Question: Can you please solve this in python? 2. Testing Encryption Validity Encryption is the process of converting information algorithmically so that only a valid recipient
Can you please solve this in python?
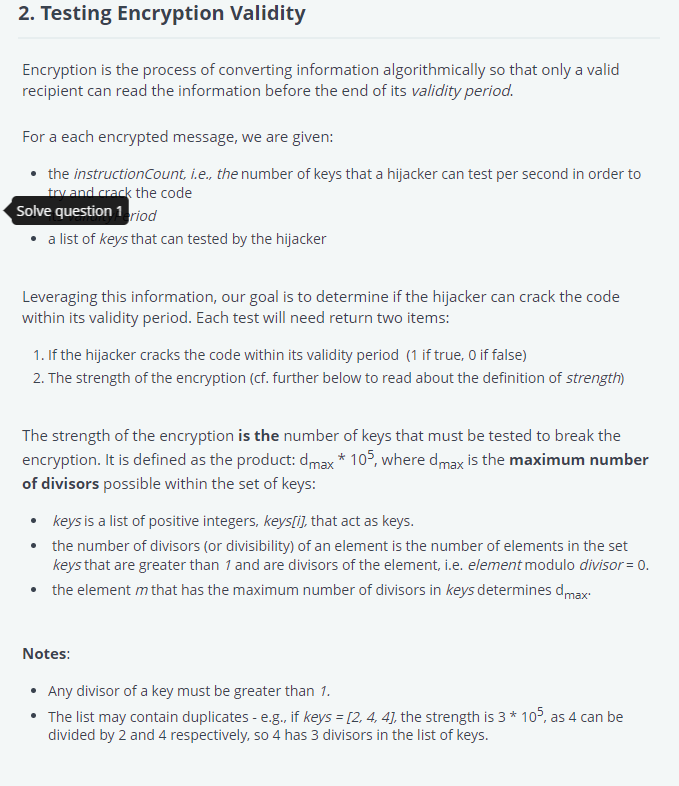
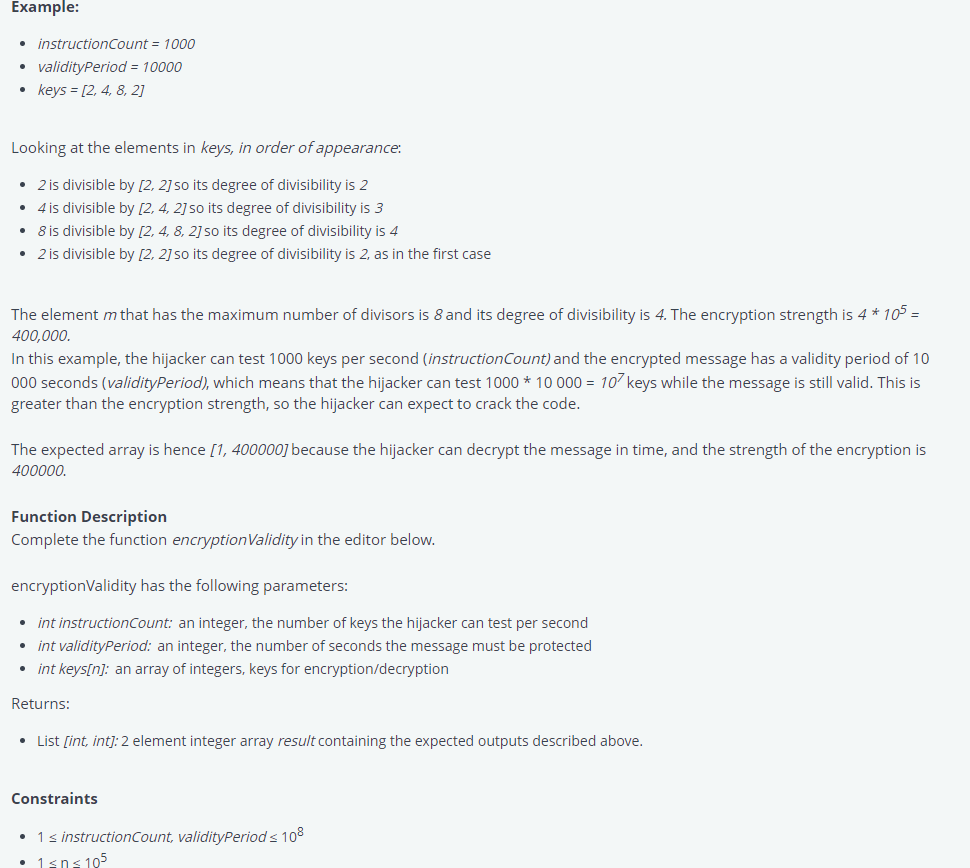
2. Testing Encryption Validity Encryption is the process of converting information algorithmically so that only a valid recipient can read the information before the end of its validity period. For a each encrypted message, we are given: the instructionCount, i.e., the number of keys that a hijacker can test per second in order to try and crack the code Solve question 1eriod a list of keys that can tested by the hijacker Leveraging this information, our goal is to determine if the hijacker can crack the code within its validity period. Each test will need return two items: 1. If the hijacker cracks the code within its validity period (1 if true, 0 if false) 2. The strength of the encryption (cf. further below to read about the definition of strength) The strength of the encryption is the number of keys that must be tested to break the encryption. It is defined as the product: dmax * 105, where dmax is the maximum number of divisors possible within the set of keys: keys is a list of positive integers, keys[i], that act as keys. the number of divisors (or divisibility) of an element is the number of elements in the set keys that are greater than 1 and are divisors of the element, i.e. element modulo divisor = 0. the element m that has the maximum number of divisors in keys determines dmax Notes: Any divisor of a key must be greater than 1. The list may contain duplicates - e.g., if keys = [2, 4, 4], the strength is 3 * 105, as 4 can be divided by 2 and 4 respectively, so 4 has 3 divisors in the list of keys.
Step by Step Solution
3.48 Rating (158 Votes )
There are 3 Steps involved in it
def cancrackcodeinstructionCount keys validityPeriod Find the maximum number ... View full answer

Get step-by-step solutions from verified subject matter experts


