Question: Click to select the wireless encryption methods, and then drag them into the correct order from most to least secure. Wireless encryption methods 1
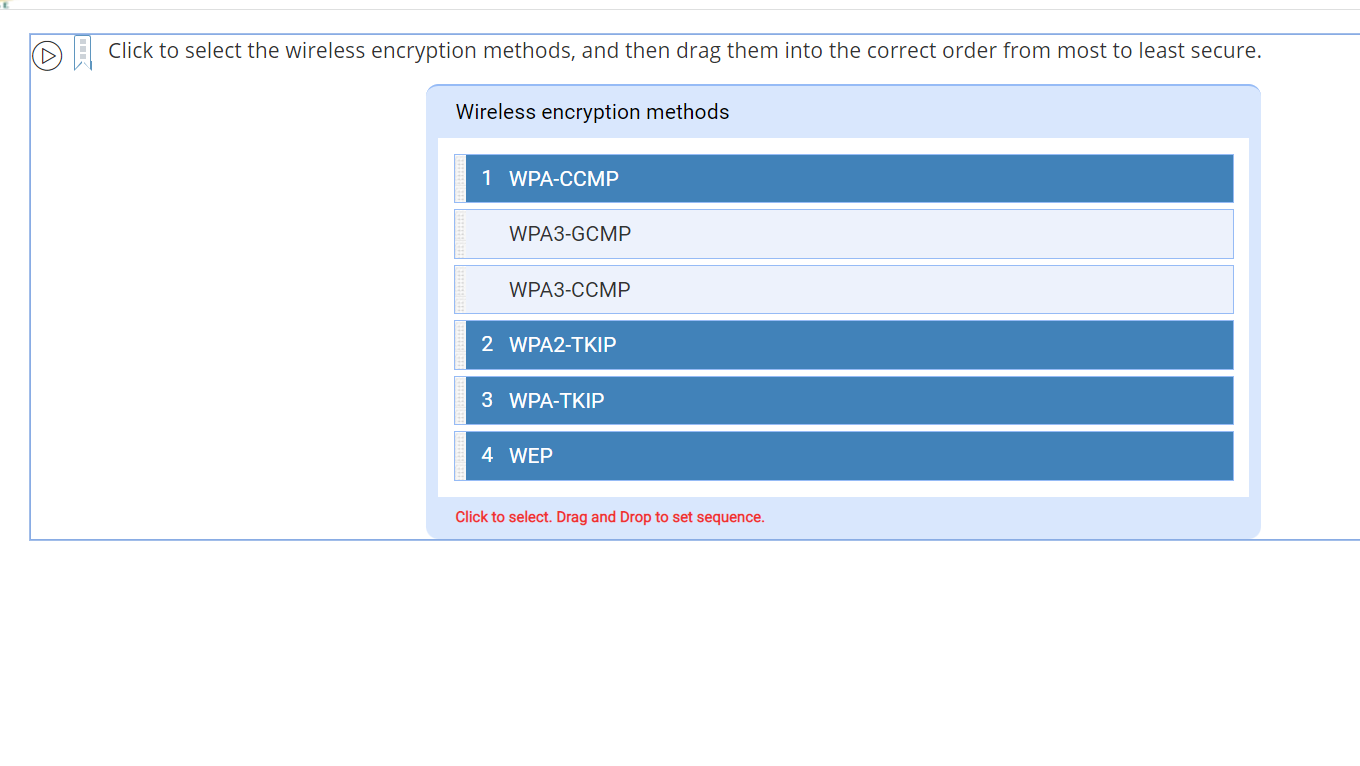
Click to select the wireless encryption methods, and then drag them into the correct order from most to least secure. Wireless encryption methods 1 WPA-CCMP WPA3-GCMP WPA3-CCMP 2 WPA2-TKIP 3 WPA-TKIP 4 WEP Click to select. Drag and Drop to set sequence.
Step by Step Solution
3.43 Rating (162 Votes )
There are 3 Steps involved in it
The most to least secure wireless encryption methods are While making choice ... View full answer

Get step-by-step solutions from verified subject matter experts


