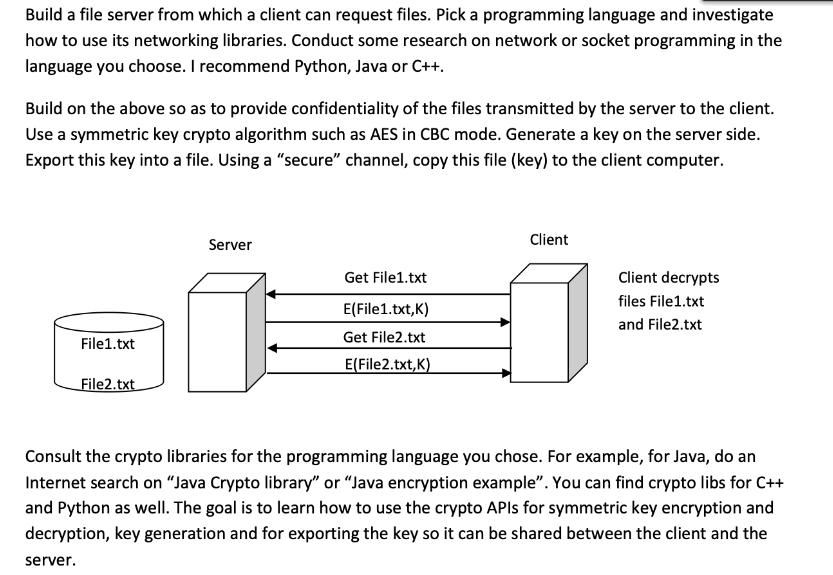
Build a file server from which a client can request files. Pick a programming language and investigate how to use its networking libraries. Conduct some research on network or socket programming in the language you choose. I recommend Python, Java or C++. Build on the above so as to provide confidentiality of the files transmitted by the server to the client. Use a symmetric key crypto algorithm such as AES in CBC mode. Generate a key on the server side. Export this key into a file. Using a "secure" channel, copy this file (key) to the client computer. File1.txt File2.txt Server Get File1.txt E(File1.txt,K) Get File2.txt E(File2.txt,K) Client Client decrypts files File1.txt and File2.txt Consult the crypto libraries for the programming language you chose. For example, for Java, do an Internet search on "Java Crypto library" or "Java encryption example". You can find crypto libs for C++ and Python as well. The goal is to learn how to use the crypto APIs for symmetric key encryption and decryption, key generation and for exporting the key so it can be shared between the client and the server.
Step by Step Solution
There are 3 Steps involved in it
We should have proper knowledge on how to use crypto APIs for symmetric key encryption and decryption next key generation and for exporting key so that it can be shared between client and server after ... View full answer

Get step-by-step solutions from verified subject matter experts


