Question: Can you help me solve this problem It for witeshark Network security Computer science elective I am doing it now as we speak untitled Implement
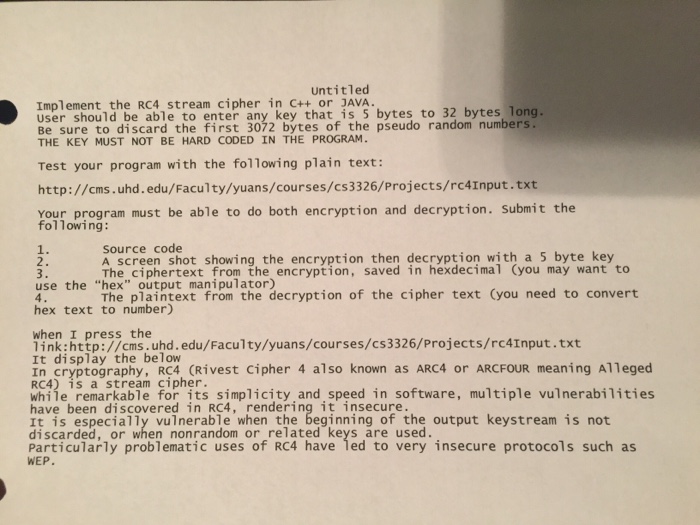
untitled Implement the RC4 stream cipher in C++ or JAVA. User should be able to enter any key that is 5 bytes to 32 bytes long. Be sure to discard the first 3072 bytes of the pseudo random numbers. THE KEY MUST NOT BE HARD CODED IN THE PROGRAM. Test your program with the following plain text: http://cms.uhd. edu/Faculty/yuans/courses/cs3326/projects/rc4Input.txt Your program must be able to do both encryption and decryption. Submit the following source code A screen shot showing, the encryption then decryption with a 5 byte key The ciphertext from the encryption, saved in hexdecimal Cyou may want to The plaintext from the decryption of the cipher text (you need to convert 1 use the "hex" output manipulator) hex text to number) I press the Thek: ht tr s cns.uhd.edu/Faculty link:http://cms.uhd.edu/Faculty/yuans/courses/cs3326/Projects/rc4Input.txt It display the below In cryptography, R4 CRivest cipher 4 also known as ARC4 or ARCFOUR meaning Alleged while remarkable for its simplicity and speed in software, multiple vulnerabilities Mi4e isemarkab e for s simplicity and speed in software, multiple vulnerabilities It is especially vulnerable when the beginning of the output keystream is not discarded, or when nonrandom or related keys are used. Particularly problematic uses of RC4 have led to very insecure protocols such as WEP
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


